If you’ve ever looked at the authentication logs for your server, then you know that any server connected to the Internet is under a constant barrage of login attempts from hackers.
Even if your server is a completely unknown hobby server, automated scripts will find it and continually try to brute force their way in using SSH. Although they’re not likely to get in as long as you’re using complex passwords or other security measures, there’s still always the chance that they could succeed.
Luckily, there’s a useful and fun way to trap these hackers in your server and keep them too distracted to cause any trouble.
What Is an SSH Honeypot?
To put it simply, an SSH honeypot is a decoy meant to look like low-hanging fruit to attract cybercriminals and bait them into targeting it. But it’s not an actual target, and the hacker often doesn’t realize it until it’s too late.

A honeypot can take on many forms and have many different uses. Sometimes they are little more than a distraction, but other times they are used to gather information about the attacker.
Many government agencies use honeypots to catch criminals, luring them into attacking, only to gather intel on them in order to catch them later. But honeypots can also be used by system administrators working for companies or even just hobbyists who run a Linux server for fun.
Also read: How to Set Up and Use SSH in Linux
Why Use an SSH Honeypot?
There are many reasons someone may want to implement an SSH honeypot on their server. In some cases, you may want to use it so you can block any future connections from them. Perhaps you simply wish to lure them away from real targets on your system. Or it may be for educational purposes: to help learn how the attacks work.
For the purposes of this guide, we are primarily using the honeypot as a distraction. Specifically, it will distract the hacker from attacking more vulnerable parts of your server as well as keep them too busy to attack someone else’s server.
And, in this case at least, the method used will be good for a laugh or two as well.
Trapped in SSH
Essentially, what we want to do is trap the hacker when they attempt to brute force the SSH login. There are a few ways to do this, but one of the simplest is to slowly send them a very long SSH banner.
This way, the hacker’s automated script will be stuck waiting for a banner. This can last hours, if not days or weeks. Since the script is automated, the hacker likely isn’t paying much attention to it and won’t notice that it’s stuck until much time has already passed.
This is sometimes playfully referred to as an “SSH tarpit,” as the hacker’s script gets stuck in it and isn’t able to get out on its own.
This does require you to know some basic SSH usage. If you’re not sure how to use SSH, then read this guide to get you started.
Also read: How to Show All Active SSH Connections in Linux
endlessh
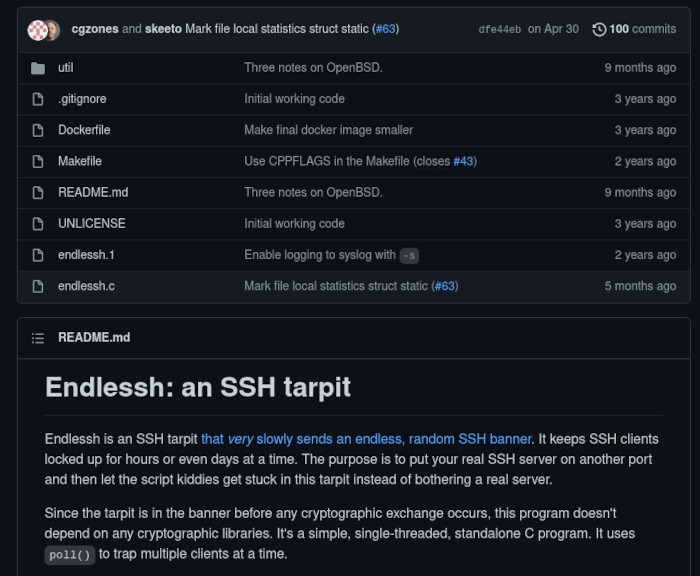
The program that we’re using to accomplish this is called endlessh and is made by skeeto.
Once you’ve logged in to your server, clone the repository. (You need to have git installed it.)
git clone https://github.com/skeeto/endlessh
Now that you have the repository on your server, you’ll need to switch to that directory and compile it.
cd endlessh make
Some errors may come up while trying to compile the program. This most likely means you’re missing a dependency that the program needs to compile. You’ll need to check which dependency it says is missing, then install it with your distribution’s package manager.
Once you have the program to compile, you’ll want to move it to your bin directory so that it’s in your path.
sudo mv endlessh /usr/local/bin
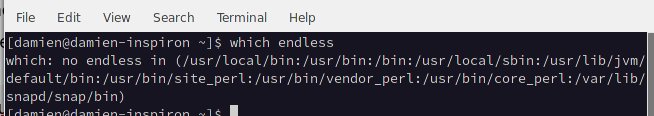
You’ll want to double-check to make sure it’s detected in your path.
which endless
It should print out the/usr/local/bin/endlessh path. If this isn’t the case, you’ll want to make sure it was moved to the correct directory.
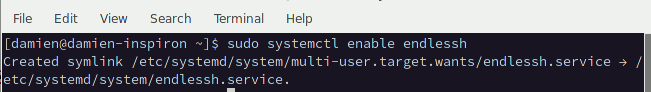
After that, turn the program into a service daemon so that it can function as a systemd service.
sudo cp util/endlessh.service /etc/systemd/system/
once that’s finished, enable the service so that it will run in the background.
sudo systemctl enable endlessh
By default, endlessh will only work on ports above 1024, but we want it to use the default SSH port so that we can fool hackers into trying to attack it. In order to do this, we need to edit the service file.
This example uses nano to edit the configuration file, but feel free to use your text editor of choice.
sudo nano /etc/systemd/system/endlessh.service
Once the file is open, uncomment the following line by removing the # character:
#AmbientCapabilities=CAP_NET_BIND_SERVICE
Then add a # to the start of this line:
PrivateUsers=true
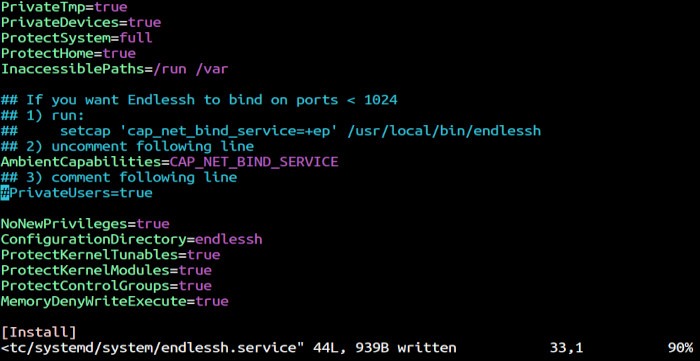
Save the file and run this command:
sudo setcap 'cap_net_bind_service=+ep' /usr/local/bin/endlessh
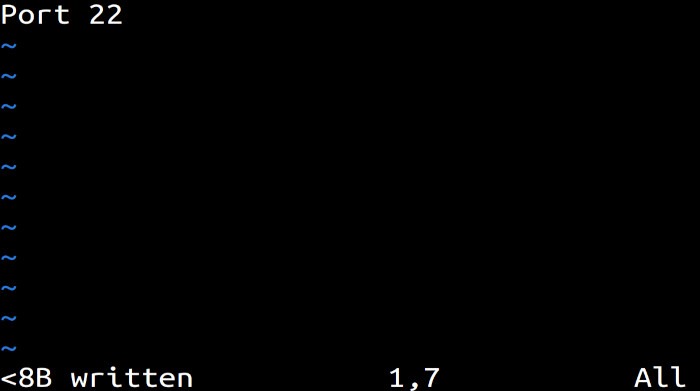
You will need to create and set up a configuration file so that endlessh knows what port it should run on. You’ll need to make a new directory for it first, then create the configuration file.
sudo mkdir -p /etc/endlessh sudo vim /etc/endlessh/config
The config file will only need a single line in it. This will tell endlessh to run on port 22, which is the default port for SSH. We do this so that it’s a more alluring target for hackers. They will see that the default SSH port is open, then try to break into it.
Enter the following into your config file:
Port 22
You’ll need to start up the endlessh service.
sudo systemctl start endlessh
That’s all there is to it! You’ll now have endlessh running on your default SSH port and are already trapping hackers.
Testing It Out
Just to make sure the honeypot is working as intended, let’s pretend to be a hacker for a second and try to gain access to SSH on your server.
ssh root@
As long as everything has been set up correctly, you should see that the ssh command is stuck and not doing anything. Let’s take a look to see what is actually happening when you (or an actual hacker) issues this command.
Repeat the same command but add the -vvv flag to use the verbose option.
ssh -vvv root@
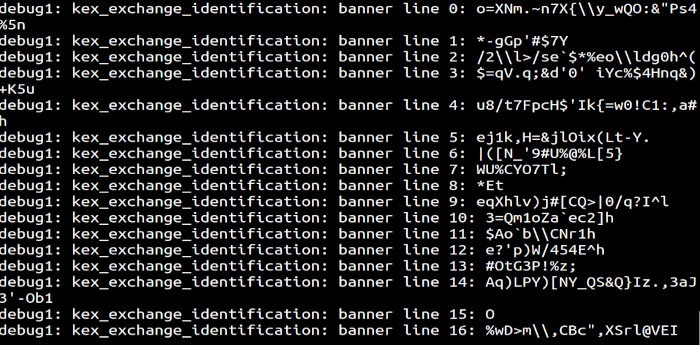
It should now be apparent just how this little tool is trapping you and keeping you from accessing SSH on your server. It is slowly, line by line, sending a very large SSH banner to the client.
And of course, since a hacke has this automated with a bot, they won’t realize this is happening until after you’ve wasted hours, if not days, of their time.
Frequently Asked Questions
1. Will this prevent hackers from accessing SSH?
Although it is a pretty good deterrent, it’s not guaranteed to stop hackers completely. An attentive hacker will eventually notice that you’ve created a honeypot on your server and may try different ports to access SSH on your server.
However, this should be enough to prevent hackers who are only looking for the low-hanging fruit.
2. How do I use SSH if this program is running on the default port?
You will need to change the port SSH runs on. This is good practice even if you didn’t have a honeypot on your server, since hackers will always try default ports first before scanning for others.
3. Are there other options I can add to the config file?
Yes, there are several other settings you can change, including changing the delay speed.
You can see a list of options in the sample configuration file on the Github repository.
Final Words
Now that you’ve learned how to set up a honeypot on your server to trap hackers and keep them distracted so that they can’t attack anything else, it is far from the only way to secure SSH access to your server.
Check out this article showing how to use encryption keys to log in to SSH to help secure your server even further.
Image credit: Honey in pot, honeycomb and stick by Yay Images








