Gmail now allows you to send private emails. You will be able to add more security to your email so that only the intended recipient will be able to read it. Every time you write a new message, you will see an option to make your email more secure with just one click. It’s easy to learn how to encrypt email in Gmail, so if you’re not very tech-savvy, it shouldn’t be much of an issue. Hopefully, it will make you feel more secure when sending an email.
Worried you might get hacked? Protect your Gmail account before it’s too late.
How to Send Private Email in Gmail on PC
According to estimates, Gmail currently has more than 1.8 billion active users. That is many, many emails traversing the globe between users and a lot of unprotected data – Gmail only uses TLS (transport layer security) to encrypt its emails. This leaves chinks in the armor, through, which allows hackers access to your precious data. Follow these steps to encrypt your email using Confidential Mode:
- Log in to your Gmail account.
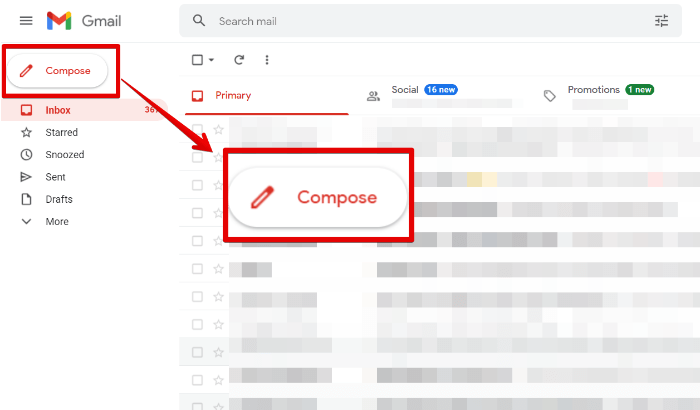
- Click on the “Compose” button on the left side of the window.
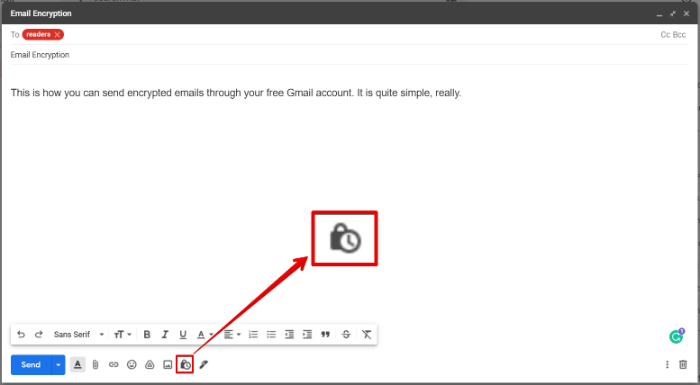
- Create an email as you usually would, then click on the lock icon at the bottom of the window.
- Configure encryption settings, duration, etc., and select the expiry date for the mail you are sending. Recipients cannot interact with email past the expiry date. Furthermore, you can send the recipient a passcode via SMS for added security.
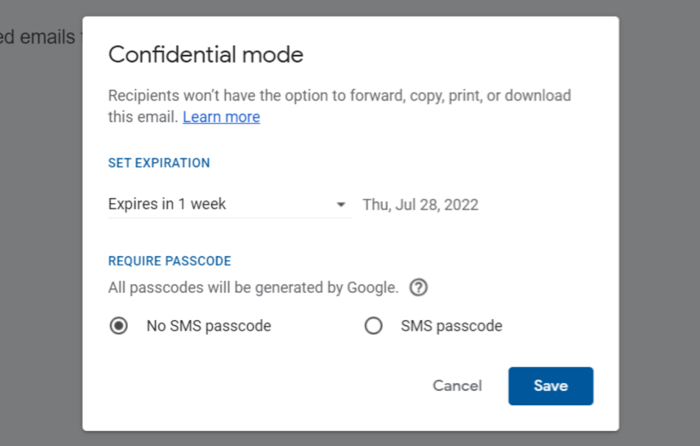
- Send the mail when you’re ready and include an SMS passcode, if desired.
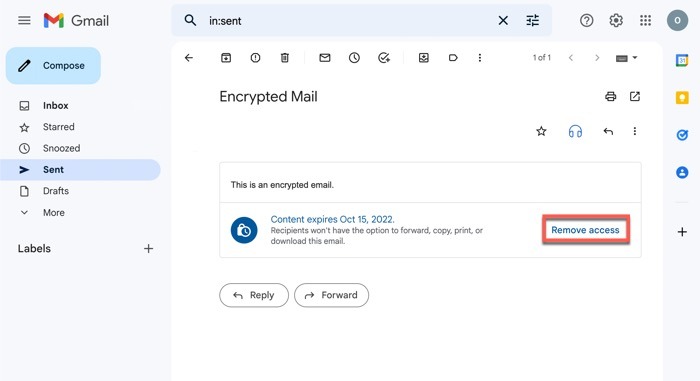
- Revoke access to an encrypted email by opening the email from the “Sent” folder and clicking “Remove access.”
Tip: get acquainted with Gmail automation with these useful Google scripts.
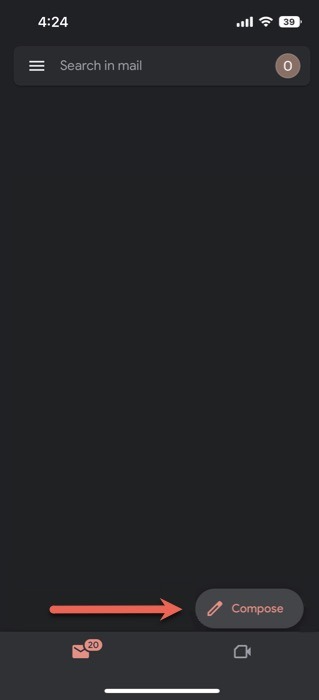
How to Send Private Email in Gmail App
- Launch the Gmail App, and click on the “Compose” button.
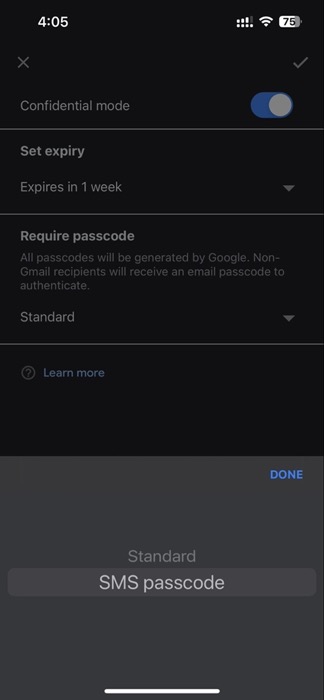
- Click on the three dots in the top-left corner of the mail composition window, and select “Confidential mode.”
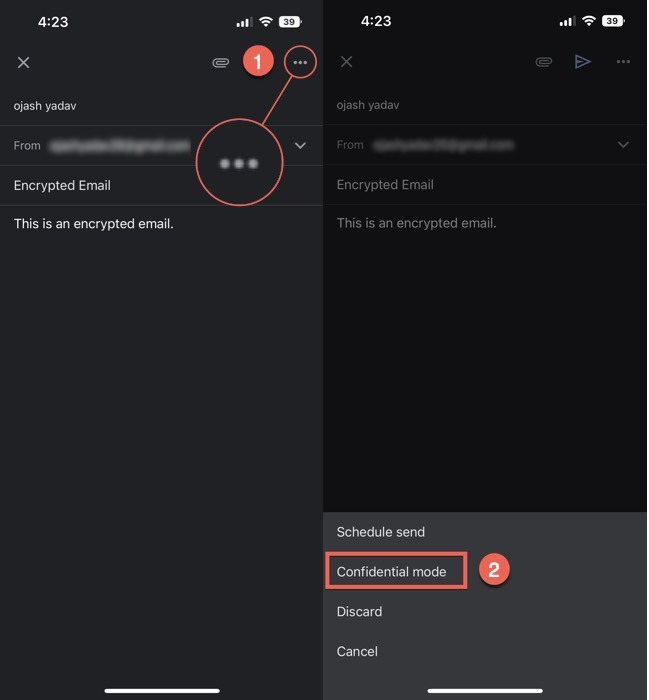
- Set the expiry date of the email by tapping on the drop-down arrow in the “Set expiry” section.
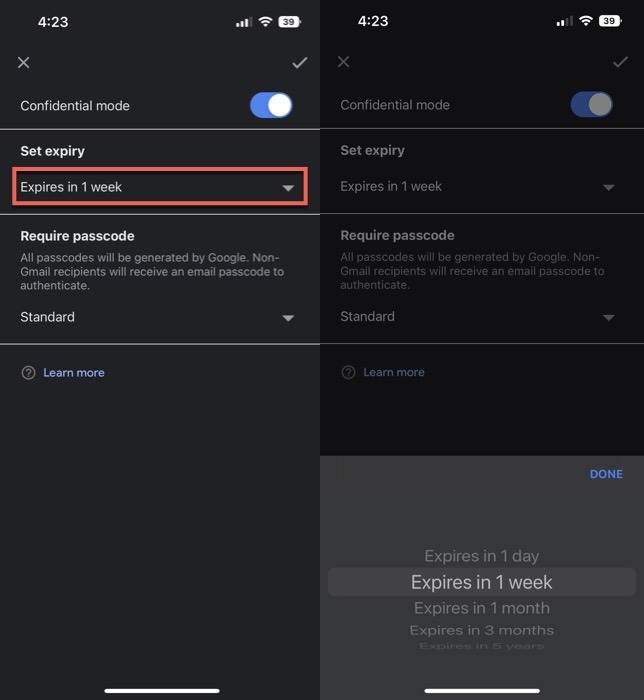
- As with the web client, you can choose to set a passcode for your encrypted mail using the Gmail app.
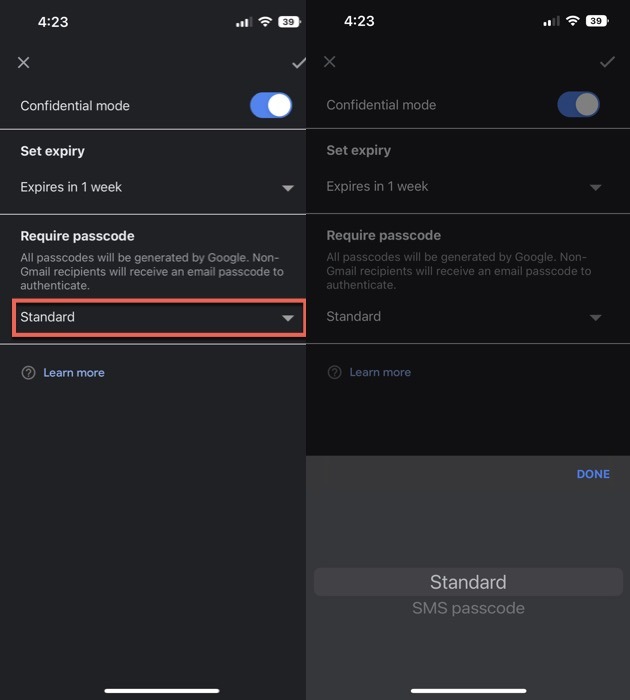
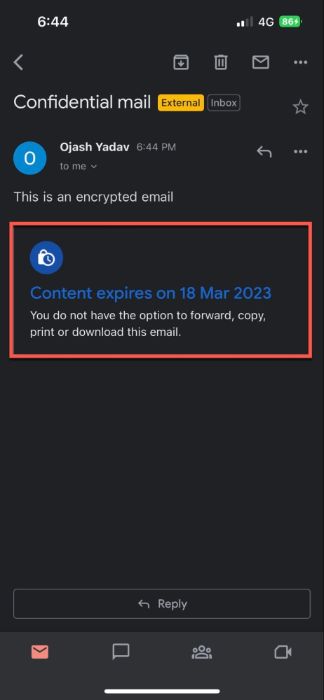
- After you’ve set things up, you will see a dialog box showing an expiry date, confirming that the mail is encrypted. Hit the “Send” button, and your encrypted mail will be delivered to the recipient.
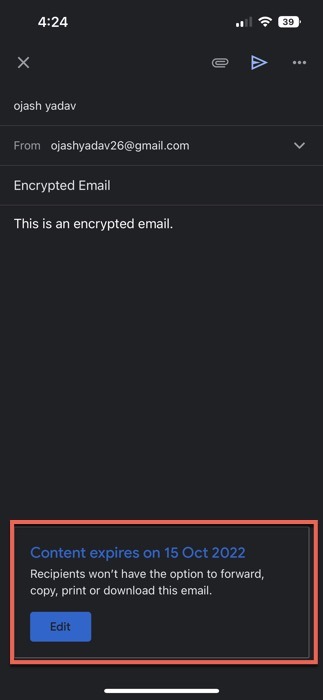
- Revoke access to an encrypted email on the app by pressing the hamburger menu in the left corner and navigating to the “Sent” folder.
- Click on the “Remove access” button in the email.
- If you want to add an extra layer of security to your encrypted email, you can also add the SMS passcode option.
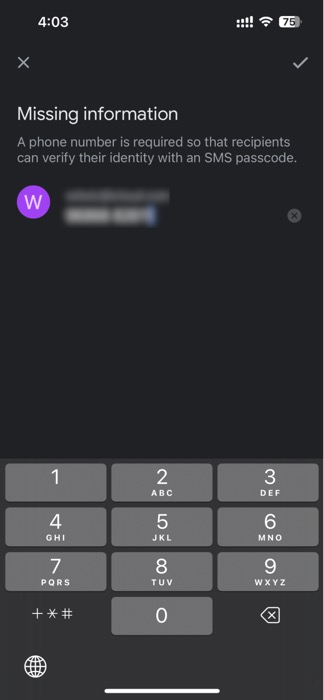
- If the recipient of the email is IN your contact list, and their phone number is saved to your account, Google will automatically link it to the email. If not, you’ll see a pop-up asking you to add the phone number when you hit “Send.”
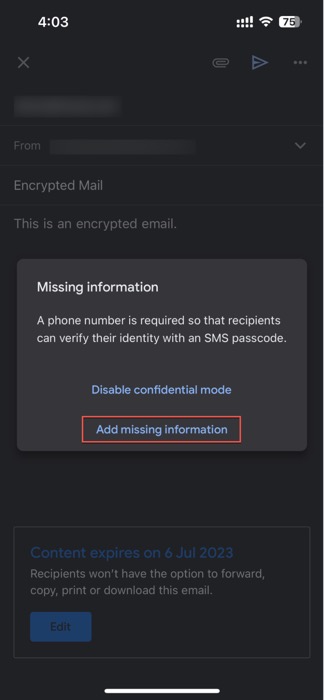
- When you add the recipient’s phone number, they can receive an SMS code for verification.
FYI: learn how to set up automatic forwarding in Gmail by reading our guide on the matter.
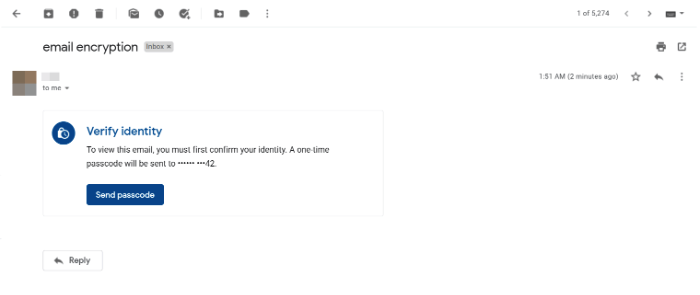
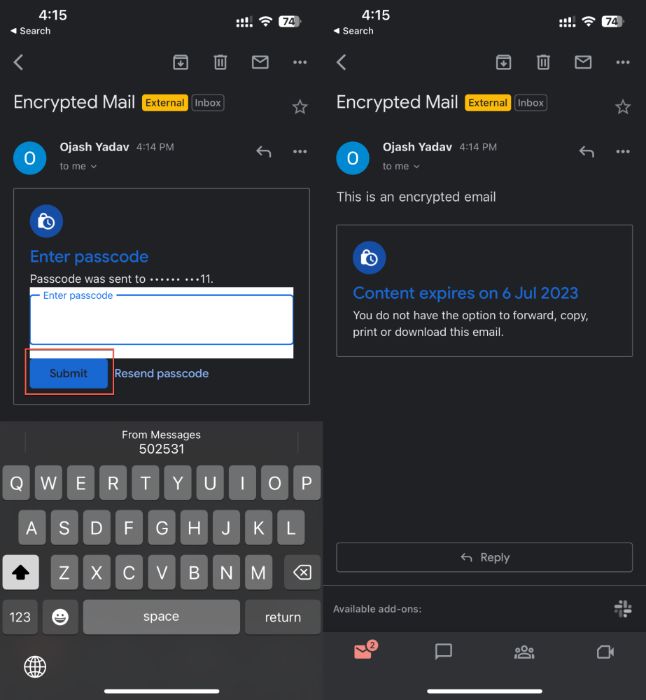
How to Open an Email Sent with Confidential Mode
If you have received an email sent with Confidential Mode in Gmail, follow these steps to open and read it:
From a Gmail Account
- Open the email in your Gmail inbox.
- If the sender has selected “Standard” encryption, you can view the email the same as any other email. However, you’ll see a content expiry notification below the email content.
- If the sender has used the SMS verification method, you’ll be asked to get an SMS on your phone number to verify your identity. Click on “Send passcode.”
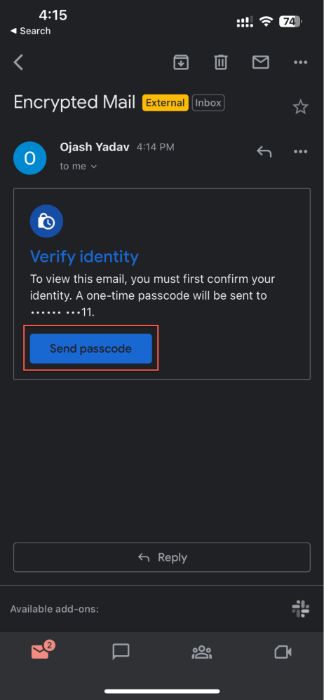
- Enter the passcode you received, and click “Submit” to unlock your encrypted email.
Good to know: You can set multiple signatures in Gmail and share contact people with select people only.
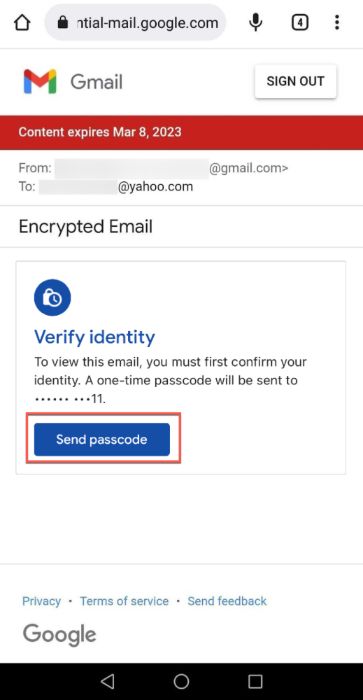
From Another Email App
- Open the mail in your email client of choice. If you’re looking for a disposable email account, we have a list of the best throwaway email providers.
- Tap the “View the email” button.
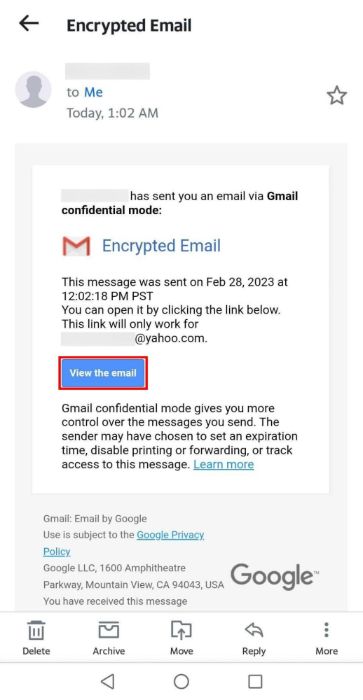
- You will be redirected to your browser.
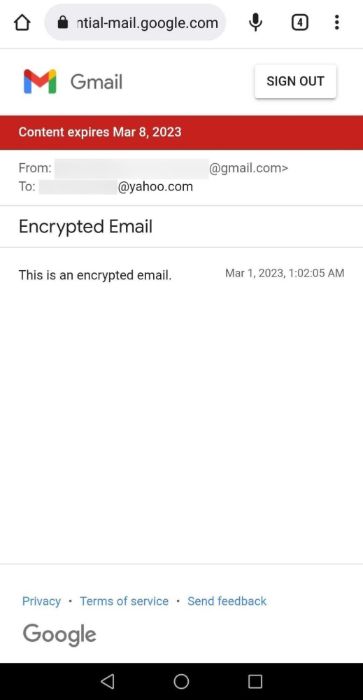
- If the email requires a passcode, tap “Send passcode.”
- Enter the passcode, and press “Submit.”
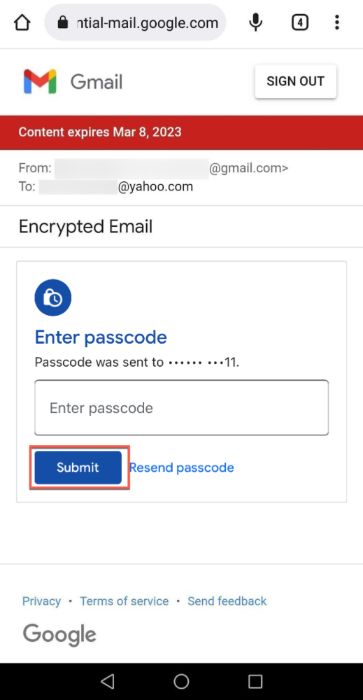
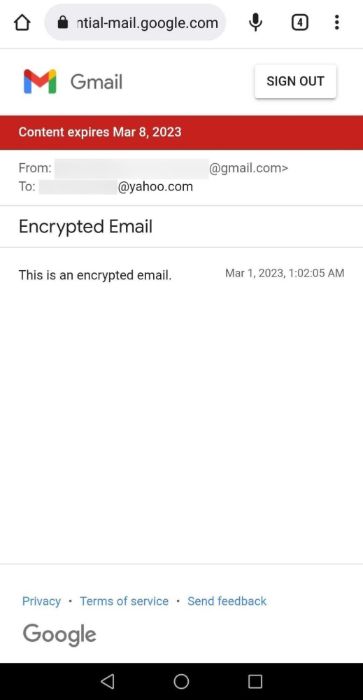
- Your email will become visible.
Tip: learn how to use Google Tasks effectively without leaving Gmail.
Frequently Asked Questions
Are email attachments encrypted?
Generally, email encryption services don’t encrypt the attachments of the email. Despite that, hackers can’t access the attached documents unless they decrypt the entire email first. If you want to add another layer of protection to email attachments, use third-party services like Persistent File Protection to encrypt the attached documents too.
Does a paid Gmail account offer enhanced encryption?
Yes, paid Gmail accounts offer a high level of encryption with S/MIME (Secure/Multipurpose Internet Mail Extensions). It encrypts your email via user-specific keys, ensuring only the intended recipients can decipher the message. However, the sender and the receiver must have S/MIME enabled for it to work.
Image credit: Unsplash. All screenshots by Ojash Yadav.








