There are many different ways to get a root session in the Linux terminal. This can create some confusion, as most beginner users who are looking to gain root privileges might not be familiar with how each command can gain root access, how they are different and when these differences matter. Here we take apart each of the many different commands used to gain root access in a terminal, explain how they gain root, when to use them, and everything in between.
Also read: What Is Doas and How to Install It
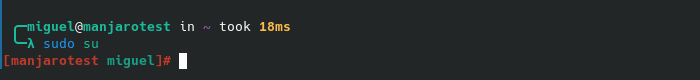
su
The su command substitutes the current user for root in the current shell.
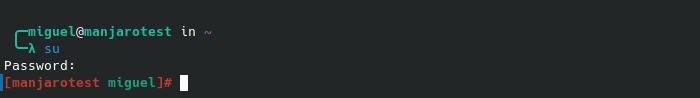
You can switch to any user by typing su and adding a username after it.
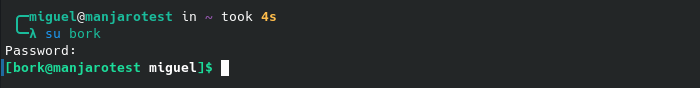
This will tell the system to switch (and essentially log out of) the current user to the one specified. Alternatively, the su command can gain root access by entering su without specifying anything after the command.
su is best used when a user wants direct access to the root account on the system. It doesn’t go through sudo or anything like that. Instead, you’re asked to enter the root user’s password, as you’re literally logging into it. Furthermore, other ways of gaining root access do not have the benefit of also getting access to the root home directory and root environment.
Warning: using su is the least safe way to execute a root action. Generally, if you can avoid it, do not use this.
Also read: The Ultimate Guide to Apt and Apt-Get Commands
su -c
This command passes other commands to the root user directly.
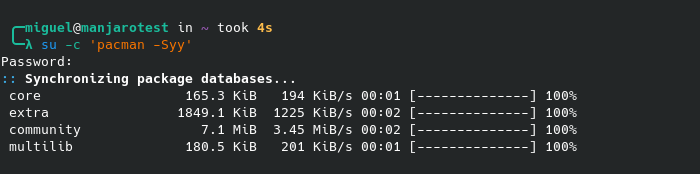
Similar to typing sudo before a command, su -c will run a command as the root user. Instead of simply typing the command, though, you’ll have to put it in quotes.
This is a quickfire way of shooting one command through your terminal with elevated privileges. It’s very useful if sudo somehow is unavailable (it doesn’t come preinstalled in distros like Arch Linux) or fails to work correctly because it’s corrupted.
Since you’re passing something directly to root, if your user and root passwords are different, you’ll have to type your root password to authenticate.
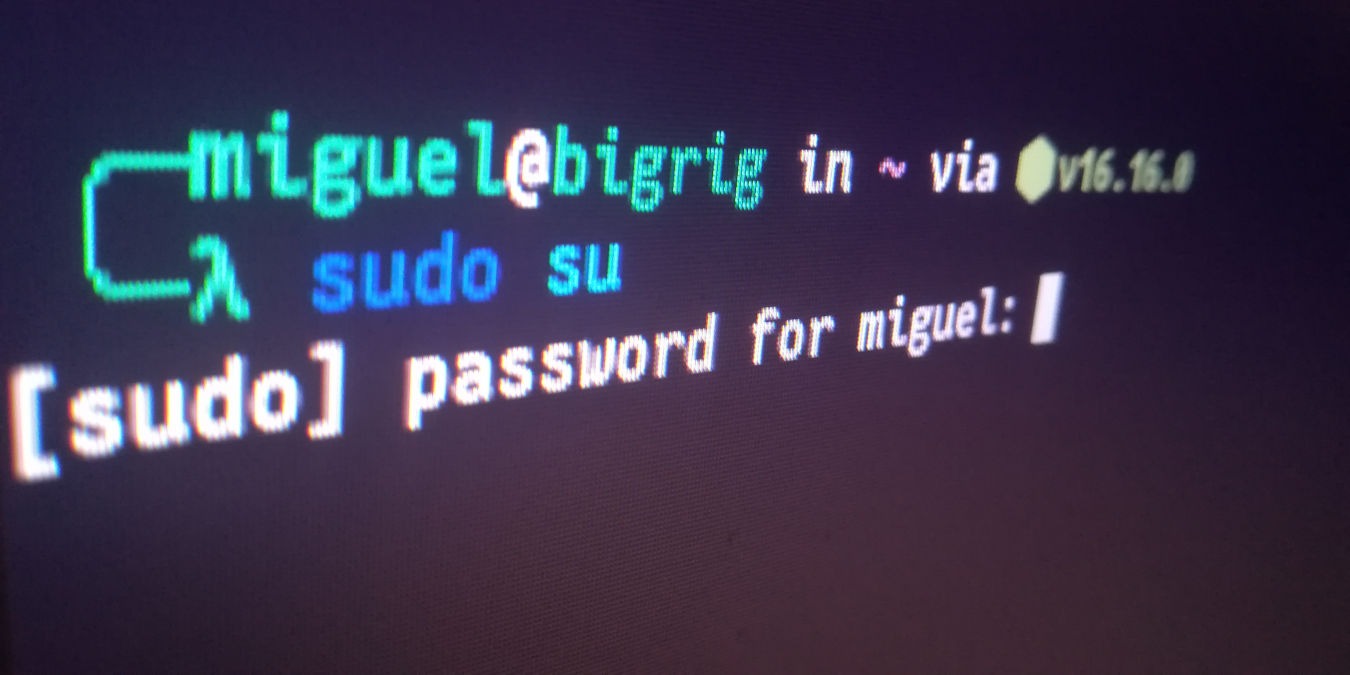
sudo su
This command asks for the current user’s password rather than root.
It’s essentially the same as just running su in the shell, save for one crucial difference: instead of telling the system to “switch users” directly, you’re telling it to run the su command with superuser privileges. When sudo su is run, “.profile,” “.bashrc” and “/etc/profile” will be started, much like running su (or su root). If any command is run with sudo in front of it, it is given root privileges.
Though there isn’t a large divergence between sudo su and su, the former is still a very useful command for one important reason: when a user is running su to gain root access on a system, they must know the root password. Root is given with sudo su by requesting the current user’s password, which makes it possible to gain root without the root password.
This is useful in situations where you may have forgotten the root password if it’s different from the password for your user account. While you could do this in the meantime, you should still reset the root password at some point.
Also read: How to Use Rm Command in Linux
sudo -i
Using sudo -i is virtually the same as the sudo su command with one exception: it does not directly interact with the root user.
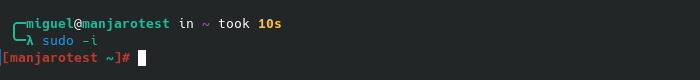
Much like sudo su, the -i flag allows a user to get a root environment without having to know the root account password. sudo -i is also very similar to using sudo su: it’ll read all of the environmental files (“.profile”, etc.) and set the environment inside the shell.
Where it differs from sudo su is that sudo -i is a much cleaner way of gaining root and a root environment without directly interacting with the root user.
To clarify: with sudo su, you’re using more than one root setuid command in the background. This makes it much more challenging to figure out which environmental variables will be kept and which will be changed (when swapping to the root environment). This is not true with sudo -i. Because of this, most people view it as the preferred method to gain root without logging in directly.
In simpler language: sudo -i will give you a “clean” root login in your “/root” folder, which is the “home” folder for the root user.
Also read: How to Use the dd Command in Linux
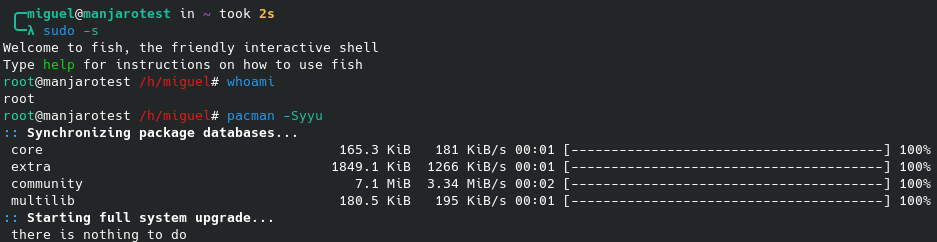
sudo -s
This command summons a shell with your $SHELL variable.
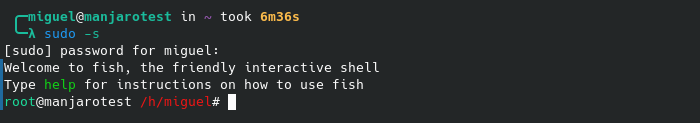
The -s switch for the sudo command reads the $SHELL variable of the current user executing commands. This command works as if the user is running sudo /bin/bash, if the shell the user comes from is bash.
In our case, sudo -s gave us the fish interactive shell, as we previously installed fish as our default shell, so it would be as if we ran sudo /usr/bin/fish.
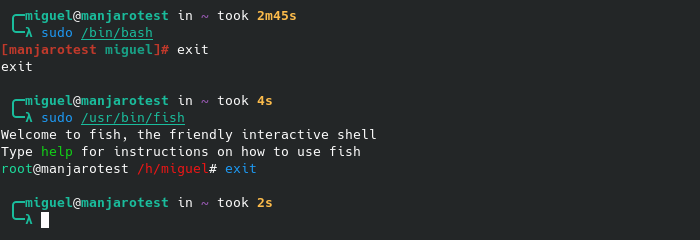
Sudo -s is a “non-login” style shell. Unlike a command like sudo -i or sudo su, the system will not read any environmental files. When a user tells the shell to run sudo -s, it gains root but will not change the user environment. Your home will not be the root home, etc.
This command is best used when the user wants to switch over to root but keep the same shell environment. For instance, you may want to run a fish script and not be forced into the default bash shell that root often gets in most distros.
Other commands covered above gain root access but will also give you the shell and environment variables that the distro has for root. Maybe you just want to switch to the user without all that baggage!
Also read: Basic Bash Commands for Linux Newbies
Frequently Asked Questions
Why would the shell I’m running with matter?
If you use an unmodified bash shell for your user account, the difference is mostly philosophical. In most instances, elevating to root through either shell will not result in any noticeable change. But if you run anything else, you’ll immediately notice how different things can be!
For example, let’s say you’re running the fish shell for your user account and keep the root shell in bash. Loading the user shell by using sudo -s yields a drastically different result.
The shell will follow whichever configuration you have in root’s home folder. If you don’t have such a thing, it will just load the default configuration instead of your personal one. (In our case, that would be “~/.config/fish/config.fish”.) For all intents and purposes, it’s best to leave things that way rather than copying over the user configuration to “/root”.
Changing to your user account’s shell when swapping over to root should only be done if you need to run a script that absolutely needs that particular shell.
Can accessing root harm my system?
In some cases, yes. Unless you’re absolutely sure you need to access root for everything in a particular terminal session, it’s often better to just type sudo followed by a command, if you want to access root for that particular command. For example, typing sudo apt install vlc in any Debian-based version of Linux would tell the operating system to access root just to run the APT package manager to install VLC.
One very important caveat to running sudo -i or any other variant we’ve discussed earlier as opposed to typing sudo before each command you want to run as root is that the former does not log your command history into “/var/log/auth.log”. If you mess up, you can’t go back and check on what you did so that you can correct it. You’ll have to operate out of memory, as root sessions are not recorded.
When I type “sudo” before a command, which variant of “sudo su” am I running?
By typing sudo to execute a command (i.e., you’re typing it in the same line as the command you want to run), you’re essentially running it under an interactive root shell. This would be what the sudo -s standalone command does. It’s also very similar to running the su -c command.
All screenshots by Miguel Leiva-Gomez.