By itself, SSH is a secure way of connecting to a remote machine. However, if you are still keen to add additional security to your SSH connection, you can add two-factor authentication to be prompted to enter a random verification code when you connect via SSH. We previously showed you how to do so on various social networks and show you here how to add two-factor authentication to your SSH connection.
Note: this instruction is based on the Ubuntu server. If you are using another distribution, some of the commands may vary.
Installing Two-Factor Authentication for SSH
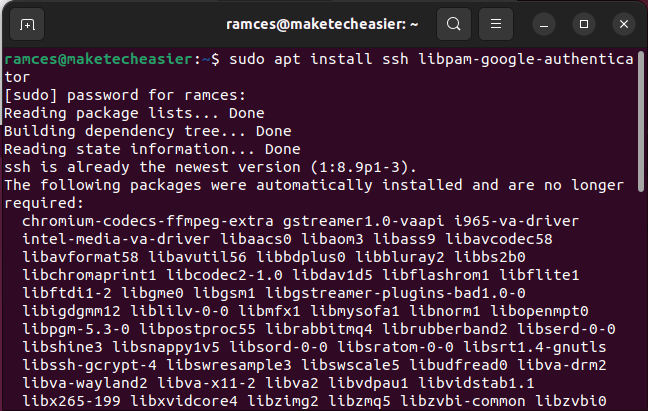
Open a terminal session on the machine where you will install the two-factor authentication, Type the following:
sudo apt install ssh libpam-google-authenticator
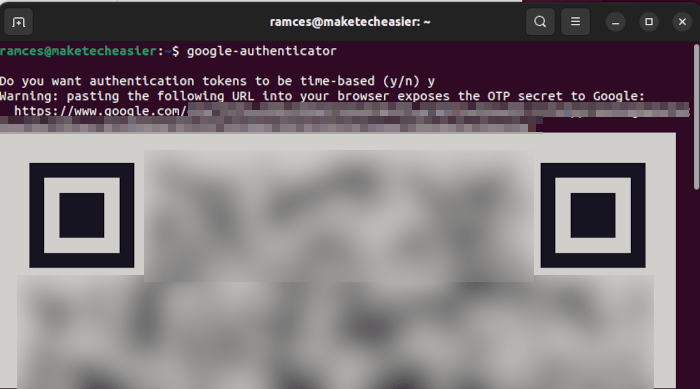
To complete the installation, run:
google-authenticator
Tip: learn how to use SSH X-forwarding to run remote apps.
Configuring SSH Two-Factor Authentication
You will be prompted with a series of questions. In most situations, you can type “y” (yes) as the answer. Anytime the settings are wrong, press Ctrl + C, then type google-authenticator again to reset the settings.
- The program will ask you if you want authentication tokens to be time-based. For this, press Y then Enter.
After this question, you should see your secret key and emergency code. Record and save the details. You will need the secret key to set up the Google Authenticator app later.
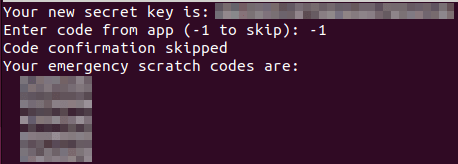
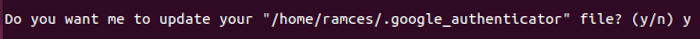
- The program will ask you if you want to update your “/home/username/.google_authenticator” file. Press Y then Enter.
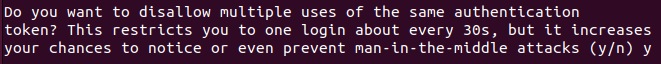
- When asked if you want to disallow multiple uses of the same authentication token, this will restrict you to only one login every 30 seconds. This can be helpful if you want to make sure that only one active connection can use an authentication token at any given time.
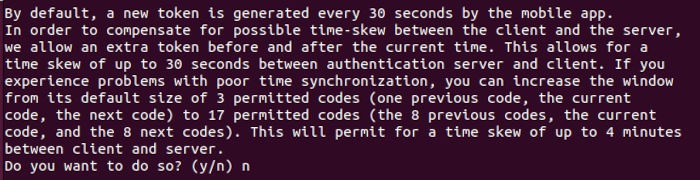
- By default, authentication tokens are only good for 30 seconds. To compensate for a possible time skew between the client and server, increase the window from its default size of 1-1/2 minutes to about 4. This can be useful in cases where the clock of your local machine or remote server is not properly synchronized.
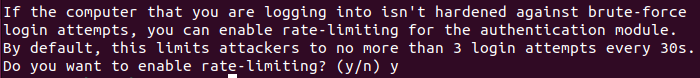
- Enable rate-limiting for the authentication module. This option limits attackers to no more than 3 login attempts every 30 seconds.
Configure SSH to Use the Google Authenticator
- Open the “/etc/pam.d/sshd” file:
sudo nano /etc/pam.d/sshd
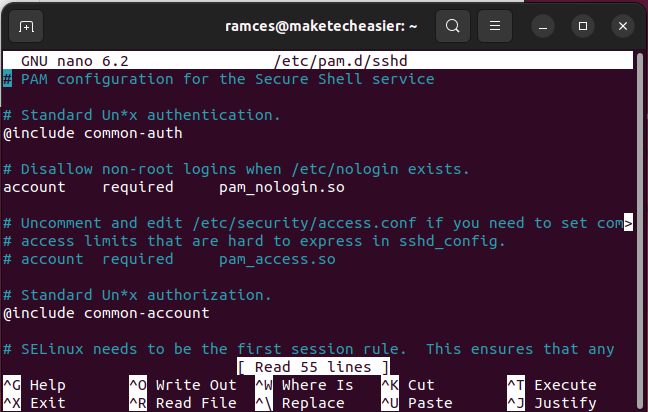
- Add this line to the top of the file:
auth required pam_google_authenticator.so
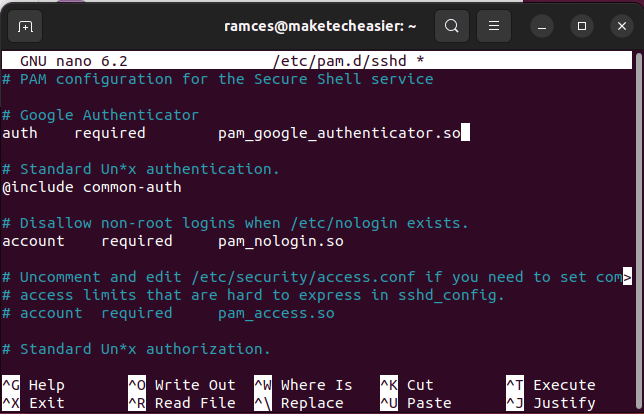
- Press Ctrl + O and Ctrl + X to save and exit the file.
- Open the “/etc/ssh/sshd_config” file:
sudo nano /etc/ssh/sshd_config
- Scroll down to the bottom of the file and type the following line:
ChallengeResponseAuthentication yes
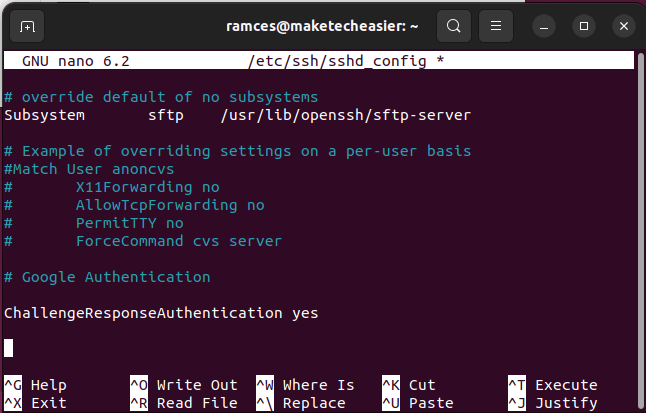
- Save and exit the file.
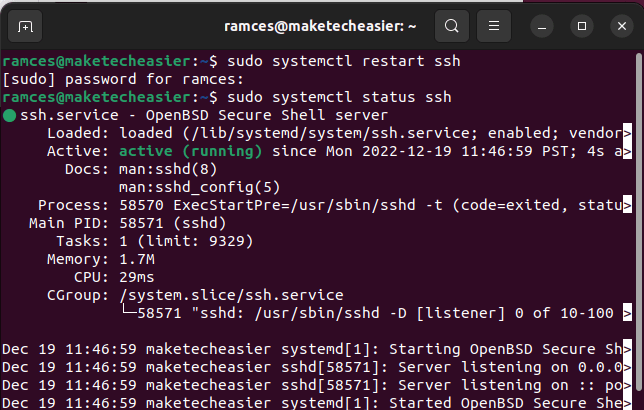
- Restart the ssh server:
sudo systemctl restart ssh
Setting Up a Key in Google Authenticator
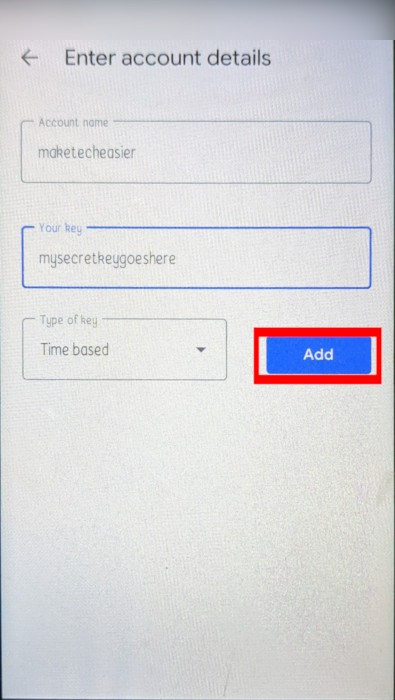
- Open the Google Authenticator app (or one of its alternatives) on your smartphone (or Desktop). Press the Plus icon on the app’s lower-left corner and select “Enter a setup key.”
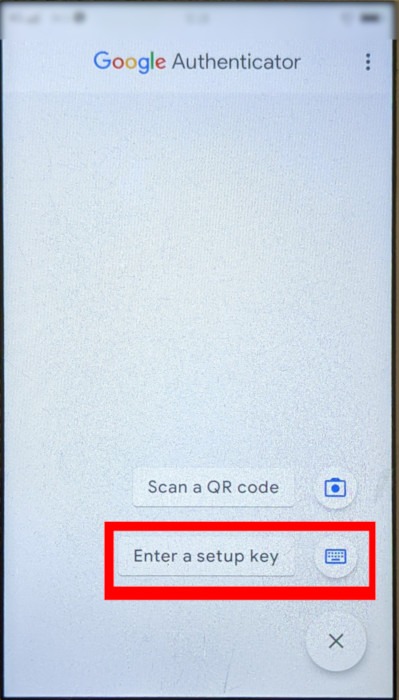
- Provide a name for your authentication app.
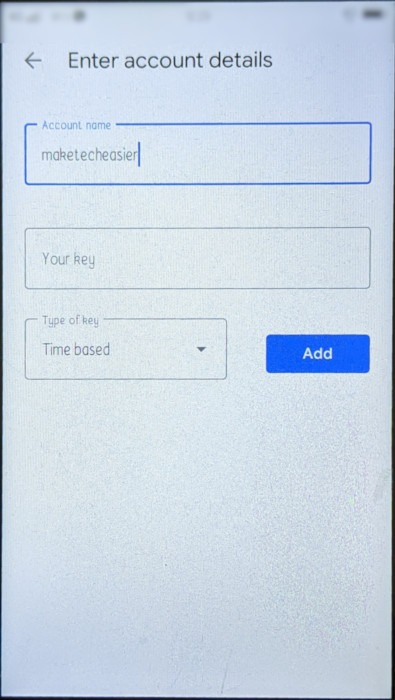
- Type the secret key that you generated earlier and press “Add.”
When you connect via SSH to your remote computer, you will see the request for the verification key.
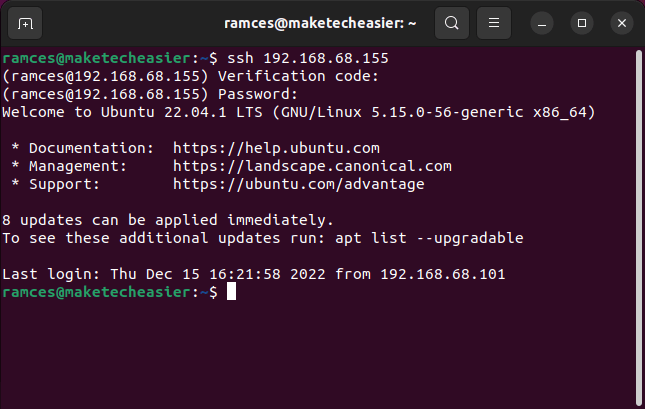
Note: two-factor authentication only works for password-based logins. If you are already using a public/private key for your SSH session, it will bypass the two-factor authentication and log you in directly. Also, check out more ways to secure your SSH server.
Frequently Asked Questions
I am using a Yubikey. Can I still use two-factor authentication in SSH?
No. The Google authentication module only works with a standard SSH password login. Similar to setting up a public SSH key, it is not possible to use this particular module with other external two-factor solutions, such as the Yubikey.
Is it possible to use the same authentication key on a different phone?
Yes. You can easily use a different phone with Google Authenticator as long as you either have your secret key or its QR code. However, you need to make sure that you have fully removed your authentication key on the previous device before you import it to a new one, as any bad actor that obtains access to the previous device will be able to bypass your two-factor challenge.
Can you use a different two-factor authentication app with SSH?
Yes. While the developers of the libpam module specifically designed it to work with Google Authenticator, you can still use it with other authentication apps, as the format of a two-factor secret key is often the same across different implementations.
Image credit: Unsplash. All alterations and screenshots by Ramces Red.








