When you run multiple tabs on your Chrome browser, malware on an infected web page may attempt to access and steal your data from other open websites.
To counter this efficiently, Google introduced Strict Site Isolation with Chrome 63. This security feature has since been upgraded and improved. You have to enable it manually on browser versions below 76. You can also disable it if it’s hindering your device’s performance. Read on to learn how.
What Is Strict Site Isolation?
Strict Site Isolation is a Chrome security feature that prevents user data theft. When you run multiple tabs in your browser, an infected website may try to steal your personal information from other open pages.
Strict Site Isolation prevents this by loading each tab in a separate process and prevents the websites you visit from accessing sensitive data on other open pages.
Google introduced Strict Site Isolation along with Google Chrome 63 in 2017. It was an experimental feature then and, therefore, not enabled by default on browsers. Users, however, could activate it from Chrome flags.
As Strict Site Isolation allocated separate processing power to each tab, it could result in a 10 to 20 percent increase in system memory usage. This was the reason Google didn’t enable this feature by default.
After several performance improvements, Google enabled Strict Site Isolation by default for all websites on Desktop platforms as of Chrome 76 and for most websites on Android devices, requiring users to sign in as of Chrome 77. However, because of the additional processing power required, Strict Site Isolation is available only for Android devices with at least 2 GB RAM.
Tip: sync your Google Chrome data and access it across all your devices.
How to Enable Strict Site Isolation from Chrome Flags
If your Chrome version is 76 or above, Strict Site Isolation is enabled by default for all websites on your browser. On Chrome 63, you have to activate it manually. You can turn on experimental features, such as Strict Site Isolation, from Google flags by following the steps below.
- Launch Google Chrome.
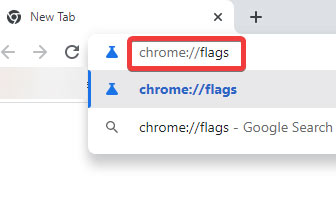
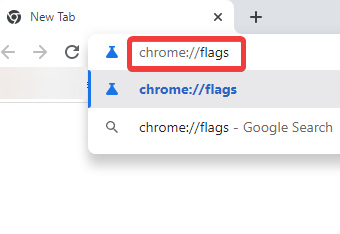
- Type chrome://flags in the address bar and hit Enter.
- Locate “Disable Site Isolation” on the page. Look for it by pressing Ctrl + F and typing “Disable Site Isolation.” In older Chrome versions, search for “Strict Site Isolation” instead.
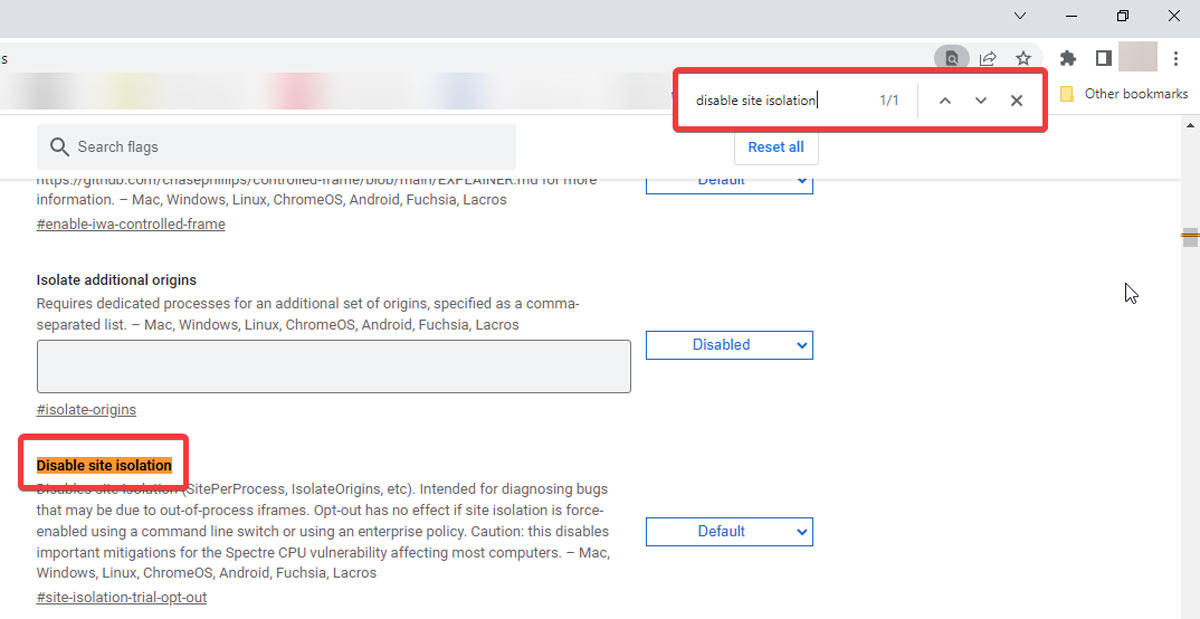
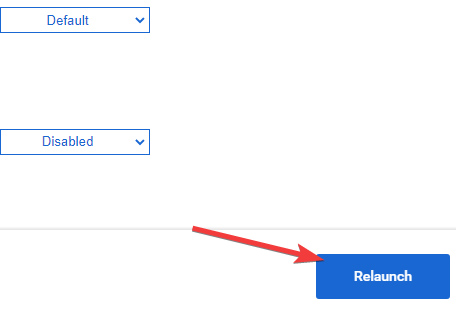
- Click on the drop-down menu next to the feature and select “Default” (“Enable” in older versions).
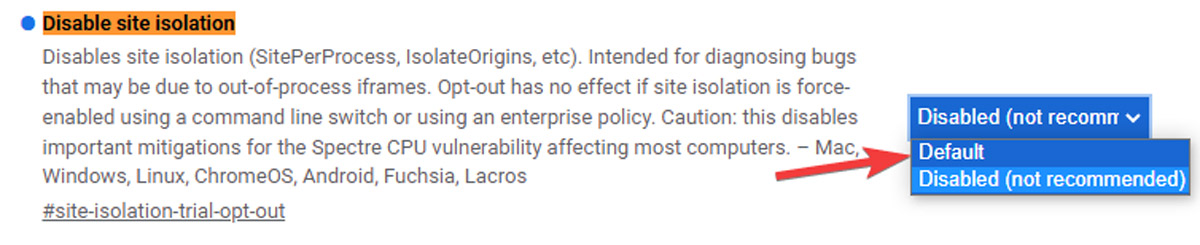
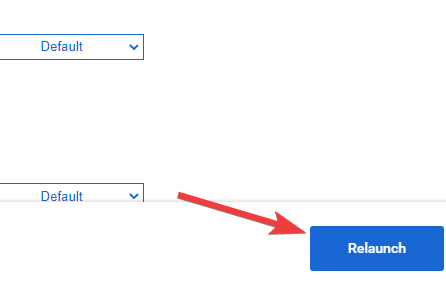
- Select “Relaunch” from the bottom-right corner of the page to apply the changes.
Note: Strict Site Isolation is not available for Chrome versions below 63. Update your browser if this feature is not in your Chrome flags list.
How to Activate Site Isolation from Chrome Properties (Windows Only)
Alternatively, Windows users can turn on Strict Site Isolation for a specific Chrome shortcut by typing a simple flag command in their browser properties. Follow the steps below:
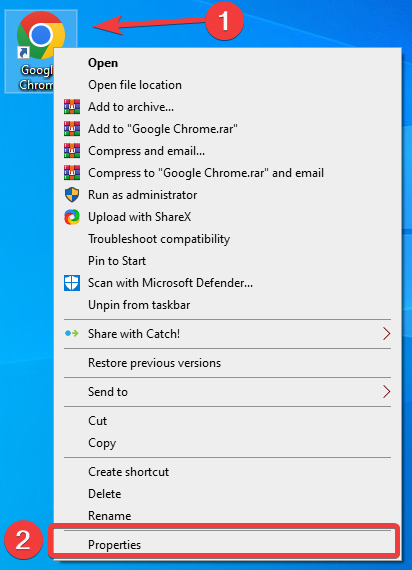
- Right-click the Chrome shortcut and select “Properties” from the drop-down menu.
- Open the “Shortcut” tab.
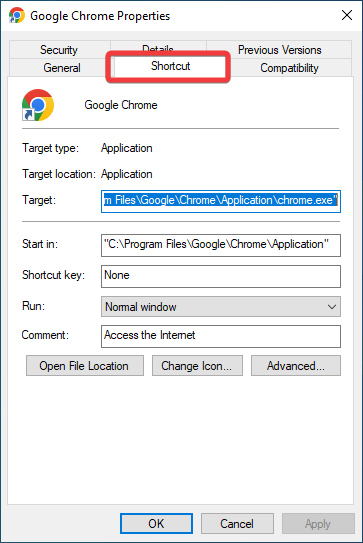
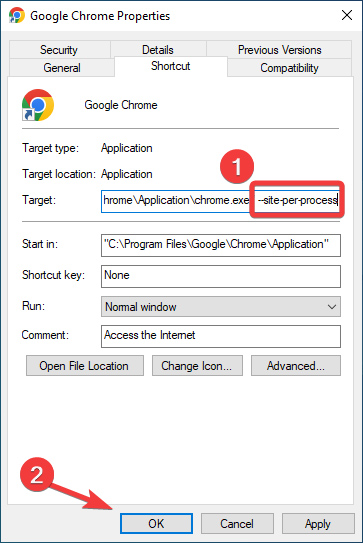
- In the “Target” field, add a “Space” at the end of the address and type
--site-per-process, then hit “OK.” The site isolation feature will be on whenever you launch Chrome via this shortcut.
Do you know: for those who still need to test their websites on an older browser, learn how to enable IE mode on Google Chrome.
How to Enable Isolate Additional Origins
In addition to Strict Site Isolation, Google has another experimental feature that allows you to process a specific website origin separately.
Using a web address, such as “https://example.com,” and enabling Isolate Additional Origins, you can open “https://a.example.com” and “https://b.example.com” in separate processes.
To activate this feature, follow these steps:
- Go to the “Start menu,” type “Google Chrome,” and press Enter.
- Type chrome://flags in the address bar and press Enter.
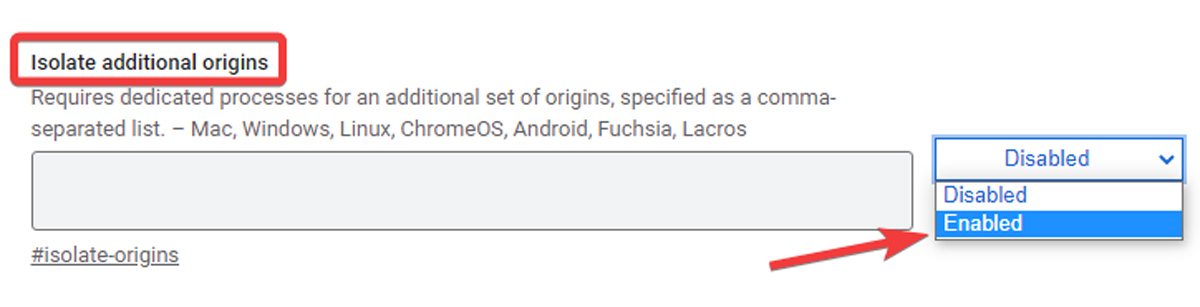
- Find “Isolate Additional Origins” on the page and enable it via the drop-down menu.
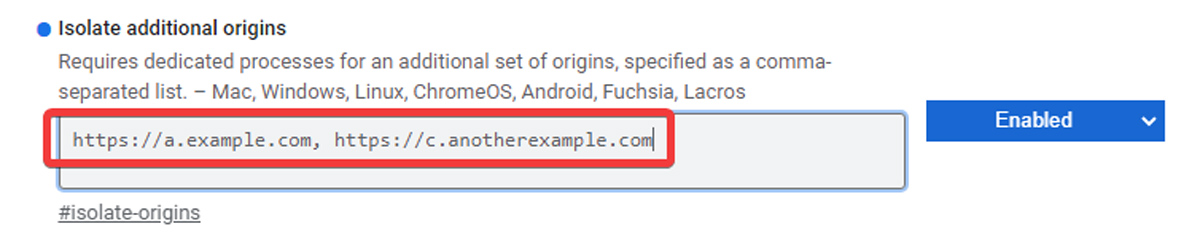
- Specify the origins you want to isolate by typing their URLs in the box. Separate them with commas.
- Select “Relaunch.”
Note: As of Chrome 77, you can isolate a range of origins without adding them individually using a wildcard. For instance, by typing https://[*.]example.com in the box, you will isolate all the origins of “https://example.com.”
Do you know: you can easily set up parental control on Google Chrome to restrict access to certain sites.
Frequently Asked Questions
Why can’t I access an unsecured website?
A connection provided by an HTTP website is not encrypted, and Google identifies it as insecure. In contrast to HTTPS, HTTP does not support SSL (secure sockets layer) and is susceptible to potential hacks. Google ended its support with HTTP, so you can’t access an unsecured website.
How do I allow unsecured websites in Chrome?
From “Settings” in Chrome, go to “Privacy and Security” and open “Site Settings.” Click on “Additional content settings” and select “Insecure content.” Hit “Add” next to “Not allowed to show insecure content” and enter the URL for the site you want to allow. Click the three-dot icon next to the URL and select “Allow.” However, you should be careful while visiting unsecured websites and avoid entering your personal data or downloading files, as it may get you into trouble.
How do I know if Chrome is infected?
Malware may spam you with pop-up ads or open new tabs that won’t go away. It can also change your browser’s homepage or redirect you to unfamiliar websites without your permission. Another sign of malware infection is unwanted extensions that reappear after uninstalling them. Getting rid of the infected Chrome depends on the type of malware that infected it. In some cases, simply uninstalling the shady extension will do the trick. At other times, you only need to reset Chrome via “Reset settings” in the “settings” menu.
Image credit: 123RF








