A checksum is a string of text derived from the software using a hash function. No two checksum should be the same. When downloading software from the Internet, one way to verify its integrity is to compare its checksum with the one provided by the website. If they tally, then the software is genuine and has not been tampered with. Here we will show you how to check and verify checksums in Linux.
While this can be easily done in the terminal, you will learn here how you can check and verify checksums with a graphical tool: the ultra-simple GtkHash.
Also read: Hashing vs. Encryption: How Your Password Is Being Stored in Server
Installation
For most Linux distributions, you can find GtkHash in the package manager or Software Center. If you are on Ubuntu or a compatible distribution and installing from the terminal, you can install GtkHash with:
sudo apt install gtkhash
For openSUSE, you will have to add its repository before installing it. Look for more information here.
On Arch and Manjaro:
sudo pacman -S gtkhash
After it’s installed, find it among the rest of your installed applications and run it.
Create Hashes
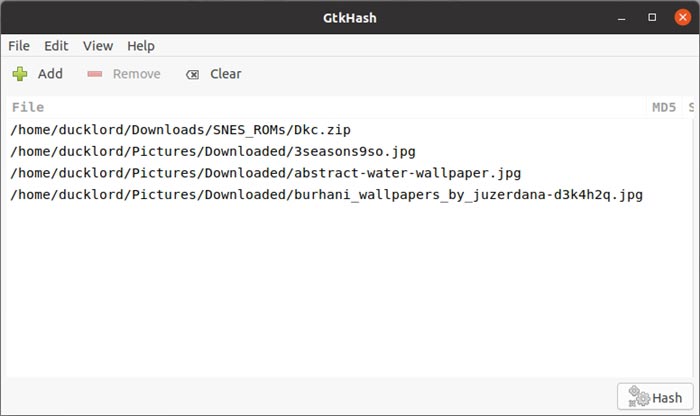
GtkHash’s interface is pretty straightforward. To calculate hashes for one or more files, click on the friendly “Add” button on the top left.

Point the requester to the location of your files and select them. You can select multiple files by holding down the Ctrl key while clicking on them. Then, click on the “Open” button on the top right to complete the command.
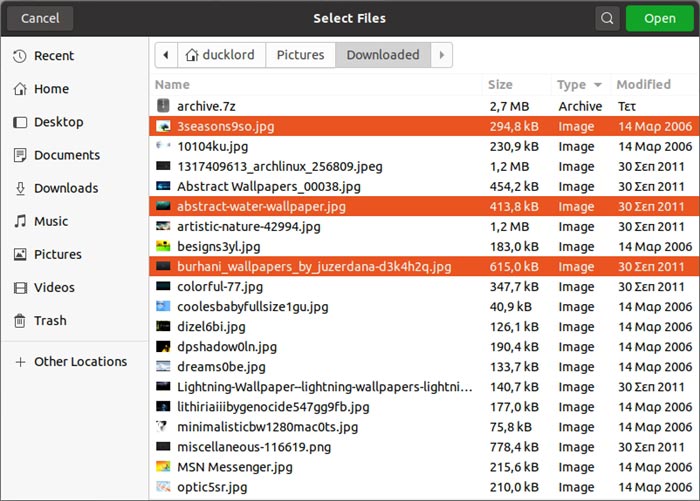
GtkHash’s list will be populated by the files you selected. If you wish, you can add more files by repeating the previous step.
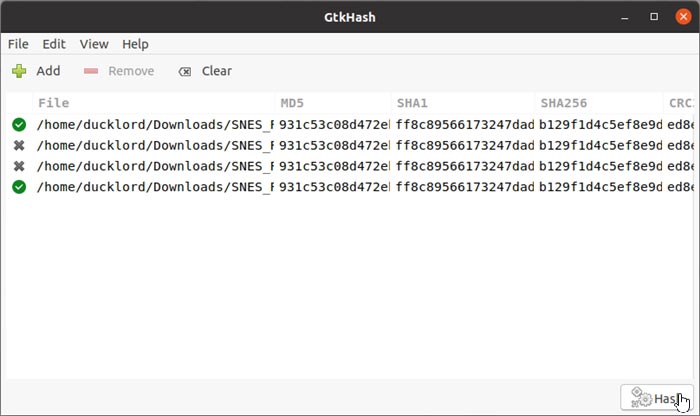
Click on the “Hash” button on the bottom right of GtkHash’s window to calculate the hashes for all the files in the list.
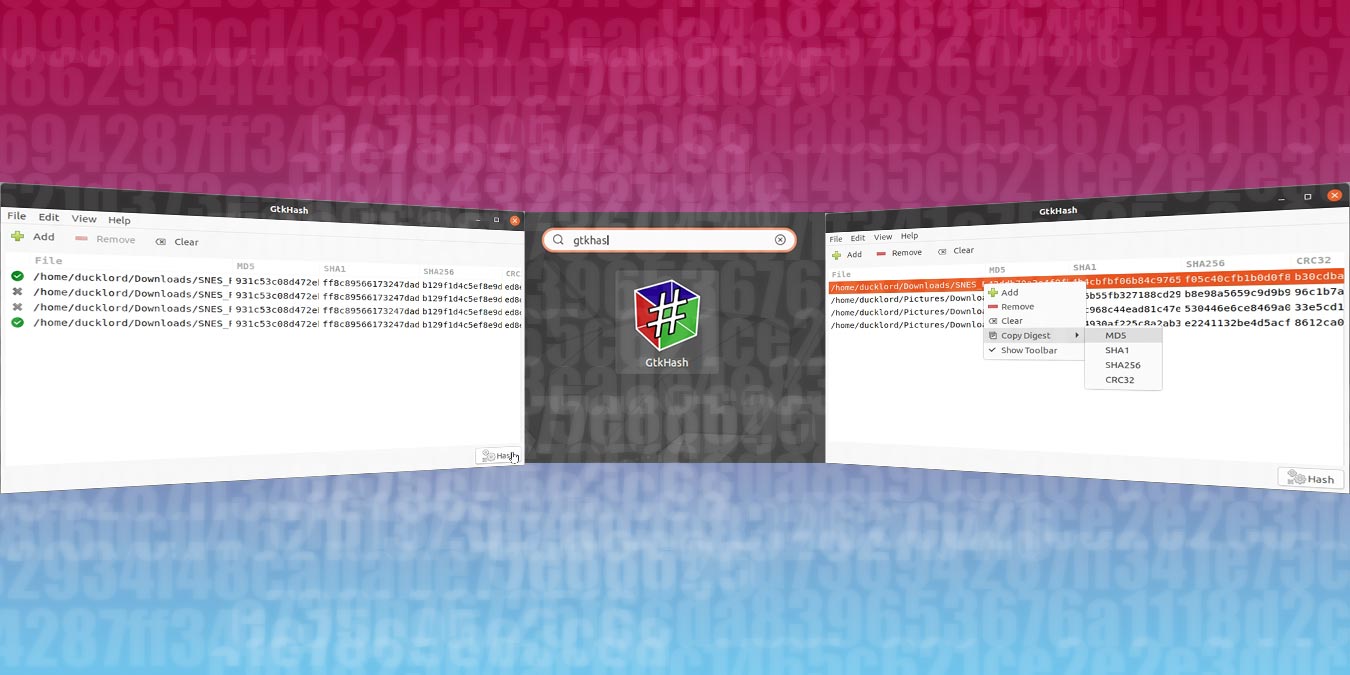
GtkHash calculates multiple hash types by default and will present them in columns next to each file.
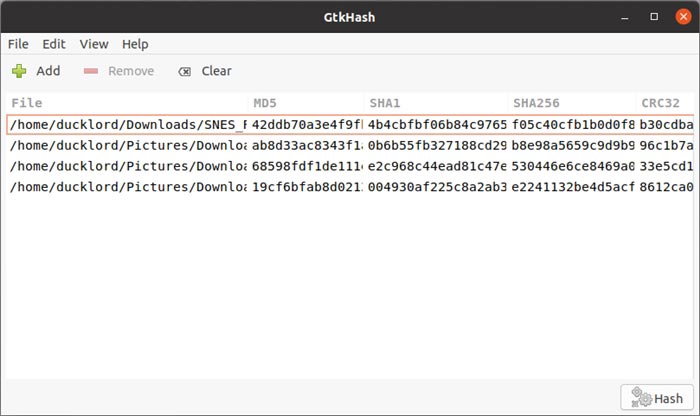
To copy a file’s hash to the clipboard, right-click on the file and select your preferred hash type from the “Copy Digest” submenu. Then, paste the copied hash somewhere for future reference.
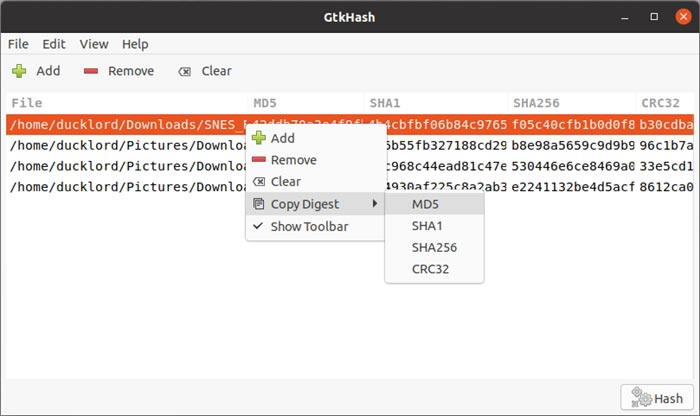
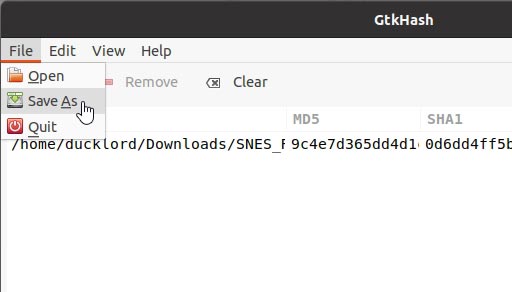
Alternatively, you can save the hash to a file through “File -> Save As.”
Check Hashes
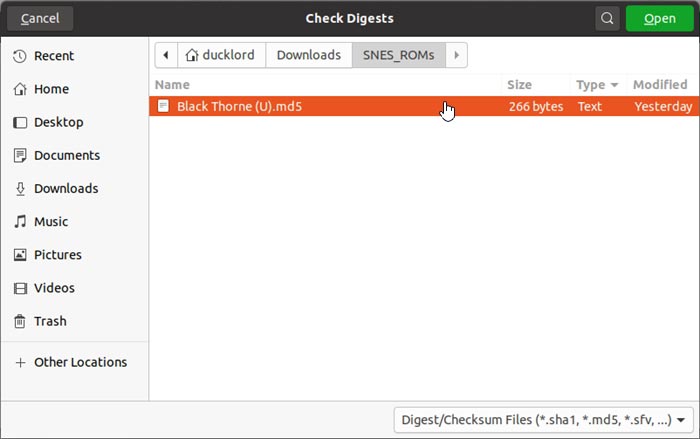
To check a file’s data integrity with GtkHash, select “File -> Open” an choose the hash file that accompanied your main file. The hash file will usually have a “sha1,” “md5,” or “sfv” extension, and GtkHash supports all the popular ones.
When the file is loaded, click on the “Hash” button on the bottom right. GtkHash will calculate and compare the file’s hash with the reported one and present you with the results. As you can see in our screenshot, we had two matches and two failures.
More Hashes
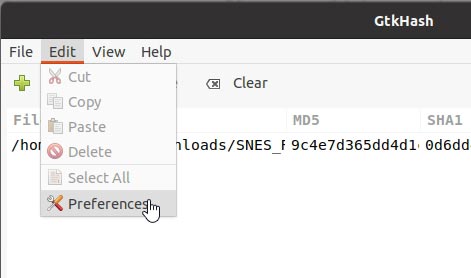
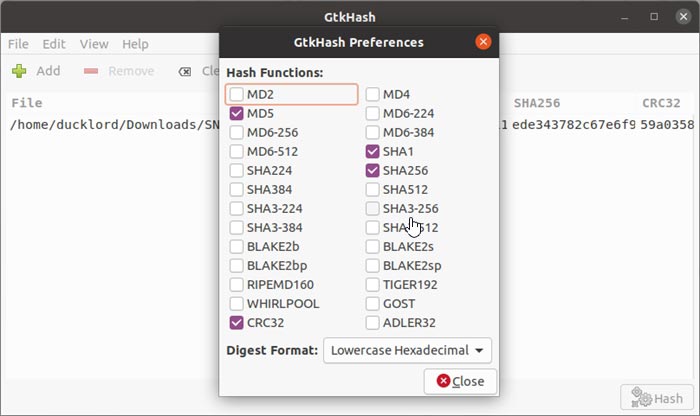
GtkHash comes with the most popular hashing algorithms enabled, but they’re not the only ones it supports. For more, visit “Edit -> Preferences.”
You can choose from over two dozen different hash functions, among which you will probably find the one you prefer.
Comparing Checksum from the Terminal
If you are in a server environment, the only way to compare a checksum is via the terminal. Luckily, checking and creating file hashes on a terminal is just as easy as using a GUI. Most distributions come with a set of tools for the job. Some of the most popular ones are:
- md5sum
- shasum
- sha256sum
- sha384sum
- sha512sum
Their use is simple since they work in precisely the same way: you type their name, then the name of the file for which you want to calculate a hash. For example, to calculate the SHA-512 hash for an Arch Linux installation ISO we’ve downloaded, we used:
sha512sum archlinux-2020.05.01-x86_64.iso
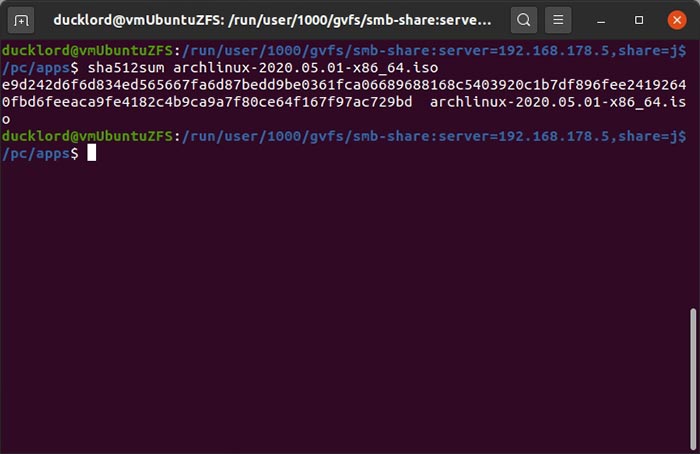
In the above, sha512sum was the command for the hash algorithm we’ve decided to use. After some waiting, we saw the SHA-512 hash on our screen.
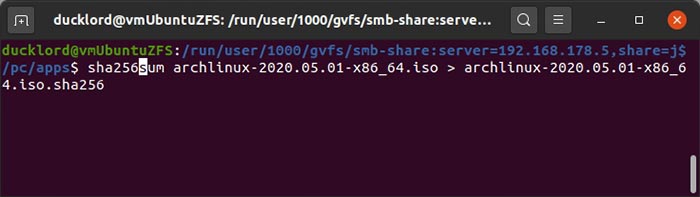
In the future we may want to re-check our file, so we decided to output the results to a file instead of our screen. The hash commands don’t offer such functionality since it’s only a redirect away in Linux. By using a > symbol after the command and a filename, the output of the command is saved in the file instead of being printed on-screen. You can also use sha256sum:
sha256sum archlinux-2020.05.01-x86_64.iso > archlinux-2020.05.01-x86_64.iso.sha256
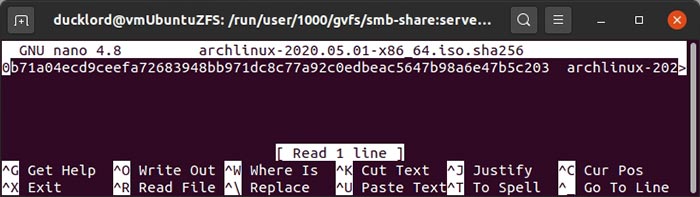
This will output the results to a typical text file that you can check out. In it, you’ll find the file’s hash followed by its filename.
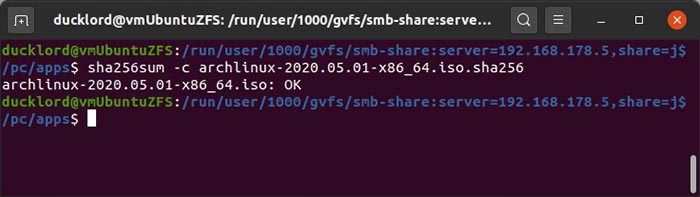
Checking a file against its hash only requires you to add a -c switch to the command and to use the hash file instead of the actual file. In other words, something like this:
sha256sum -c archlinux-2020.05.01-x86_64.iso.sha256
While it is easy to verify checksums in Linux, it’s not realistic to check hashes for every single file. It’s something you should do for those sensitive data or the Linux ISO you downloaded from the Web. If you are using Mac, the same method applies.