If you have been using a computer long enough, you might have come across a number of suggestions like never try to access your personal or financial information from a public computer or any system that is not yours. One of the reasons for this suggestion is the threat of keylogging where everything you see and type is automatically recorded and sent to a third party without your knowledge. This, in turn, provides the attacker with plenty of access to your personal and financial information. In fact, the keyloggers play a major role in online identity theft.
What a Keylogger Is and What It Can Do
As you can tell from the name itself, a keylogger is nothing but software (unless it is a hardware keylogger) that monitors, records and sends the data over to a third party. Often, this is done without your knowledge leading to data and identity theft. Over a period of time, keyloggers have grown in functionality and can monitor and record a wide range of your activities that can seriously damage you. The below list includes but is not limited to the capabilities of the most modern keyloggers.
- Stay invisible to the user so that they cannot view or uninstall it
- Monitor keyboard presses and mouse activity
- Control various system settings without the knowledge of the user (often with admin rights)
- Monitor file and folder activities
- Capture login details of email accounts, bank accounts and other online and offline accounts
- Monitor clipboard activities
- Take control of your microphone and webcam
- Take screenshots of your desktop activity
- Send collected data via FTP, LAN, email, etc.
Protect Yourself from Keylogging
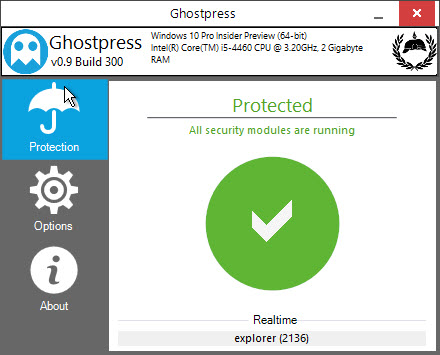
To protect yourself from a software keylogger, you can use an anti-keylogger software like GhostPress which encrypts all your keystrokes. The good things about GhostPress are that it is free, small, and portable which make it a good choice when you want to use a public computer or a system that is not yours.
To start, head over to the official site and download the software. Once downloaded, extract the contents of the zip file.
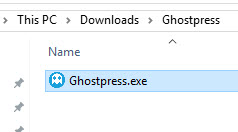
Now, execute the EXE file in the folder. Being a portable application, there is no need for you to install it. Once the application has been launched, it automatically encrypts any and all keystrokes. There is no need for you to mess with any settings.
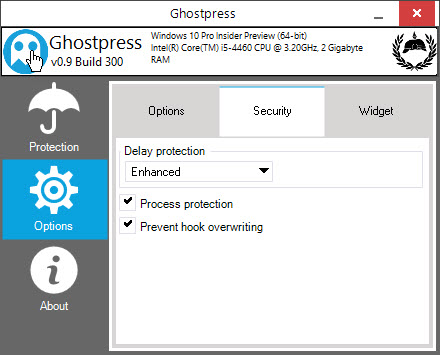
If you want to further increase the protection then you can do that by simply selecting “Options” appearing on the left panel and then navigating to the “Security” tab. Here, select the checkbox “Process Protection” and optionally, set the Delay Protection to “Enhanced.” When the Delay Protection option is enabled, all your keystrokes will be randomly delayed for a short time so that the keylogger software cannot detect who you are based on your typing behaviour.
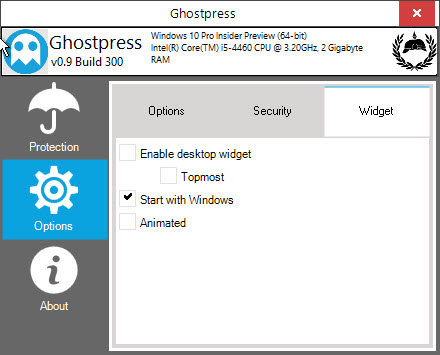
If you want to regularly use this software on your machine, then navigate to the “Widget” tab and select the “Start with Windows” checkbox. When enabled, GhostPress automatically launches on system startup eliminating the need to manually launch it every time.
If you want more advanced protection against webcam hijacking, system screenshots, remote access, clipboard hijacking, etc., then you need to look at premium software like Zemana AntiLogger.
Obviously, all the software you use can only protects you from the software keyloggers. If the attacker is using a hardware keylogger which sits between the keyboard and the system, all your keystrokes can still be leaked. So be extra cautious when you can using public computers like in Internet cafes.
Do comment below sharing your favorite anti-keylogger software.








