Encryption is almost a necessity now that security and privacy standards are not strictly adhered to by companies anymore. If you are really concerned about the security of your data that you stored in the cloud, and you really need to store it in the cloud, it is best to encrypt it first before you upload it to the cloud.
Gocryptfs is an encrypted overlay filesystem written in Go and is built on top of the go-fuse FUSE library. Unlike full-disk encryption systems, gocryptfs encrypts files individually using chunked AES-GCM (Galois Counter Mode) and encrypts filenames with AES-EME (ECB-Mix-ECB). It is also cross-platform compatible, which means you can access your files on any platform.
In this tutorial we will show you how to make use of Gocryptfs to encrypt files.
Installation
Linux
Gocryptfs comes with a deb package and is available in the repository of Debian and Ubuntu, which means you can easily install it with the command:
sudo apt install gocryptfs
The same applies to Arch Linux. You can install gocryptfs via Pacman:
sudo pacman -S gocryptfs
For other Linux distros, you can download the binary file from its Github site.
Mac
To use gocryptfs in macOS, you have to install Homebrew first:
/usr/bin/ruby -e "$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)"
Then use the following command to install gocryptfs:
brew install gocryptfs
Windows
Gocryptfs is not natively supported in Windows due to its lack of support for FUSE. However, cppcryptfs is an implementation of the gocryptfs encrypted overlay filesystem in C++ for Windows, so you can still get it to work in Windows. Follow the build instruction here.
Using gocryptfs to encrypt files
To start using gocryptfs, you need to first create two empty folders:
mkdir encrypted plain
Next, initialize gocryptfs:
gocryptfs -init encrypted
Lastly, mount the “encrypted” folder to the “plain” folder:
gocryptfs encrypted plain
Now, any files you place in the “plain” folder will be encrypted and stored in the “encrypted” folder.
As an example, if you want to store the encrypted file in Dropbox and mount it to a “Private” folder in the Home directory, you can run the following commands:
cd mkdir ~/Dropbox/encrypted ~/Private gocryptfs -init ~/Dropbox/encrypted gorcypted ~/Dropbox/encrypted ~/Private
Every file you place in the Private folder will be encrypted in the “Encrypted” folder and uploaded to the Dropbox server.
SiriKali – a GUI tool for using gocryptfs
SiriKali is a GUI tool that can be used for encrypting with gocryptfs and other standards. It is available for Linux, macOS and Windows, though the Windows version don’t have support for gocryptfs.
1. Go to the SiriKali website, and download the package suitable for your system. The Linux package offers the source which you can extract and build. It also is available with its own repository for a variety of distributions and can be found here.
2. On Ubuntu, run the following within the Terminal:
sudo sh -c "echo 'deb http://download.opensuse.org/repositories/home:/obs_mhogomchungu/xUbuntu_18.04/ /' > /etc/apt/sources.list.d/home:obs_mhogomchungu.list"
Once the commands have finished, it is a good idea to run this to “trust” the key and allow updates.
wget -nv https://download.opensuse.org/repositories/home:obs_mhogomchungu/xUbuntu_18.10/Release.key -O Release.key sudo apt-key add -3. Now you should find that SiriKali is installed and available within your menu. Click to open.
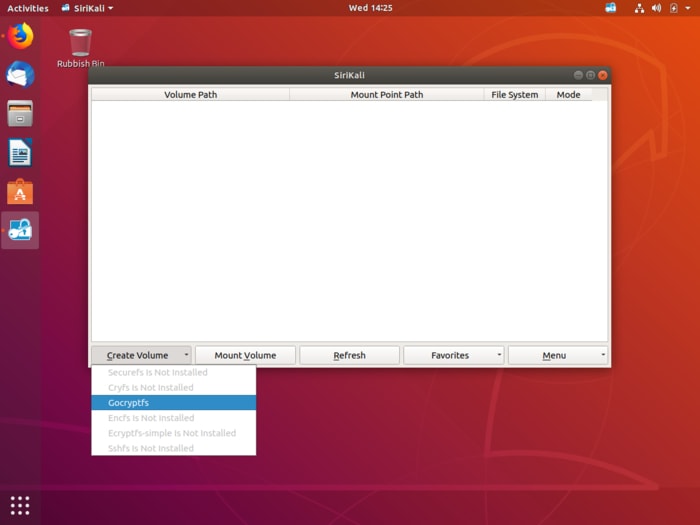
4. SiriKali opens a window that is reminiscent of VeraCrypt with options at the bottom of the screen. You can Create Volume, Mount Volume, Refresh, Manage Favorites and finally, there is a Menu.
5. Now you can click on Gocryptfs and create a volume.
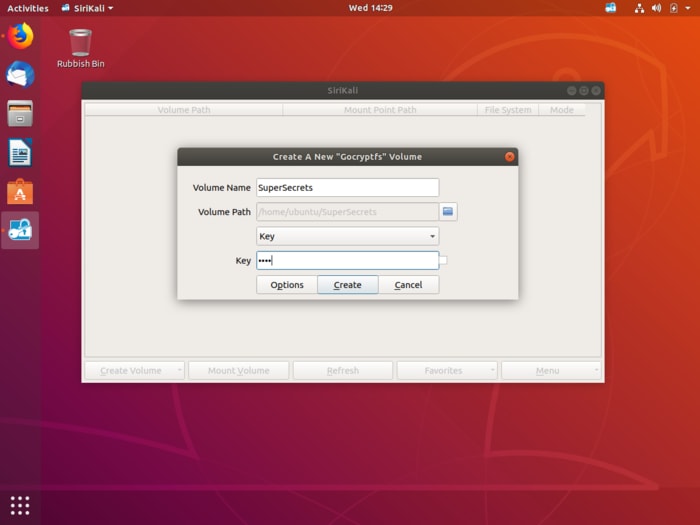
6. Call the volume whatever you would like, and the Key represents the password. There are different options such as password, password and key file, and the GNOME Wallet. Select which suits your needs – just remember to use a password that isn’t easily guessed.
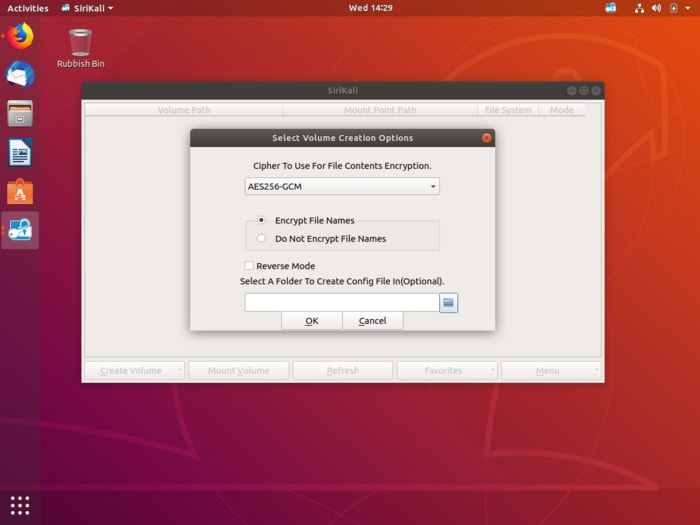
There are further variables under the options button which details the encryption level and if you need file names scrambled.
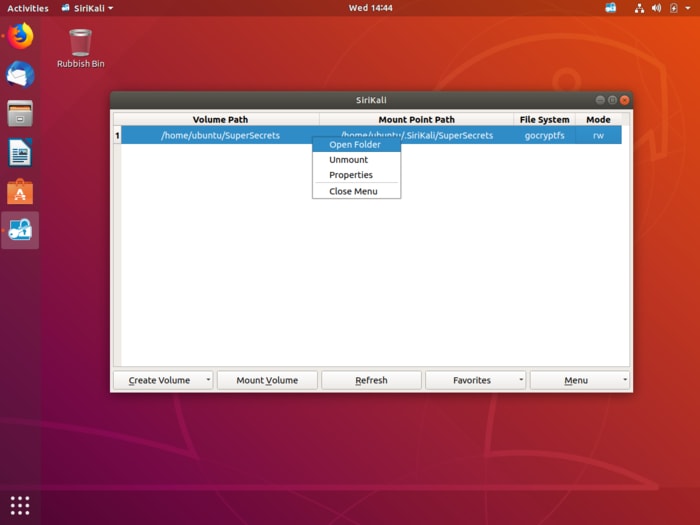
7. Once done, the newly created folder will appear in the SiriKali application. Click on this to open your folder where you can copy over the files you want to encrypt, just as you would any other for any other file copy action.
8. When you have finished, remember to click again and select “unmount volume.”
Which level of encryption do you use? Do you keep your data open so anyone can access it, or do you keep it locked down? Let us know in the comments section, along with any knowledge you have of better alternatives.