Phishing attacks on cell phones aren’t new but are becoming more sophisticated because of new attack vectors. These are no longer just about fake sites grabbing fonts and color schemes to mock the originals. Scammers are now big on stealing social media data and overriding one-time password (OTP) security.
Here we will discuss traditional and advanced mobile phishing attacks and the best ways to combat them.
Traditional Phone Phishing Attacks
1. SMS Phishing
SMS phishing attacks have been around for so many years. The methods haven’t changed much – they still focus on grabbing the target’s attention with incentives, fear or a snarky comment. Apart from bank account and credit card information, phishing criminals are after Apple ID logins, crypto-currency and PayPal accounts. All this information can be sold for a profit in the dark web. Currently, the going rate for an Apple ID is only $15, which goes to show how many of them are easily available. If it’s a banking fraud, the con artists would probably call first to confirm the OTP.
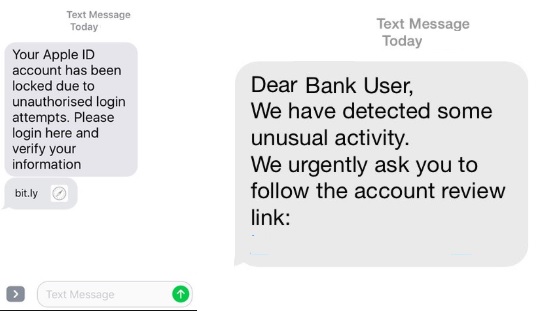
How to combat it: Do not click on any links which force you to act in a hurry. Legitimate companies never harass you in this manner. Besides, there may be phone malware riding on those links.
2. Robocalls
Voice call-based phishing attempts (called “vishing”) are slightly more brazen than SMS. The robocallers have the latest technologies at their disposal: caller ID spoofs, remote auto-dialers, area code-based numbers and access to your personal information. You only have to enter your credit card information after they tell you to dial “1.”

How to combat it: certain mobile apps such as Truecaller and Robokiller can help you automatically stop these robocalls in their tracks. If it’s a real human con artist, simply hang up and don’t be polite.
3. Social Media Phishing
After the Cambridge Analytica scandal, it doesn’t surprise anyone that social media websites have become target-rich environments for phishing attacks. Social media scammers can impersonate celebrities, your best friends and even your family members with all the data you’re handing out to them on a platter. Cryptocurrency scammers prowl for potential victims after checking their social media posts.

How to combat it: keep your wits about you, and do not overshare your personal information on social media. Do not brag about things such as your online bitcoin collection.
Also read: 4 Most Common Cyber Attacks Used Against Older People in 2020
Advanced Phone Phishing Attacks
1. Phone Number “Port Out”
Phone number “port out” attacks are among the latest mobile phishing scams, and even telecom companies are issuing advisories (see below). They basically strike at the heart of your bank account’s security system: two-factor authentication. As it turns out, the growing dependence on OTPs by banks and credit card companies as a second layer of security isn’t exactly foolproof.
Attackers collect personal information about you such as phone numbers, date of birth, etc., and pretend to be “you” to port your SIM number to another carrier. This is increasingly done in those carrier stores where the security and verification is lax. After taking control of your phone number for a few hours or even days, they can use it to receive OTPs from your banks. Apart from financial fraud, drug dealers are using “ported out” numbers to cover their tracks.

How to combat it: There is really not much you can do if a phisher impersonates your phone number. But you might get a few hours of lead time before something bad happens, so it is important to stay vigilant. If you find your phone is unable to do basic functions such as calling or sending texts, suspect that it has been compromised. Inform your banks and ask them to freeze your accounts. Inform your carrier to block the SIM card immediately.
2. Cell Phone Cloning
Cell phone cloning attacks are the latest addition to the mobile phishing family. In the past it was done using “SIM swapping” to tap into a phone’s IMEI number. Nowadays it can be done even without touching the device. A simple Google search on “how to clone a phone wirelessly” offers some surprisingly easy tutorials.
One of these methods is through Bluetooth hacking. Using a downloaded software, the attackers can gain access to another Bluetooth device in its proximity that is on. After connecting, the activities of the target phone, including keystrokes, can be monitored remotely. In fact, it’s not even illegal because there are parental control solutions which allow you to monitor other phones remotely.

How to combat it: This is really hard to protect against. The best thing you can do is to only install apps from verified sources and look through all permissions that each app requests. If an app is asking for permission to a function that it don’t need, blacklist or uninstall it immediately.
Final Word
Given the growing prevalence of cell phone phishing attacks, it’s fair to assume that nothing short of constant vigilance will help you stay safe.
Have you been a victim of a phone phishing attack? Please share your experiences.