SSL is also known as Secure Socket Layer protocol. It was created by Netscape to secure transactions between web servers and browsers. SSL protocol uses a Certificate Authority (CA) to identify one end or both ends of the transactions. All communications sent over regular HTTP connections are in plain text, and any hacker can access the connection between your browser and the website and read sensitive information like credit card details or your social security number. SSL is used is to keep sensitive information sent across the Internet encrypted, so the information becomes unreadable to everyone.
Also read: How to Generate SSL Certificates on Linux Using OpenSSL
Self-signed Certificate vs. Commercial Certificate
Self-signed Certificate is signed by its owner. It is generally used for testing local servers and development environment. Although self-signed certificates provide the same level of security between website and browser, most web browsers will always display a security alert message that the website certificate is self-signed and cannot be trusted, as it is not signed by the Certificate authority.
Commercial Certificate is an authorized certificate issued by a trusted certificate authority. Signed certificate is mostly used in a production environment.
In this article I am going to explain how to create a self-signed SSL certificate for Apache which will allow you to encrypt traffic to your Apache web server.
Configure Apache to Support SSL
By default, Openssl is installed in Ubuntu 14.04. This module provides SSL support to Apache. It is disabled by default, so you need to enable the SSL module first.
You can enable the SSL module by running:
sudo a2enmod ssl
After you have enabled SSL, you’ll have to restart the Apache service for the change to be recognized.
sudo service apache2 restart
Also read: How to Get a Free SSL Certificate for Your WordPress Website
Generate a Self-signed Certificate
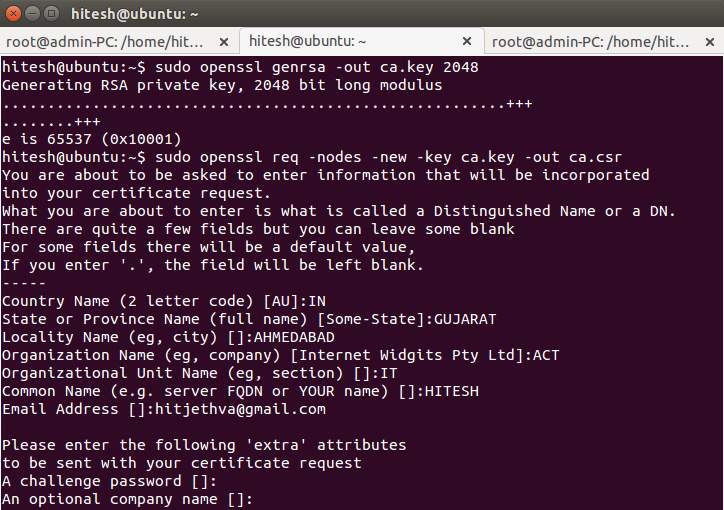
The first step is certificate creation. For testing purposes, or for small LANs, you need to generate a private key (ca.key) with 2048 bit encryption.
To do this, run:
sudo openssl genrsa -out ca.key 2048
Then generate a certificate signing request (ca.csr) using the following command:
sudo openssl req -nodes -new -key ca.key -out ca.csr
Lastly, generate a self-signed certificate (ca.crt) of X509 type valid for 365 keys.
sudo openssl x509 -req -days 365 -in ca.csr -signkey ca.key -out ca.crt
Create a directory to place the certificate files we have created.
sudo mkdir /etc/apache2/ssl
Next, copy all certificate files to the “/etc/apache2/ssl” directory.
sudo cp ca.crt ca.key ca.csr /etc/apache2/ssl/
Configure Apache to Use the SSL Certificate:
Now all the certificates are ready. The next thing to do is to set up the Apache to display the new certificate.
For this, you need to enable SSL support on the Apache default virtual host file located in the /etc/apache2/sites-enable/ directory.
You can do this by editing the Apache default virtual host config file.
sudo nano /etc/apache2/sites-enable/000-default.conf
Comment out all the lines by adding a “#” in front of each line and add the following lines:
ServerAdmin webmaster@localhost DocumentRoot /var/www/html ErrorLog ${APACHE_LOG_DIR}/error.log CustomLog ${APACHE_LOG_DIR}/access.log combined SSLEngine on SSLCertificateFile /etc/apache2/ssl/ca.crt SSLCertificateKeyFile /etc/apache2/ssl/ca.key
Save and close the file, then restart Apache.
sudo /etc/init.d/apache2 restart
This should enable your new virtual host which will serve encrypted content using the SSL certificate you created.
Testing Apache (HTTPS) Server:
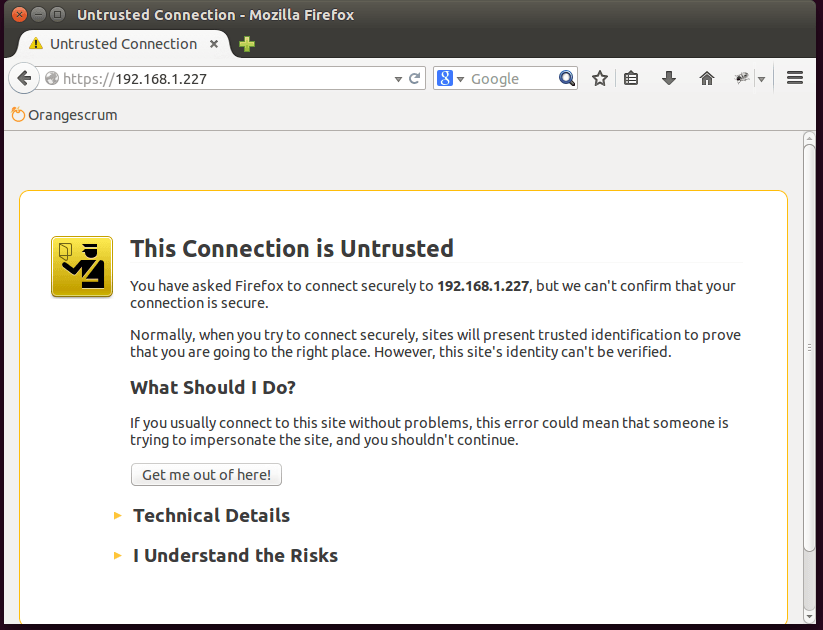
To verify the Apache (HTTPS) web server, open your web browser and type your server IP Address (with “https://,” for example: “https://192.168.1.227”).
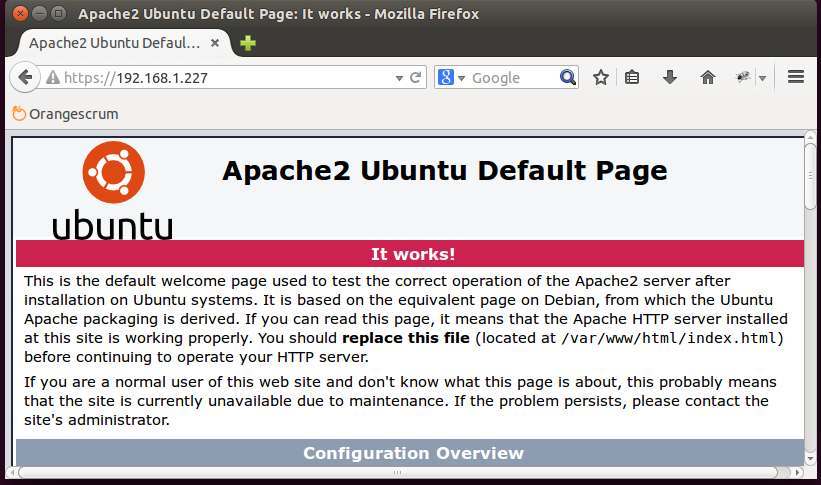
An error should appear on your browser, and you must manually accept the certificate. The error message shows up because we are using a self-signed certificate instead of certificate signed by a certificate authority that the browser trusts, and the browser is unable to verify the identity of the server that you are trying to connect to. Once you add an exception to the browser’s identity verification, you should see a Ubuntu test page for your newly secure site.
Conclusion
Now, you have SSL enabled on your Apache server. This will help to secure communication between your Apache server and clients. If you want to host a public site with SSL support, then you need to purchase an SSL certificate from a trusted certificate authority.







