Ransomware remains one of the world’s most dangerous threats to computer systems. A ransomware attack encrypts all your data, preventing you from accessing it unless you pay a ransom to its creators. These attacks are often devastating to small businesses and individuals who cannot afford to pay the ransom. Thanks to research from many security firms worldwide, you can now decrypt your data without paying hackers. Let’s take a look at some decryption tools that will allow you to unlock and restore your data.
Also read: Do I Need Antivirus Software If I Have Windows Defender?
A Few Things to Note
Before we dive into the tools, keep the following in mind:
- Ransomware isn’t like other types of malware. There’s no one-size-fits-all solution. For you to decrypt any ransomware, you must identify it correctly, which is usually quite simple to do. Ransomware will identify itself either by its extension file or warning screen.
- Each ransomware has its own unique decryption tool. Some tools may decrypt ransomware of the same family, but no single tool can decrypt all ransomware.
- Each decryption tool is unique. Different companies employ varying methods with their tools. Make sure to read all instructions for each tool carefully before using it on your PC. If you get these instructions wrong, you may make your problem worse.
- Even after decrypting ransomware, you’re still susceptible to reinfection. To prevent that risk from reoccurring, first scan your system with robust and up-to-date antivirus software. Ensure you get rid of all threats and potentially unwanted software (PUPs) before decrypting your files.
Also read: 11 Legitimate Windows Processes that Can Look Like Malware
1. No Ransom by Kaspersky
No Ransom is a Kaspersky project that offers free and up-to-date decryption and ransomware removal tools. It contains six different tools, and each can be downloaded for free from the website.

These six tools are:
- Shade Decryptor: decrypts all versions of Shade.
- Rakhni Decryptor: decrypts files affected by CryptoKluchen, Democry, TeslaCrypt versions 3 and 4, Dharma, Jaff, Crysis versions 2 and 3, Rakhni, Aurora.
- Rannoh Decryptor: this tool decrypts Rannoh, Fury, AutoIt, Cryakl, Crybola, CryptXXX.
- CoinVault Decryptor: this tool resulted from a collaboration between The National High Tech Crime Unit of the Netherlands’ police. It decrypts Coinvault and BitCryptor.
- Wildfire Decryptor: this tool decrypts all files locked by the Wildfire ransomware.
- Xorist Decryptor: this tool decrypts files locked by the Xorist and Vandev ransomware.
Also read: How to Enable Ransomware Protection in Windows
2. Avast Free Ransomware Decryption Tools
Avast also offers a collection of decryption tools for about 27 different ransomware.

Downloadable from the website are fixes for common ransomware, such as:
- Apocalypse
- Alcatraz Locker
- Bart
- CrySiS
- Jigsaw
- Legion
- TeslaCrypt
All these tools are free downloads, and you can use them to unlock your files once you’re attacked. Avast also has resources that teach you about different ransomware attacks and the encryption and encoding of each.
Also read: Hysolate: Protect Yourself by Running Apps in an Isolated Environment
3. No More Ransom Decryption Tools
Like the Kaspersky and Avast projects, the No More Ransom project helps victims of ransomware attacks retrieve their encrypted data without paying ransoms. This project began as a collaboration between Kaspersky, McAfee, Europol’s European Cybercrime Center, and the National High Tech Crime Unit of the Netherlands’ Police.
You’ll find free tools to decrypt over 50 different ransomware on the website. This includes:
- Ragnarok.
- NoobCrypt
- Megalocker
- Fonix
- Darkside
You’ll also find information on how to prevent future ransomware attacks on your data.
4. Emsisoft Decryption Tools
Emsisoft can help you identify 1049 different ransomware strains. Beyond that, they also offer free ransomware decryption tools that will unlock your files without ransom.

Emsisoft lets you upload an infected file or ransom note to its website to help identify the ransomware. After that, their team will help you decrypt your files.
You can use Emsisoft Decryptors on many ransomware, including:
- Ragnarok
- Avaddon
- Ziggy
- Cyborg
- Crypt32
- KokoKrypt
Also read: Emsisoft Anti-Malware Review: Feature-Rich & Affordable
5. Bitdefender Decryptor Tools
Bitdefender also offers decryption tools for many ransomware types. You can get decryptors for:
- Fonix
- Darkside
- WannaRen
- GoGoogle
- Shade
- Paradise
Besides that, Bitdefender also offers anti-ransomware that blocks attacks and intercepts any attempt to encrypt your data.
6. McAfee Ransomware Recover
This recovery software is a free tool by McAfee that can decrypt ransomware. The company keeps it up to date with decryption logic and keys that you can use to unlock files, documents, databases, and applications that ransomware has encrypted on your device.

McAfee also keeps the decryption framework free for the security community. Doing so saves developers the time it would take to build their own decryption frameworks.
Also read: 6 Best Tips to Protect Your Gmail Account Security
7. AVG Ransomware Decryption Tools
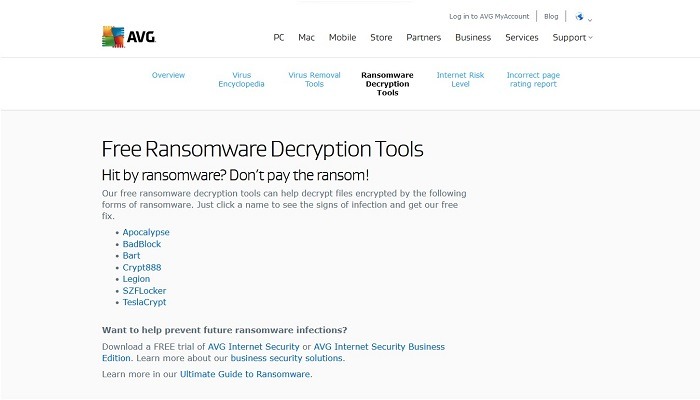
AVG is another excellent place to get decryption tools if your PC gets hit by ransomware. Its tools can decrypt some common ransomware such as:
- Legion
- TeslaCrypt
- Bart
- BadBlock
- Apocalypse
- SZFLocker
- Crypt888
Like all of the other tools, AVG decryptor tools are free to download.
Tips to Prevent Ransomware Attacks
Ransomware attacks can be costly, especially to your personal and business data. Here’s the good news: you can now fix most of these attacks using freely available tools. However, that’s not enough to keep you safe. Preventing future attacks is just as essential as finding solutions for them.
These tips will help you reduce the risk of ransomware attacks and data loss.
1. Back Up Your Data in the Cloud
One of the best practices is to back up essential data in the cloud. Although you can opt for an external storage device, the risk of data loss is much lower with cloud storage.
Also, external storage devices are susceptible to ransomware attacks if you connect them to an infected computer.
2. Avoid Unsafe Links and Websites
Ransomware and other malware often spread through spam messages and unsafe websites. Stay away from unfamiliar websites or links. Also, block pop-ups from unknown sources and websites.
3. Avoid Opening Suspicious Email Attachments
Email attachments are a common way hackers attack computer systems. To prevent the risk of malware, ensure you open emails from trusted senders only.
You can also install email scanning software to filter out potential threats and scan any downloaded attachments with an up-to-date antivirus to delete any attached ransomware.
Also read: 9 Firefox Addons to Protect Your Online Privacy
4. Scan Your PC and Peripheral Devices Frequently
Another of the best practices is to scan and clean any USB sticks with an antivirus before opening them. Doing this quarantines and deletes any malware that may infect your PC. Also, avoid using your USB devices on public computers or devices you don’t trust.
5. Keep Your PC and Antivirus Up to Date
Always keep your computer up to date. Operating system updates often come with security patches that seal potential vulnerabilities malicious actors can exploit. Besides, keeping your antivirus software up to date protects your PC from emerging threats, including newer ransomware attacks.
6. Use VPNs On Public Wi-Fi Networks
If you’re on campus or at the airport and need to use Wi-Fi, ensure you have a VPN installed on your PC. Using a VPN on public networks secures your PC from attempted hacks and prevents data and identity theft by malicious actors.
7. Download from Trusted Sources
Whether you’re downloading documents, movies, or videos, get them from trusted sources only. Untrusted sources can infect your computer with ransomware and other malware types.
Ensure the website you’re visiting uses both Secure HTTP (or HTTPS) and has an SSL certificate. If you see a locked padlock next to the link in the address bar, the website is secure.
Also read: How to Set Up OpenVPN in Windows
Frequently Asked Questions
1. Why do attackers use ransomware?
Unlike many other types of malware, ransomware attacks have a financial incentive for hackers. Once they deny you access to your files, hackers demand a ransom payment to restore your access.
2. How is ransomware installed?
In many cases, ransomware attacks come in phishing emails with infected attachments. Another common method is drive-by downloads. Once you open the malicious attachment, it installs ransomware on your system.
3. Can ransomware spread through Wi-Fi?
Yes, ransomware can spread across computers through a Wi-Fi network. Like a computer worm, ransomware can also spread across different Wi-Fi networks within the same area.








