Malware is a malicious software whose goal is to disrupt the smooth and normal operation of a computer system or server, collect private information or just gain unauthorized access to the system/server. Linux systems are known to have few malicious software compared to Windows, but that doesn’t mean Linux users should be at ease.
Most attacks on Linux are aimed at exploiting bugs in services like java containers and browsers, and its main aim is to change how the targeted service works and sometimes shut it completely.
One of the most dangerous attacks on a Linux system is when an attacker tries to get a user’s login credentials. When this is successful, the hacker can run anything they want and have access to confidential data. They can also attack other machines connected to the Linux server. To combat this, users can use Maldet to detect and clean malware from Linux and keep their systems clean.
Linux Malware Detect
Maldet is also known as the Linux Malware Detect (LMD). It is a Linux malware scanner that was developed to handle threats that are common with shared hosted environments. It uses threat data from network edge intrusion detection systems to extract malware that is actively being used in attacks and generates signatures for detection. While it sounds complicated, it is easy to use.
Installing Maldet
Open a terminal and run the command below to download the application:
wget http://www.rfxn.com/downloads/maldetect-current.tar.gz
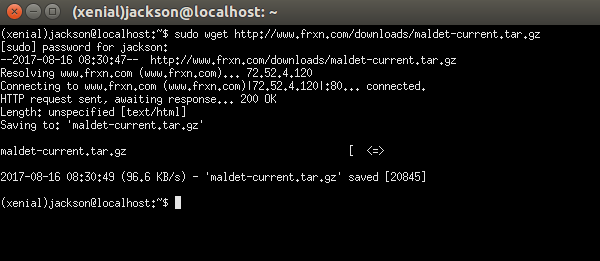
Unpack the downloaded archive file using the command below:
tar -xvf maldetect-current.tar.gz
Change the active folder to the folder containing the extracted maldetect file:
cd maldetect-x.y
“x.y” is the version number of the application. In this folder there is the “install.sh” script. The next step is to run the script using the following command:
sudo ./install.sh
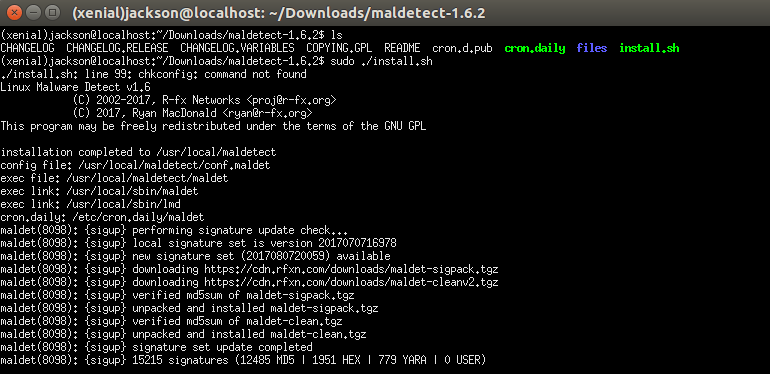
If the installation is successful, you will be notified. You will also be told where Maldet was installed. In my case it was installed as “/usr/local/maldetect.”
Configuration
After Maldet is installed, a configuration file is created in the Maldet directory called “conf.maldet.” To edit it, open it using a text editor.
gksu gedit /usr/local/maldetect/conf.maldet
Or you can use “nano” or “vi” to edit it in the terminal:
sudo nano /usr/local/maldetect/conf.maldet
Below is an example of options that may be set:
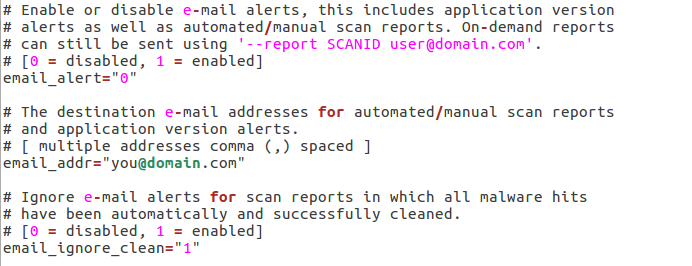
Email notification
Receive an email notification when malware is detected.
- Set “email_alert” to 1.
- Add your email address to the “email_addr” option.
- Change the “email_ignore_clean” to 1. This is used to ignore alerts being sent to you when malware is automatically cleaned.
Quarantine options
Actions to be taken when malware is detected:
- Set the “quarantine_hits” to 1 for the affected files to be automatically quarantined.
- Set the “quarantine_clean” to 1 to automatically clean the affected files. Setting this to 0 allows you to first inspect the files before cleaning them.
- Setting “quarantine_suspend_user” to 1 will suspend users whose accounts are affected, while the “quarantine_suspend_user_minuid” sets the minimum user id to be suspended. This is set to 500 by default but can be changed.
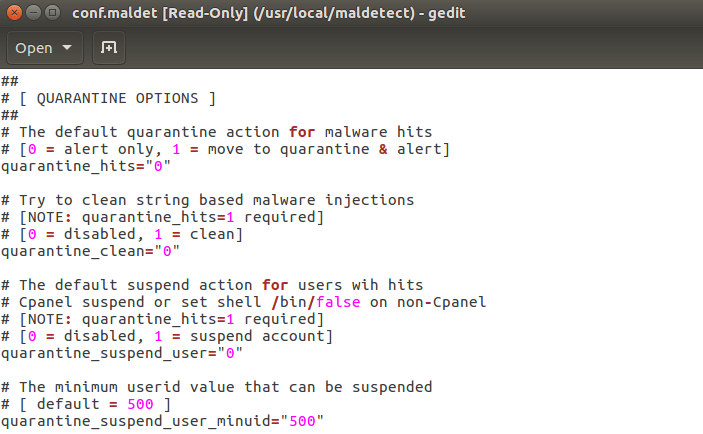
There are many other configuration options that you can go through and make the necessary changes. Once you are done with configuration, save and close the file.
Scanning Malware
You can run a basic scan manually or automate a scan to take place periodically.
To run a scan, run the following command:
sudo maldet --scan-all /folders/to/scan
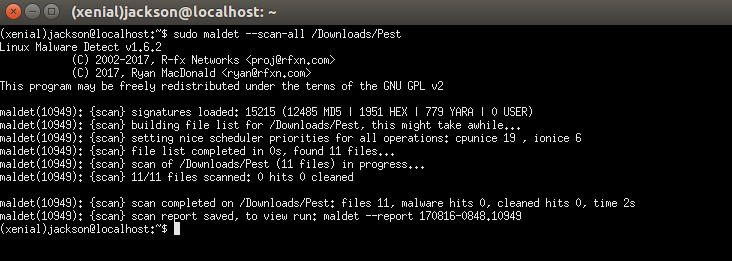
When this command is run, a list of files is built from the directories in the path and scanning of the files starts. Change the file path “/folders/to/scan” to the directory where you want Maldet to scan. After scanning, a report is generated and you can then see which files are affected.
How to Quarantine Affected Files
If you set the “quarantine_hits” to 1, Maldet will automatically move the affected files to quarantine. When it is set to 0, the generated report shows you the location of the affected files. You can then inspect the files and decide whether to clean them or not.
Restoring a File
Sometimes you might have a false positive leading to a file being quarantined for the wrong reason. To restore such a file, run the following command:
sudo maldet -restore FILENAME
Automatic Scan
During the installation of Maldet, a cronjob feature is also installed at “/etc/cron.daily/maldet.” This will scan the home directories as well as any files/folders that were recently changed on a daily basis. It will always notify you of any malware through the email address in the configuration file.
Conclusion
Many people are saying that Linux systems are immune to malware, but that is not true. You can be tricked into installing malicious software, or malware can even be spread through emails, and this would cause damage to your system. There are also many other vulnerabilities where hackers try to gain unauthorized access, making the system insecure. To stay safe, you can use Maldet to keep your system clean. Other measures that you can take include setting up network monitoring and firewall rules among others.