Tomb is a simple shell script that allows you to encrypt files in Linux. Unlike full disk encryption, Tomb enables you to only include the files and folders that you want to encrypt. Here we show you how to install and use Tomb on Ubuntu.
Why Use Tomb to Encrypt Files in Linux
One of the biggest advantages of Tomb is that it does not require any additional software to install and use. This means that it is possible to use it in an existing system without any internet connection. This can be helpful in situations where you want to quickly encrypt a file in live systems such as Kali Linux.
Tomb heavily relies on programs and utilities that come by default in most popular Linux distributions. For example, Tomb uses both GNU Privacy Guard to handle its encryption and dd to wipe and format its virtual partitions.
This means that Tomb will always use the latest encryption and programming techniques when maintaining its files. This approach also allows the program to focus on integrating itself to your system rather than create its own environment. As a result, you can easily adapt Tomb and its files to work with any custom shell script that you made in your machine.
Lastly, a Tomb file is also highly flexible. It allows you to seamlessly modify its properties without affecting its contents. Because of that, you can also use it as a simple encrypted backup storage.
Installing Tomb in Ubuntu
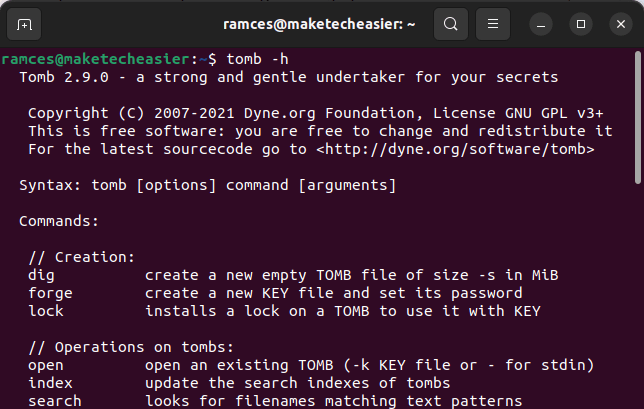
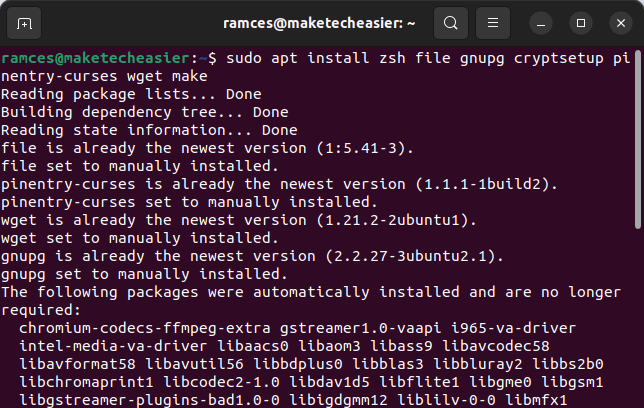
- Make sure that all of Tomb’s dependencies are present in your system. You can double check this by running the following command:
sudo apt install zsh file gnupg cryptsetup pinentry-curses wget make steghide mlocate
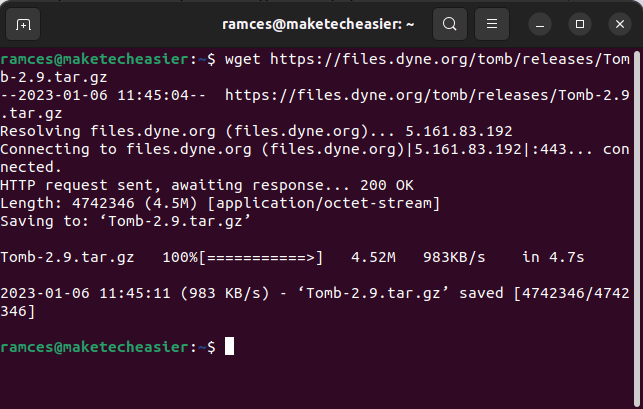
- Download a copy of Tomb from the developer’s website:
wget https://files.dyne.org/tomb/releases/Tomb-2.9.tar.gz
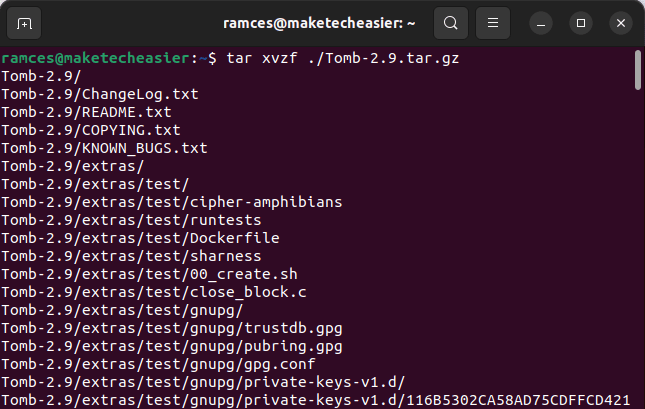
- Unpack the Tomb utility to your home directory. You can do this by running the following command:
tar xvzf ./Tomb-2.9.tar.gz
- Go inside the Tomb directory and install it to your system using
make:
cd Tomb-2.9 sudo make install
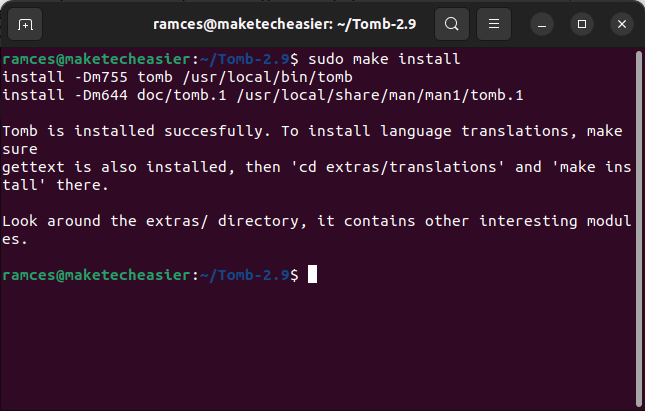
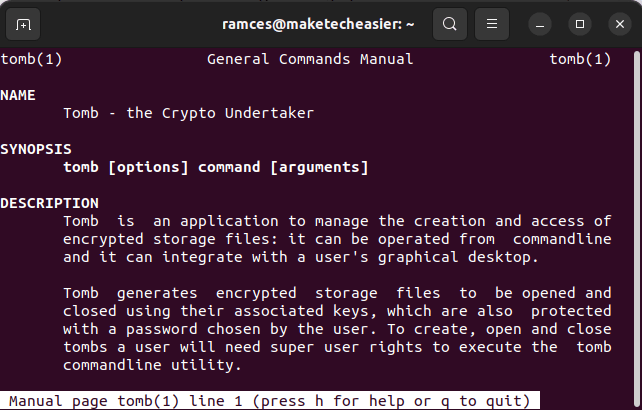
This command will automatically copy Tomb to “/usr/local/bin” and set the correct permissions for it to work. You can also check whether you have properly installed the program by running man tomb.
Creating Your First Tomb to Encrypt Files
With the program installed, you can start to use Tomb to encrypt file. Tomb works by allocating a set amount of space that it will encrypt beforehand. You can copy your files to this space later and Tomb will encrypt them on the fly.
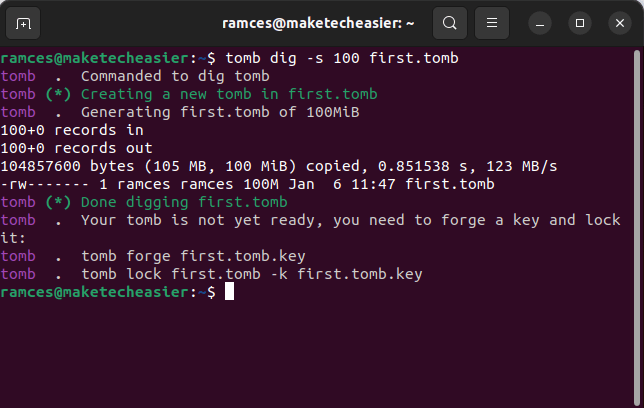
To allocate the space for your first Tomb, you need to use the dig subcommand. The following command creates a 100MB Tomb file with the name “first.tomb.”
tomb dig -s 100 first.tomb
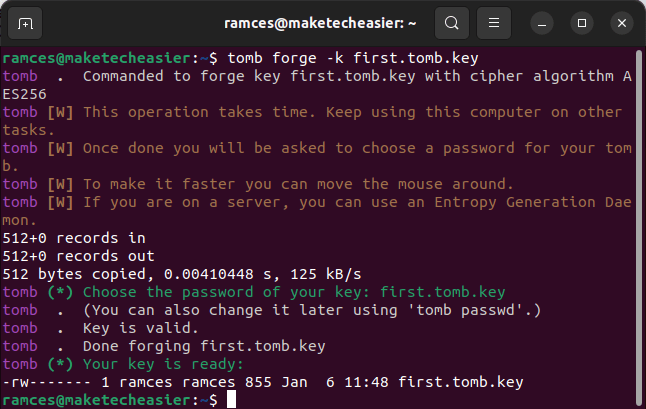
Next, you need to create a key for your new tomb file:
tomb forge -k first.tomb.key
It is important to note that running this command can be resource intensive to your machine. This is because the forge subcommand tries to generate as much random data as possible for its keys. You can alleviate this issue by constantly moving the mouse cursor during this process.
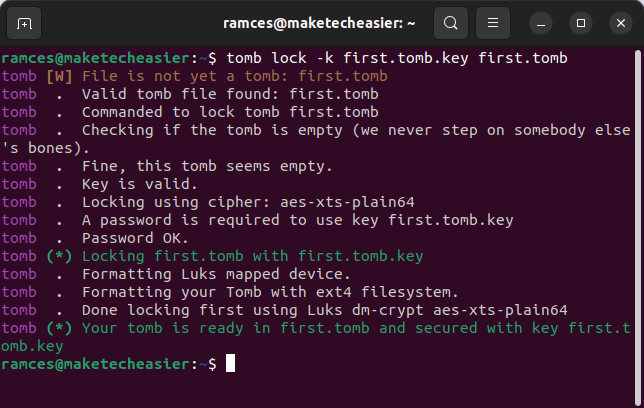
Once you have your key, you can now link it to your new tomb file. To do this, you can run the lock subcommand:
tomb lock -k first.tomb.key first.tomb
Lastly, you can open your newly locked tomb by running the open subcommand:
tomb open -k first.tomb.key first.tomb
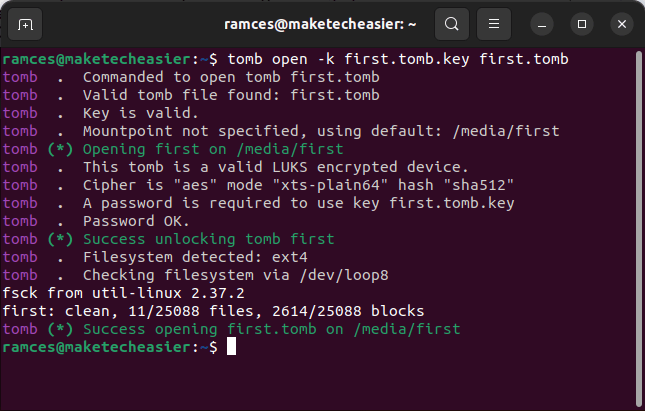
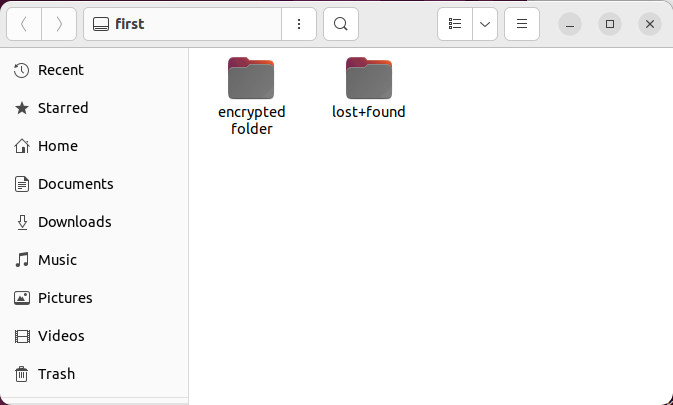
Running this command will prompt you for your Tomb’s password (in case you can’t remember your password, check out these password managers for Linux). After which, it will then automatically mount your file as a separate partition in your system.
Creating an Image Key to Encrypt Files
Aside from creating simple password keys, you can also use images to unlock your tomb files. This can be helpful if you want to share your tomb to others without directly sharing your password.
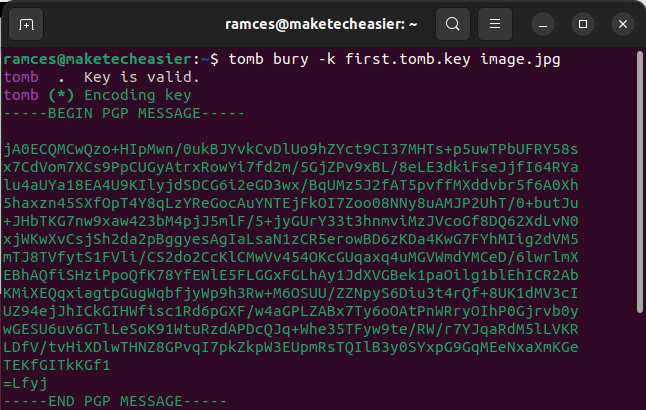
To create an image key, you need to use the bury subcommand. For example, running the following command will combine my “first.tomb.key” file with my “image.jpg” file.
tomb bury -k first.tomb.key image.jpg
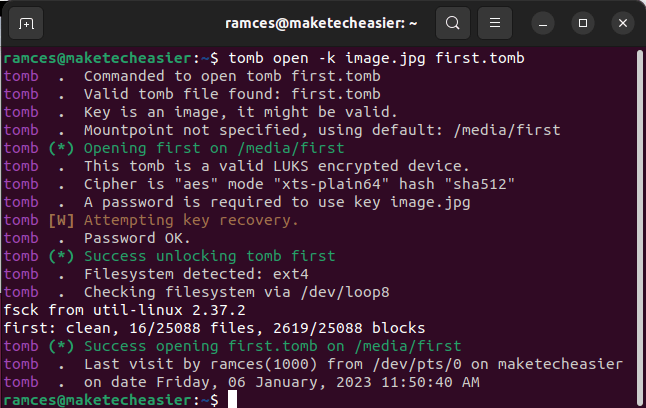
Once that is done, you can now use your image to open the tomb file. The following command opens the “first.tomb” file using my new image key.
tomb open -k image.jpg first.tomb
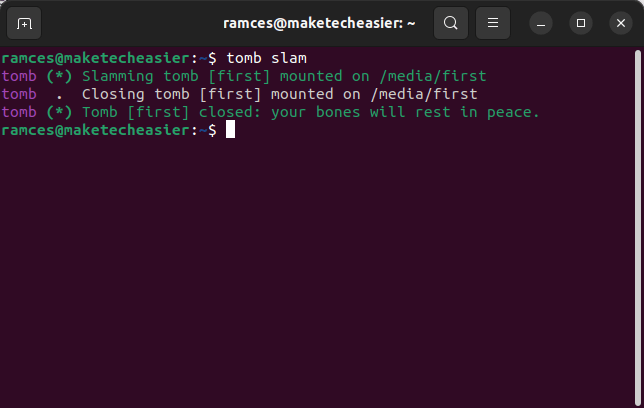
Closing and Slamming Your Tomb
Unlike a regular encrypted drive, a Tomb file does not work as a separate device in your system. Instead, it behaves as an isolated partition within your file system.
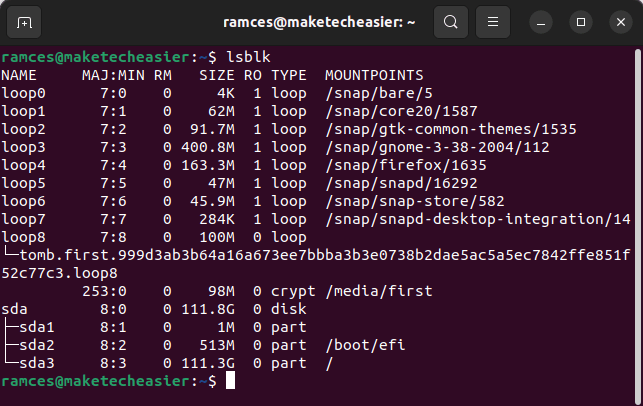
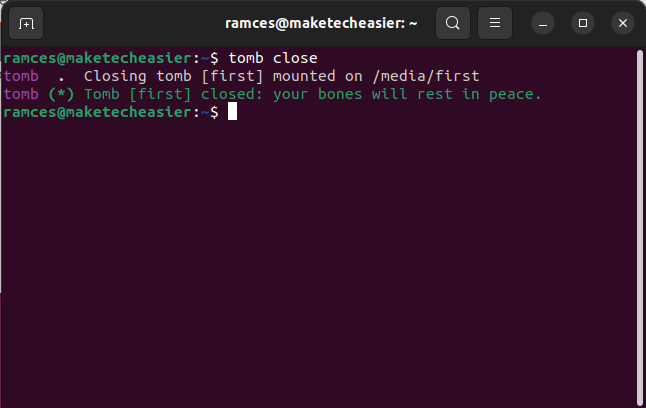
One issue with this approach is that you need to use program-specific subcommands to cleanly unmount tombs. For example, running the following command will reencrypt a tomb’s contents and cleanly unmount it from your current session:
tomb close
Aside from that, you can also force close any mounted tombs in your system. This is useful if you have a misbehaving application that does not want to terminate.
However, it is important to note that forcing an unmount can potentially damage the data inside your tombs. Knowing that, you can do a force close by running the slam subcommand:
tomb slam
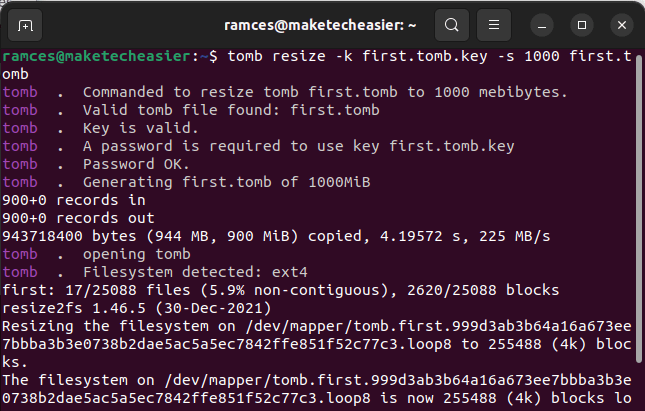
Expanding and Indexing Your Tomb
It is also possible to increase the amount of storage for your tomb files. This can be helpful for users that wanted to store more data but do not want to encrypt a new partition for their data.
To do this, you need to use the resize subcommand. For example, running the following command will expand the size of my first.tomb file from 100MB to 1GB:
tomb resize -k first.tomb.key -s 1000 first.tomb
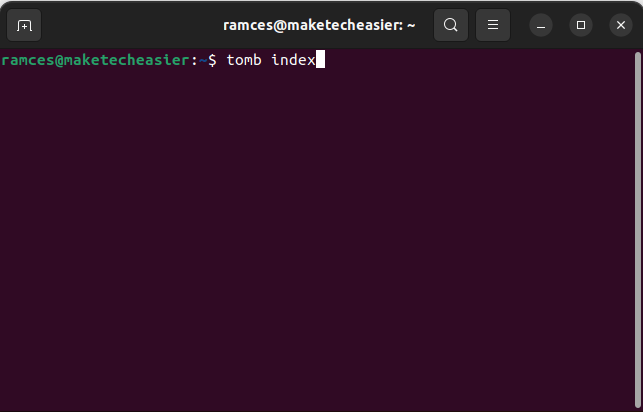
Searching Your Tombs
Lastly, you can also create easily searchable indexes for your currently open tomb files. This is useful for users that want to have a quick way to manage multiple encrypted partitions.
In order to search through your tomb files, you need to first build an index of it. To do this, you need to run the following command:
tomb index
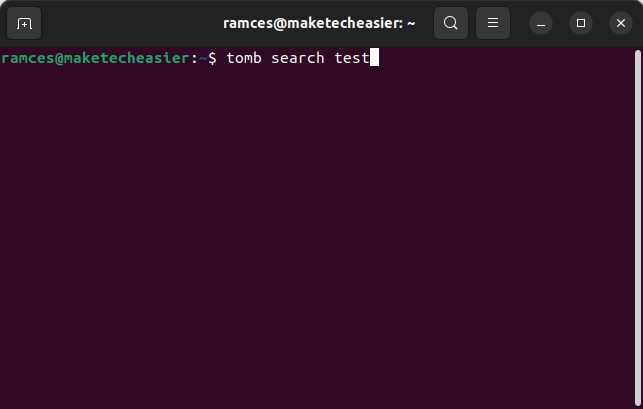
Next, you can now search through all of the currently open tomb files by running the search subcommand. For example, running the following will look for every file that contains the word “test”:
tomb search test
Frequently Asked Questions
Can you use Tomb on a different Linux distribution?
Tomb is a highly portable script that only relies on a small set of Linux utilities. This means that it is likely that the program will run on your machine as long as you have the right dependencies. For example, both zsh and GNU Privacy Guard are programs that are often present in any distribution repository.
Can you link a single key to multiple tombs?
Yes. Similar to publishing an SSH key pair, it is possible to use a single key to manage multiple tomb files. To do this, you need to create your new file by running: tomb dig -s 100 test2.tomb.
Next, you need to link your new tomb file by using the lock subcommand. For example, running the following will link my new test2.tomb to my existing test.tomb.key: tomb lock test2.tomb -k test.tomb.key.
Is it possible to reduce the size of a tomb file in Linux?
No. The developers of Tomb designed their encrypted filesystems to only grow in size. This is mostly due to the way both the encryption and resizing works between cryptsetup and resize2fs.
The only way to “shrink” a tomb file is to create a new tomb with a smaller size using the dig subcommand. After that, you can link this new tomb file to your existing key using the lock subcommand.
Image credit: Unsplash. All screenshots and alterations by Ramces Red.








