Did you know that most email services like Gmail and Outlook only use basic email encryption techniques, leaving your email prone to data attacks? This tutorial discusses the various data encryption techniques you can implement to secure your data.
Also read: PGP Encryption: How It Works and How You Can Get Started
What Is Email Encryption?
Email encryption is a technique that disguises an email so that only the sender and intended recipient can access its contents, preventing unauthorized individuals from intercepting the signal and reading the message.
Most email doesn’t have this level of protection. Content is sent as regular text and open to data security risks. However, you can step in with proper end-to-end encryption, for instance, to secure your confidential email easily.
In this method, email is encrypted on the sender’s system using a public encryption key that scrambles the email and any attachments. The email is then sent to the recipient, who has a private key that can be used to decrypt the message. This technique is so secure that the message cannot be read by any email services, banking institutions, Internet service providers (ISPs), or hackers.
Why Is Email Encryption Important?
Privacy on the Internet is paramount for every individual and enterprise. However, a cyberattack can very easily put your private information in emails, such as login passwords, files, pictures, sensitive documents, and OTPs, at risk.

The data you are sending via email may seem harmless, but even a mildly proficient hacker can extract your static or dynamic IP address, which can be used to reveal your name, address, ISP, and so much more. Using this data, any motivated hacker can wreak havoc by using strategies like phishing.
Phishing is one of the most prominent forms of cyberattacks. A large number of these attacks are caused by unencrypted emails that reveal sensitive data to malicious parties and are entirely preventable. Given this scenario, it’s in your best interest to encrypt your email.
Also read: Why Encryption Is Not Working on Windows 11 Home, and How to Fix It
Types of Email Encryption
There are multiple protocols for email encryption, each one suitable for different use cases, depending on implementation cost, success rate, complexity, and various other factors. A few prominent email encryption protocols in use today are covered below. They can be divided into two distinct types: transport-level encryption and end-to-end encryption.

Transport-level encryption handles the data during transportation from the sender to the recipient. This format is less robust but cheaper than end-to-end encryption (E2EE), which stores the private encryption key at the endpoints and uses a public encryption key to secure data. The additional protection offered by this method comes at an additional price.
PGP and S/MIME
PGP or Pretty Good Privacy is considered one of the most widely used encryption protocols in the world. It utilizes the end-to-end encryption approach, providing cryptographic privacy and authentication with techniques like hashing, data compression, symmetric-key cryptography, and public-key cryptography to encrypt and protect datasets like emails, directories, and documents. S/MIME is used for email that contains multimedia files.
It was developed by Phil Zimmermann in the year 1991 and follows OpenPGP as the encryption key and standard (RFC 4880) for encrypting and decrypting data.
StartTLS
StartTLS is a form of transport-level encryption that uses either TLS (transport layer security) or SSL, also known as secure sockets layer, to upgrade an unprotected system to a protected one. It asks the email server to convert the unencrypted message into an encrypted one while the mail is being transmitted from sender to recipient.
This way, both the sender and recipient enjoy encryption without having to encrypt and decrypt messages on their systems. However, this approach can still leave the data vulnerable to hackers, who may intercept the message between the sender and the email server. These vulnerabilities can be overcome using protocols like DANE and MTA-STS.
Also read: Windows Security Not Opening in Windows? Here are 8 Fixes
DANE or MTA-STS
DANE (DNS-Based Authentication of Named Entities) or MTA-STS are similar protocols and serve the same purpose. MTA-STS is actually SMTP MTA-STS, short for Simple Mail Transfer Protocol – Mail Transfer Agent – Strict Transport Security. That is a mouthful!
The only apparent difference between DANE and MTA-STS is that DANE utilizes DNSSEC for DNS authentication, while MTA-STS relies on certification authorities. Also, MTA-STS features a testing-only mode, which allows you to deploy a policy in a test environment before adopting it.

These tools can be used as add-ons for extra protection on top of the StartTLS encryption protocol. They protect you from hackers and cybercriminals using StripTLS attacks or stripping attempts of TLS security levels, by enforcing the use of TLS by both the sender and recipient. Therefore, these protocols offer an added level of premium protection if a user finds that existing StartTLS encryption protocols are not enough.
Also read: 10 Disposable and Throwaway Email Providers You Can Try
Bitmessage
Bitmessage is a relatively newer component of online data encryption and security. It was released under the liberal MIT license in 2012 and is based on the model of security protocol used by Bitcoin. Bitmessage is a peer-to-peer, zero-trust framework that gained traction shortly after its release when rumors of spying by the National Security Agency (NSA) surfaced.
It offers some pretty advanced data security features, like decentralization, hermetic encryption, hidden sender and recipient, and proof of work (POW) requirement. The peer-to-peer encryption protocol makes Bitmessage almost impossible to track, which is one of the many reasons for its popularity.
GNU Privacy Guard
GNU does not adhere to any single model of data encryption – transport level or end-to-end formats. It is, in fact, a complex hybrid of the two. Also known as GPG or GnuPG, it utilizes public key encryption for ease and symmetric key cryptography for the swiftness of the process.
It is open freeware and can be used, modified, studied, etc. GNUPG is still prone to cyber attacks where hackers may pose as either sender or recipient. This is due to the exchangeability of the public key used for encryption.
Also read: What Is Microsoft’s Pluton Security Processor and Why You Need It
Third-Party Email Services That Offer Email Encryption
There are several third-party email clients that offer varying degrees of email encryption. These email service providers can help defend you and your system from cyberattacks, spam mail, doxxing, and many other ways hackers try to get through your defenses.
1. ProtonMail
Developed by CERN scientists in 2013, ProtonMail has emerged to be one of the leading secure email services in the market today. It is best suited for personal, non-institutional use by individual users, and encrypted email sent using this service can be accessed by recipients across all email servers.
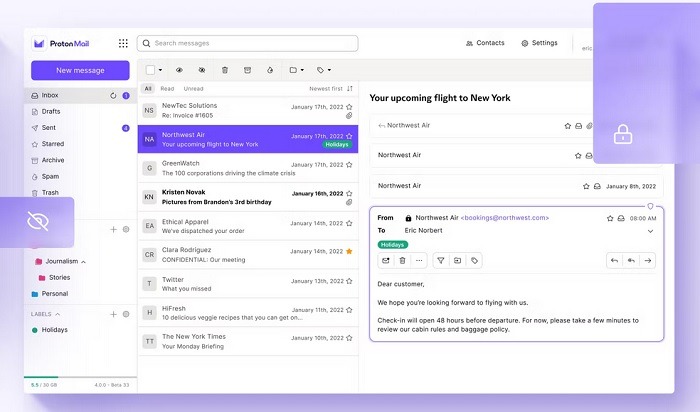
ProtonMail features a strict no-logs policy, meaning it does not log any user information that passes through its systemn to ensure complete security and anonymity on the Web.
It utilizes end-to-end encryption to best protect your data between nodes. One of the most unique features of ProtonMail is PGP encryption, which very few email clients offer.
The service is supplemented by a fluid, user-friendly mobile app (Android | iOS) to be used in conjunction with the web client. However, it does not offer a dedicated desktop app, which can be an issue for some.
Also read: 7 Chrome Security and Privacy Extensions to Stay Safe Online
2. Mailvelope
Mailvelope is a freeware email service provider powered by a German enterprise, Mailvelope GmbH, since 2012. It uses end-to-end encryption to provide security to users and takes advantage of the OpenPGP standard to encrypt and sign electronic messages and corresponding files in emails.
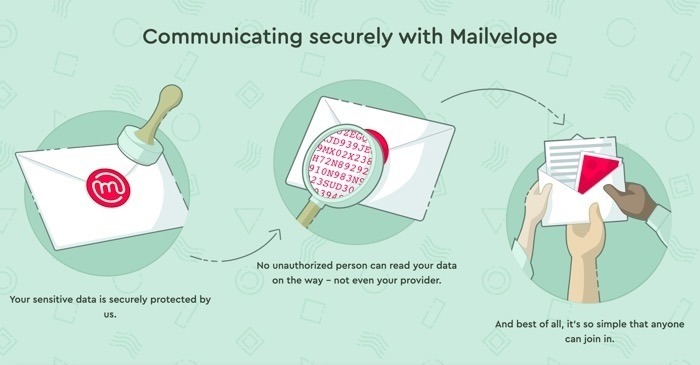
The unique thing about Mailvelope is that it features neither a desktop nor a web app. Rather, it is a free browser add-on that integrates itself with almost all web email services and encrypts your email without forcing you to migrate to a different app ecosystem.
Mailvelope has been adopted by users across all usage types. It is suited for enterprise, institutional, and individual users and has been integrated into the workforce of several companies. It is compatible with email services like Gmail, Outlook, Yahoo, 1&1, Freenet, and GMX.
Also read: How to Use Google Tasks Effectively in Gmail
3. CipherMail
CipherMail caters specifically to corporations and similar institutions and has been adopted by dozens of multinational companies across verticals.
It features a slew of advanced features aimed at protecting users from hackers, cyberattacks, insider leaks, and the cyber threats corporations deal with on a daily basis.
CipherMail’s powerful email encryption gateway supports all major encryption protocols, like S/MIME, PGP, TLS, and PDF encryption. On top of that, it is compatible with all SMTP-based services and can be easily integrated into the existing workforce of an enterprise.
It also offers a Webmail Messenger that can protect data in cases where S/MIME or PGP cannot be used.
CipherMail allows users to communicate efficaciously and securely with external recipients who do not use any email service provider. In such a scenario, the recipient can install and use CipherMail’s webmail messenger to securely receive messages and files across the Web. CipherMail can also be accessed via Android devices.
Also read: How to Encrypt Your Files in the Cloud Using Rclone
4. Startmail
StartMail is a secure email service offered by the creators of the privacy-focused Startpage search engine. It integrates PGP encryption standards into the encryption protocol.
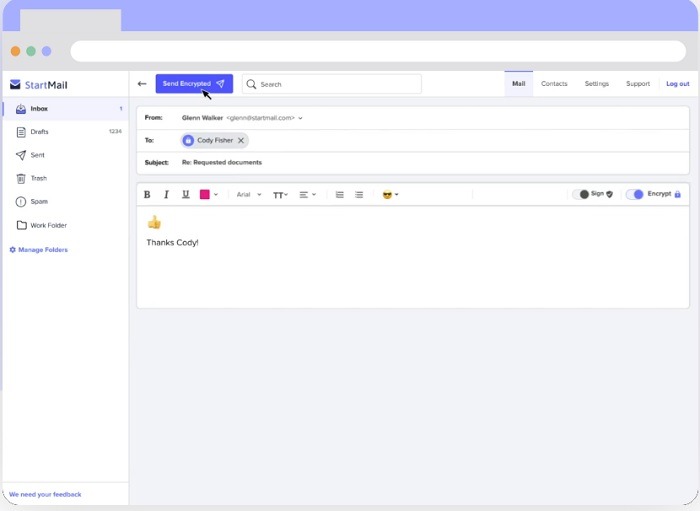
The thing to note here is that PGP is implemented with only the server and is therefore not true end-to-end encryption. However, you can enable two-factor authentication to secure your account, protecting it even if your password is compromised.
StartMail offers users the ability to utilize burner email addresses without losing the encryption privilege, thus adding additional convenience to day-to-day operations. It also allowsmultiple aliases for quick throwaway usage and offers complete IMAP and SMTP support to users.
StartMail has a web client and desktop app. However, it lacks mobile support.
Also read: How to Schedule Email in Outlook
5. CounterMail
CounterMail uses OpenPGP to encrypt your data with 4096 bits encryption keys.
It is the only known email service that can protect your email from man-in-the-middle (MITM) attacks. To achieve this, it uses a hypercomplex system comprised of four layers of added protection, including:
- SSL encryption
- Session encryption
- OpenPGP encryption
- Server side disk-encryption
These layers are based on standard algorithms, but their independent operational ability makes them impenetrable to attacks.
CounterMail is available as a web app and mobile app (Android). The web app design isn’t great, but the app itself is reliable in terms of supreme security and anonymity.
The service also offers two-factor authentication for added protection and comes with a seven-day free trial. Even the payment gateways offer an anonymous payment option to further protect your identity.
Also read: How to Change Gmail Name on Mobile and PC
Frequently Asked Questions
Can hackers intercept encrypted emails?
Yes, it’s possible for hackers to intercept your encrypted emails. However, they will not be able to read the content of your email, as it will be distorted and jumbled. The only way to make it readable again is to decrypt it using the encryption key.
What are the most common methods of email hacking?
The most common are:
- Email phishing: hackers send emails that look like they’re from a legitimate company or person in the hopes that the recipient will click on a malicious link or attachment.
- Malware: malicious software is embedded in an email attachment or link, and once opened, it gives hackers access to your computer or network.
- Spear phishing: this targeted email phishing attack uses information specific to the recipient to make the email seem more legitimate.
- Domain spoofing: a hacker spoofs the domain name of a legitimate email address, making it look like the email is coming from a trusted source.
- Email forwarding: hackers set up email forwarding rules to send copies of all incoming and outgoing messages to another email address without the user’s knowledge.
Does encrypted email guarantee encrypted attachments?
Not all encryption methods can automatically protect files that are attached to a message. Encryption methods that cover attachment encryption are usually end-to-end based. If they aren’t, you’ll need a separate program to encrypt your file before attaching it to the email.
Image credit: Mikhail Nilov via Pexels.