Generally, when an app developer adds features that improve security, privacy, and performance, they don’t get a lot of flak for it. Mozilla’s implementation of DNS over HTTPS (an encrypted way for your computer to look up web addresses), however, earned it a place as a finalist in the “Internet Villains” ranking run by the UK’s Internet Service Provider Association (ISPA) and some negative comments from government agencies.
Why? Because this feature encrypts the requests your computer sends out when it’s trying to find a website. UK ISPs have to comply with Internet blocking and tracking regulations, a lot of which are implemented at the DNS level, so they’re not big fans of people getting the power to bypass their filters.
Most of the Internet doesn’t agree with the ISPA, though, since encrypted DNS makes pretty much everything better: it keeps your browsing more private, helps prevent cyberattacks, and even works a bit faster than regular DNS.
What is DNS again? And what’s wrong with it?
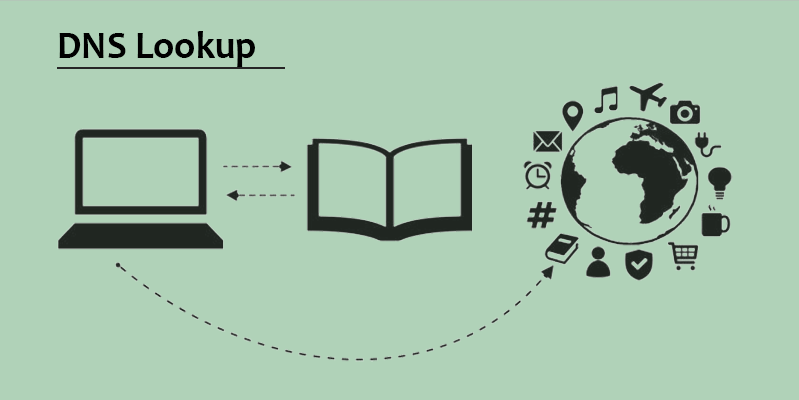
If you forgot how normal DNS (Domain Name Server) works, here’s a quick breakdown:
- Websites all have IP addresses made up of numbers, but that’s hard for us to remember, so we use names.
- In order to match the name we type in with the number, our request needs to go to a DNS server, which maintains a list of IP addresses mapped to names. That’s a DNS request – asking a “phonebook” server to tell us the actual numeric address of the site we’re trying to visit.
- Your default server, if you haven’t changed it, will be the one recommended and/or run by your ISP. Your request will go there, and the server will do a bunch of fancy footwork, bouncing your request around to a few different places to put the pieces together.
- After a few microseconds, the address you need should come back to your device, allowing you to establish a connection with the server that the website you want is on.
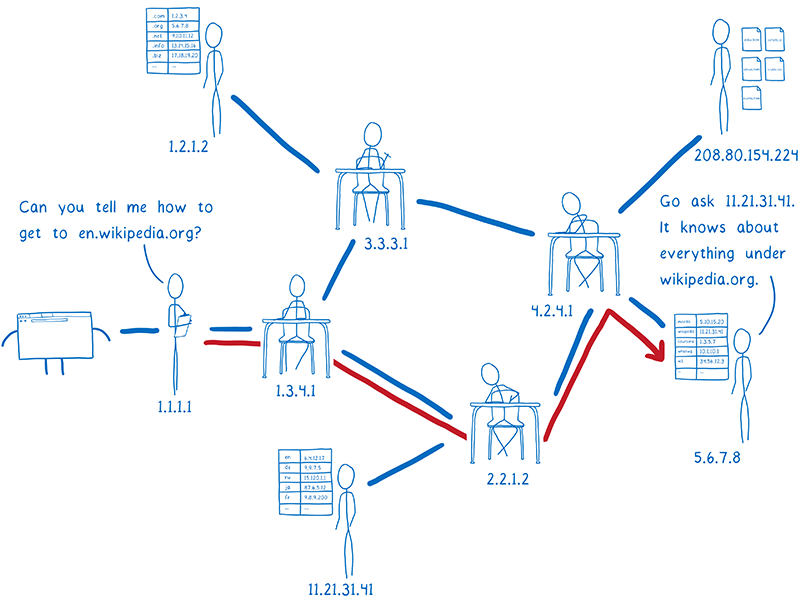
This is basically a complex phonebook lookup process, and it all happens in a few milliseconds, which is pretty impressive. However, all of this information is sent around in plain text, meaning anybody who looks at it (usually your ISP, but maybe an attacker) can tell where you’re going and possibly interfere with your connection by either blocking it or sending back the wrong address to try to get you to visit a malicious website.
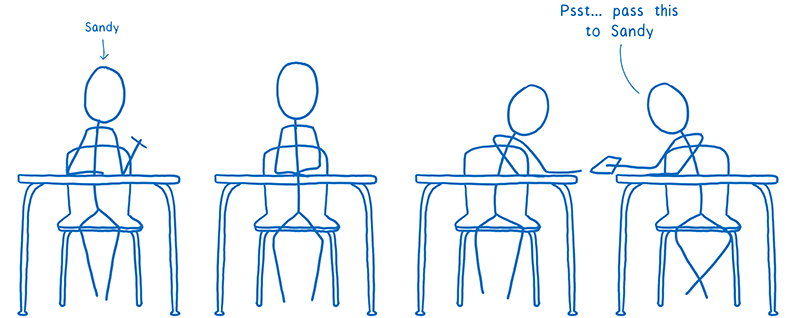
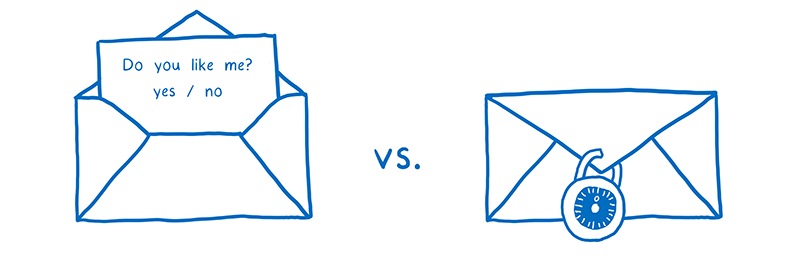
Lin Clark at Mozilla uses the metaphor of passing a note in class with someone’s name written on it – it might get where it’s going, but now everyone knows who you’re passing a note to, and if they want to they can read it or tamper with it. Wouldn’t it be better if there was a way to write the notes in a secret code and get them to the recipient without everyone knowing who it is? That’s DNS over HTTPS.
How is DNS over HTTPS different?
If you send data using HTTP (the basic protocol for transmitting data over the Web), it’s in plain text, making it readable by pretty much anyone (like regular DNS). HTTPS, though, is encrypted so that no one who intercepts the data can read it. DNS over HTTPS is pretty much what it sounds like: your DNS request is sent to the name server over the same secure channel that transmits your credit card data when you check out on a shopping site.
Nobody, including the ISP, knows what’s inside. If they try to open it, it will look like gibberish. The request can’t be blocked or logged, so countries like the UK and China will have a tougher time filtering and tracking traffic. That doesn’t make it completely untraceable, since your ISP still may be able to see the address you end up connecting to, but it makes blocking harder and obfuscates a lot of detail about your activity.
Firefox has also partnered with Cloudflare, which has agreed to extra-strict privacy standards for Firefox users and is also using “QNAME Minimization,” which essentially breaks your request into pieces so that no one server gets the whole address you’re looking up.
How do I get it?
DNS over HTTPS is not currently enabled by default in Firefox, but it’s easy to do.
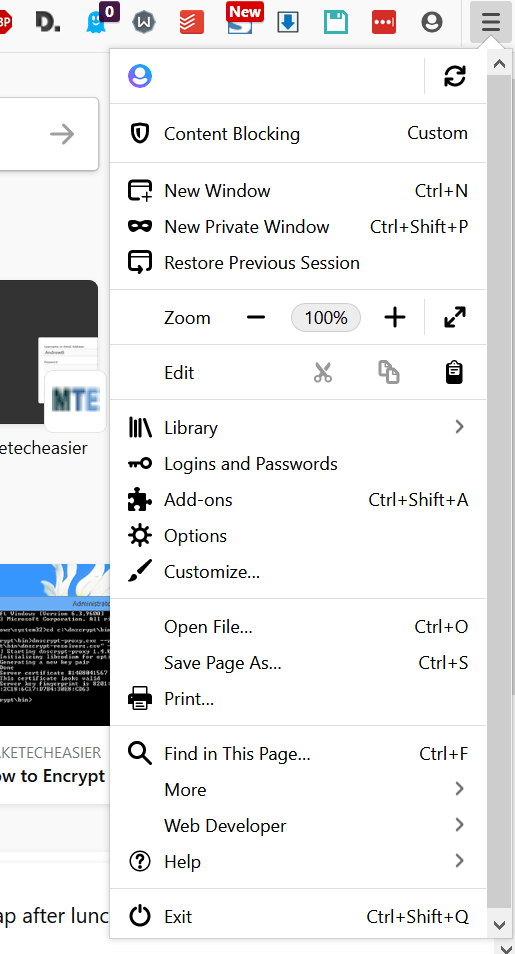
1. Open the hamburger menu on the top-right.
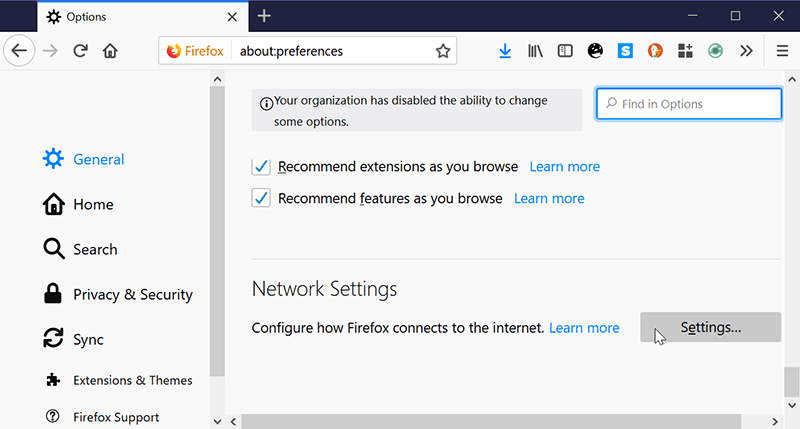
2. Go to Options and scroll down the “General” section until you see “Network Settings.”
3. Check “Enable DNS over HTTPS.” You can either use the default Cloudflare (recommended, as it has lots of extra privacy features) or enter your own.
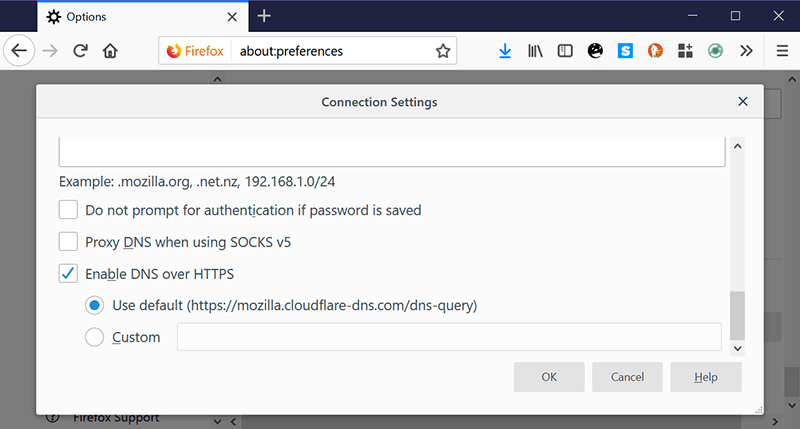
You’re done! You can check and make sure it worked on DNS Leak Test. You should see Cloudflare DNS servers popping up. You’ve just added a few privacy, security, and censorship resistance points to your stat sheet. Congratulations!
If you’re more of a Chrome user, you’ll have to wait until Google enables it there, and it’s likely that they will, but you can still change your system’s DNS to something a little more private than your ISP.
Maybe ISPA should have stayed quiet?
This has the Streisand Effect written all over it: you try to suppress something you don’t like and end up making it more popular than it would have been otherwise. ISPA’s attempt at shaming Mozilla actually ended up spreading the word about DNS over HTTPS better than Mozilla probably could have on its own.
If enough people start using it, it will definitely create problems for countries that use DNS to censor the Internet, but that’s hardly the only way to block sites, so this isn’t a complete solution by any means. A VPN is still the absolute best way to get around censorship and/or tracking, and it’ll probably stay that way as more governments and ISPs adapt their surveillance strategies.
Image credit: intro to DNS over HTTPS