Hard drives and SSDs are easy to remove from laptops or computers. In such a case, all of the security measures implemented by your operating system go out the window. If you have data you want to protect, you can create an encrypted container. You would store sensitive files there, while storing non-secretive files on your regular partitions.
It’s easiest to set up an encrypted partition when you install your Linux distribution. The installer can guide you through that. But if you missed that opportunity, follow the steps in this guide to create your secret vault.
Also read: How to Encrypt Files on Linux Using GPG, Ccrypt, Bcrypt and 7-Zip
Prerequisites
You need an empty partition for this process. This means one that is unformatted (no filesystem on it).
If your formatted partitions currently occupy all the free space on your storage device, you will need to use GParted to shrink one of them.
Warning: It’s wise to back up your data first. When you shrink a partition and its filesystem, there is a small amount of risk involved. Your computer may crash or lose power during the process. This could leave your filesystem in an inconsistent state that may be hard to recover from.
Follow the first steps in this guide to resize a partition with GParted. Or, if there is a partition you don’t need anymore, you can delete it. (After you free up some space and it shows up as “unallocated,” skip the rest of the steps from the guide.) Specifically, don’t create a partition formatted as ext4. Instead, right click on the unallocated space, as shown in the guide. In the dialog window that opens, you will see a field labeled “File system.” Normally, ext4 should be selected as default here. Click on it and change it to “cleared.”
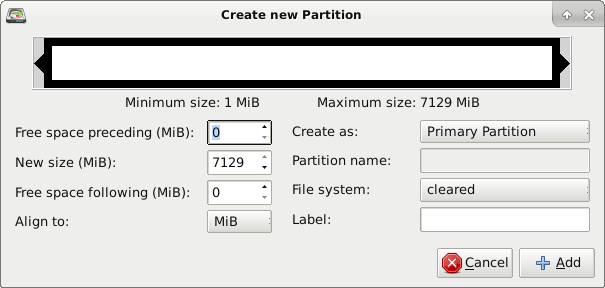
After you select “Add,” click on the green checkmark to apply the changes.
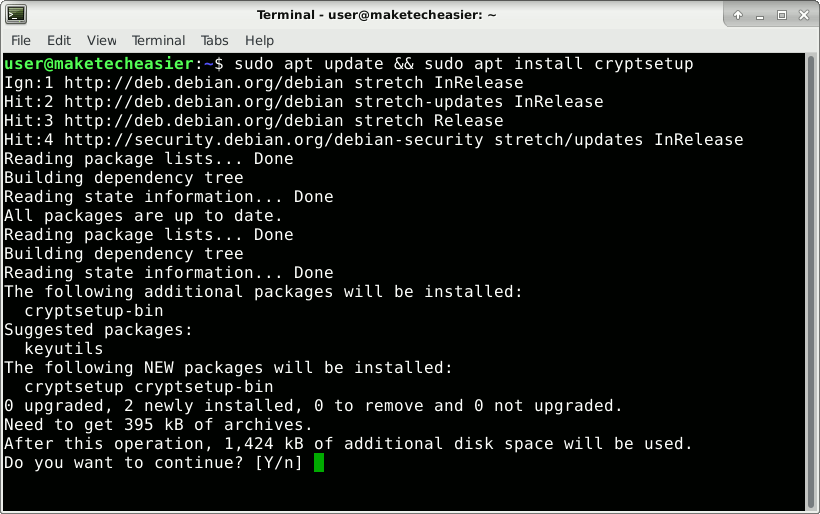
Install cryptsetup
If you’ve booted a live operating system to edit your partitions with GParted, reboot back into your main Linux distribution.
Open a terminal emulator. On Debian-based systems, such as Ubuntu or Linux Mint, enter this command:
sudo apt update && sudo apt install cryptsetup
On distributions such as Fedora or CentOS and others that use RPM packages instead of DEB, cryptsetup may already be installed. If not, you can install it with:
sudo yum install cryptsetup
On OpenSUSE, if cryptsetup isn’t preinstalled, you can install it with:
sudo zypper refresh && sudo zypper install cryptsetup
And on Arch-based distributions, you would use this command:
sudo pacman -S cryptsetup
Find the Block Device Name of Your Partition
Enter the following command:
lsblk
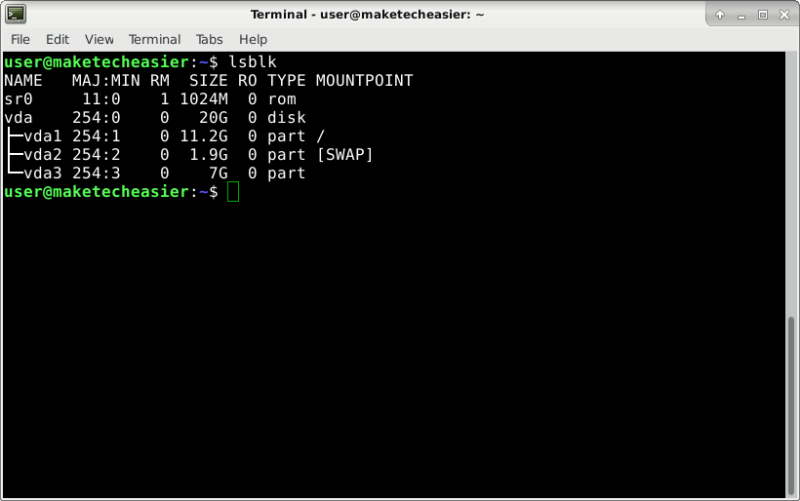
In the example offered in the picture, the storage device is “vda.” “vda1” to “vda3” are partitions.
To find the partition you have prepared, remember the size you reserved for it. You will find it among the partitions with no mountpoints. In your case this might be something like “/dev/sda2” instead of “/dev/vda3.”
Encrypting the partition will overwrite data on it (if present), which means if you get the device name wrong, you could end up destroying useful data. To make sure you get the device name right, you can install GParted and take a look at your partition layout. The device names will be listed in the graphical user interface. Don’t use the name you saw in GParted when you booted from the live system (if you did). The layout shown in the live system will be different from the layout you see when booting from your installed distribution.
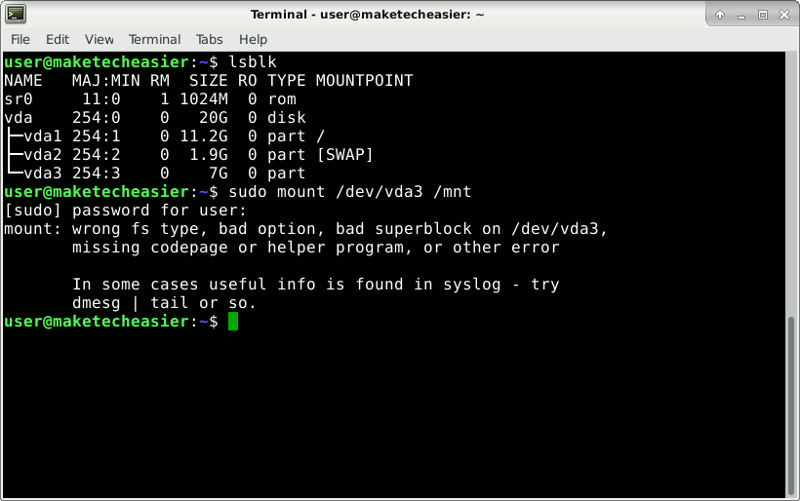
There is another way to make sure you don’t write on the wrong block device. Try to mount it. Normally, it should refuse to do so since it doesn’t have a filesystem on it.
Important: remember to always replace “vda3” with the name of your device:
sudo mount /dev/vda3 /mnt
In your case, the command might be sudo mount /dev/sda2 /mnt or something else.
This is the message you should get.
Set Up LUKS Header
Once you’re certain you have the right device name, add a LUKS header to the partition.
sudo cryptsetup luksFormat /dev/vda3
Type “YES” and then choose a strong password for your encrypted partition. Type the same password when asked to verify the passphrase.
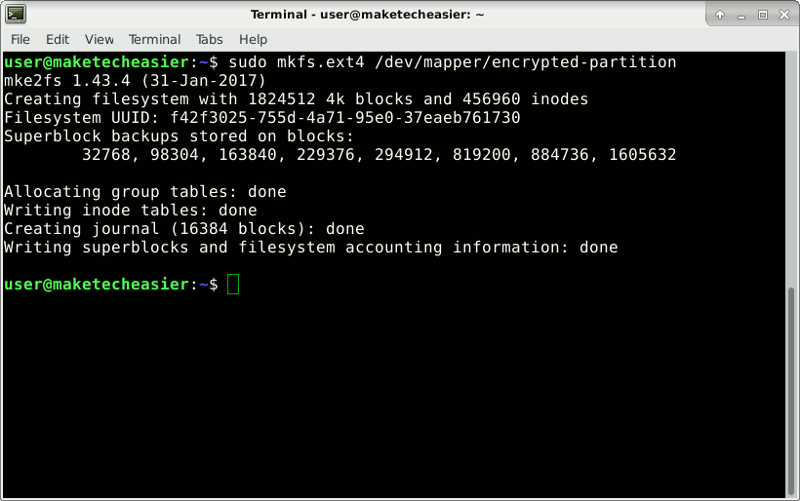
Create a Filesystem on the Partition
You have to map this physical device to a virtual device. What gets written to the virtual device will be encrypted before being stored on the physical device.
sudo cryptsetup luksOpen /dev/vda3 encrypted-partition
The partition needs a filesystem to be usable. Create an ext4 filesystem with this command:
sudo mkfs.ext4 /dev/mapper/encrypted-partition
Mount Encrypted Partition
Create the directory where you will mount the filesystem from the partition.
mkdir ~/encrypted-storage
Mount the filesystem:
sudo mount /dev/mapper/encrypted-partition ~/encrypted-storage
Change to that directory:
cd ~/encrypted-storage
At the moment, only the root user can write here. Give your user permission to write in this filesystem by making it the owner of the upper level directory. Copy and paste the whole command, including the “.” at the end.
sudo chown $USER:$USER .
Restrict other users from reading or writing to this directory.
chmod o= .
At this point, most file managers should show you the new encrypted device in the interface. This shows how it looks in the Thunar file manager, the default used in the XFCE desktop environment.
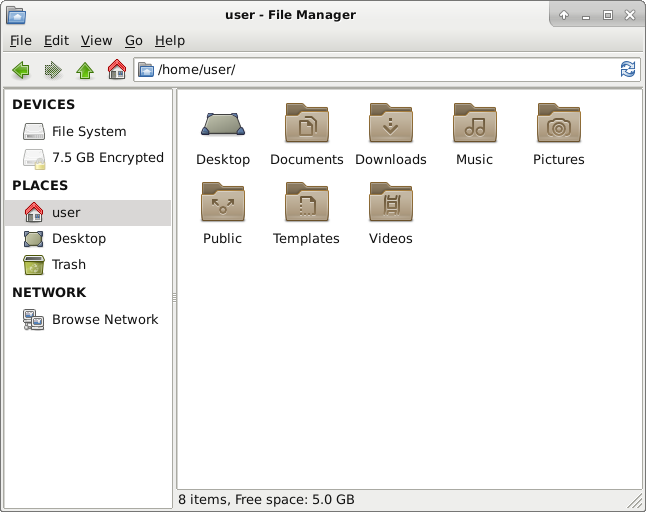
If the volume is not mounted, when you click on it you will be asked for the volume password and your sudo password. The volume will be mounted automatically, and you will be able to browse it. The mountpoint will be different from “~/encrypted-storage.” It could be something like “/media/user/f42f3025-755d-4a71-95e0-37eaeb761730/,”
That is unimportant; permissions you set earlier still apply. What is important is to remember to right-click it and unmount when you finish working with the volume. Unmounting and closing the virtual device guarantees that no one can read the data from the encrypted partition, not even your operating system.
If, for some reason, your file manager doesn’t support this feature, you can mount from the terminal.
sudo cryptsetup luksOpen /dev/vda3 encrypted-partition sudo mount /dev/mapper/encrypted-partition ~/encrypted-storage
You can now access the volume by going to “/home/username/encrypted-storage” in the file manager. When you’re done, unmount the filesystem and close the virtual device:
cd && sudo umount /dev/mapper/encrypted-partition sudo cryptsetup luksClose /dev/mapper/encrypted-partition
Conclusion
You now have a safe for your important files. Knowing that no one can see what you store there should give you some peace of mind.








