What makes any malicious action successful is to be unsuspecting. While we’re all aware that we shouldn’t open email links from an unknown sender, when the sender is a trusted organization, it makes us feel safe enough to not even consider that there could be nefarious actions attached to it. That’s the case with a new Emotet campaign that disguises emails as being from the IRS – but they’re really hiding malware within.
Also read: Emotet Malware Targets US Government
What Is Emotet Malware?
Emotet is malware that infects computers by hiding in malicious emails. The malware is hidden in Microsoft Word and Excel files. When these files are opened, unsuspecting users unknowingly enable macros that trigger the Emotet malware to be downloaded onto the users’ computers.
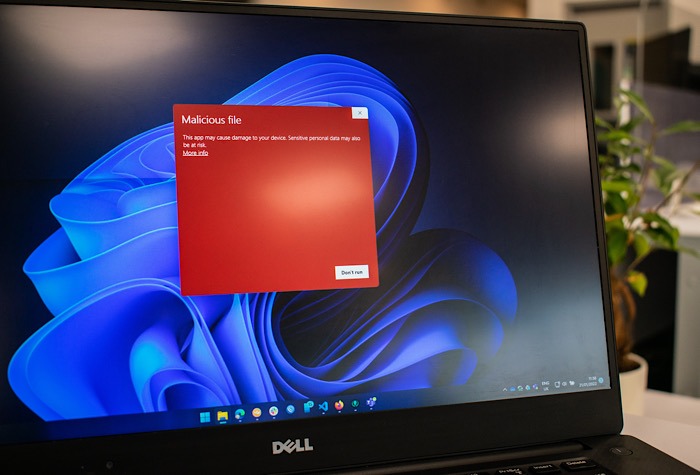
The malware, once installed, steals the emails of users and stores them for use in future attacks. It also sends more spam emails and installs other malware that could lead to a ransomware attack.
But again, to be successful, the Emotet malware needs to find unsuspecting people or an unsuspecting way to launch the attacks.
Ransomware Pretending to Be IRS
The Emotet malware found its unsuspecting way to launch attacks during tax season. It’s very easy to assume the Internal Revenue Service letter you’re looking at in your email is real.
Security firm Cofense issued a report that showed the multiple phishing campaigns that were disguised as emails from the IRS. The recipients are tricked into believing the emails contain their tax return, W-9 form, or another relevant document.
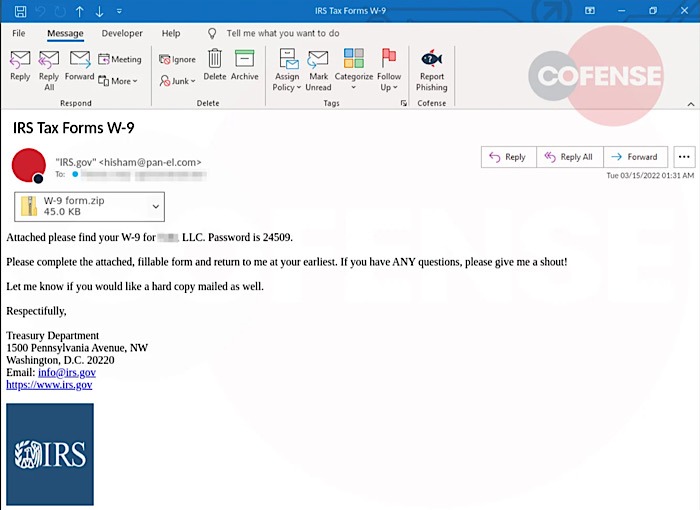
The letters contained in the emails and the subject line in the emails may differ, but ultimately, the overall message is that this is an important document you’ve been waiting for. The subjects have been “IRS Tax Forms,” “W-9 Incorrect Form Selection,” and “INCOME TAX RETURN 2021.”
An example directs recipients to a W-9 attachment and asks for it to be filled out and returned. It kindly offers answers to any questions and a “hard copy email,” which seems like an oxymoron.
Zip files or HTML files are attached to the emails. They get through secure email because they are password protected. This leads to an assumption that this is a group that knows what it’s doing.
Then again, in tests that were conducted, the files weren’t parsed correctly by the built-in extractor in Windows. And if the malware can’t be downloaded, the email won’t hold much weight. Third-party programs, though, don’t have a problem extracting the files.
Inside an example email is a “W-9 form.xslm” Excel file. After it’s opened by a user, they are asked to click the “Enable Editing” or “Enable Content” button to see the document. When the button is clicked, the micros will download and install the Emotet malware that’s waiting on WordPress sites that have been hacked.
Additional payloads will be downloaded once the Emotet malware is installed. These payloads have often been Cobalt Strike. Another research group, Cryptolaemus, has seen the SystemBC remote access Trojan being dropped by Emotet.

Perhaps something similar is what happened to my husband and me. We filed our return a few years back through an online tax software, and we were informed someone with our names, address, and social security numbers had already filed our return. Neither of us had initiated a tax return other than that one. We had to jump through hoops to convince the IRS of our true identities.
We have not been fooled since and no longer file online. A note to the wise: the IRS won’t email you. It will contact you through the United States Postal Service. If you believe you may have been infected, learn how to check your PC for Emotet malware.