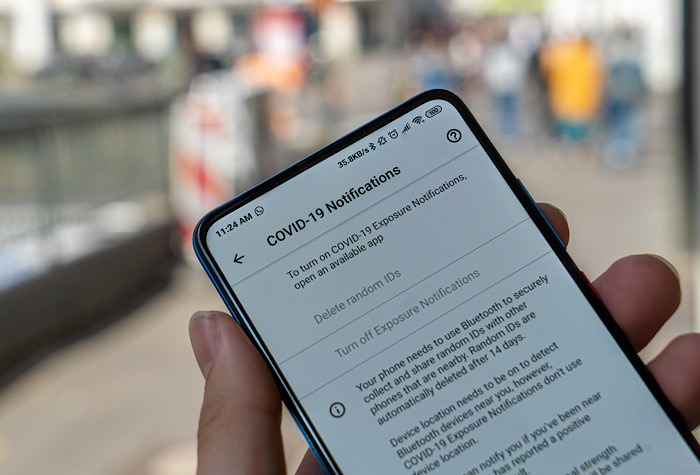
When the world became paralyzed during the COVID-19 pandemic more than a year ago, the tech world jumped up to help. Google and Apple each developed contact tracing apps meant to alert you to possible COVID-19 contact, promising privacy. While it appears Apple kept its promise, researchers have found a privacy flaw in the Android contact tracing app.
Contact Tracing App Privacy Flaw Discovered
The idea behind both contact tracing apps is that they will use your location data to alert you if you were in contact with someone with a known case of COVID.
The Android and Apple contact tracing apps have been downloaded by millions of users internationally. Individual countries and states have carried their own versions of the app.
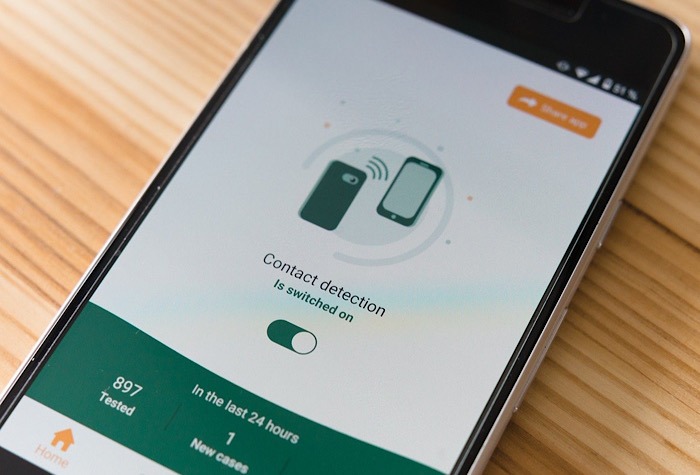
AppCensus researchers tested the apps through a contract with the U.S. Department of Homeland Security. While it found a privacy flaw in the Android contact tracing app, AppCensus says Google ignored it when it was presented with the issue in February of this year.
“This fix is a one-line thing where you remove a line that logs sensitive information to the system log. It doesn’t impact the program; it doesn’t change how it works,” said the co-founder and forensics lead of AppCensus, Joel Reardon. “It’s such an obvious fix, and I was flabbergasted that it wasn’t seen as that.”
Google, however, defended its actions. “We were notified of an issue where the Bluetooth identifiers were temporarily accessible to specific system-level applications for debugging purposes, and we immediately started rolling out a fix to address this,” Google spokesperson José Castañeda claimed in an emailed statement.

App Census doubled down, as co-founder and CTO Serge Egelman said Google repeatedly ignored the concerns brought to its attention. However, Castañeda, doubled down as well, saying the “roll out of this update to Android devices began several weeks ago and will be complete in the coming days.”
Why It’s Considered a Privacy Flaw
Reardon explained the issue with the Android contact tracing app is considered a privacy flaw because preinstalled apps have access to sensitive information collected by the contract tracing app and stored in system logs.
The contract tracing app exchanges anonymous Bluetooth signals with other devices with the app. T improve privacy, the signals are changed every 15 minutes, and a key that creates the signals is changed out every 24 hours.
The signals are saved in the system logs that preinstalled apps have access to as well. Those logs could contain the device’s name, MAC address, and advertising ID collected from the other apps.
“What Google is saying is that these logs never leave the device,” said Reardon. “They can’t make that claim – they don’t know if any of these apps are collecting the system logs.”
Reardon had reached out to Google once the privacy flaw was found in the Android contact tracing app to report it to Google’s bug bounty program. He received an email back stipulating the privacy flaw wasn’t enough for AppCensus to receive payment.
However, it seems somewhat heinous. Users worried about their physical safety are subjected to the prospect of a loss of data safety. Hopefully, Google really is working on this – users shouldn’t have to make such a choice.
Read on to learn how Safe Blues Virtual Virus was developed to track COVID.