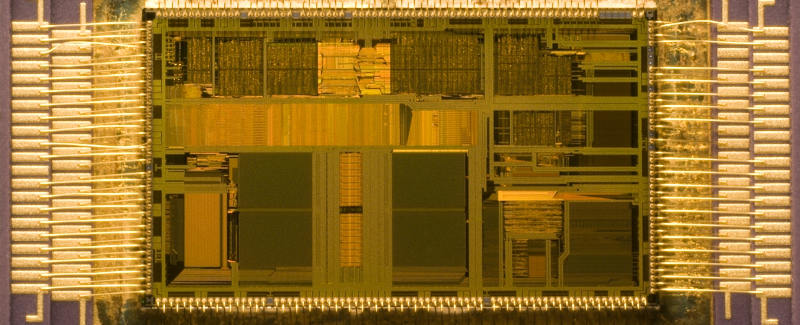
Using a computer, you usually expect that threats will come mostly at the software level. It doesn’t even cross our minds to think that the hardware itself can be a conduit to viruses and other sorts of nasty malware.
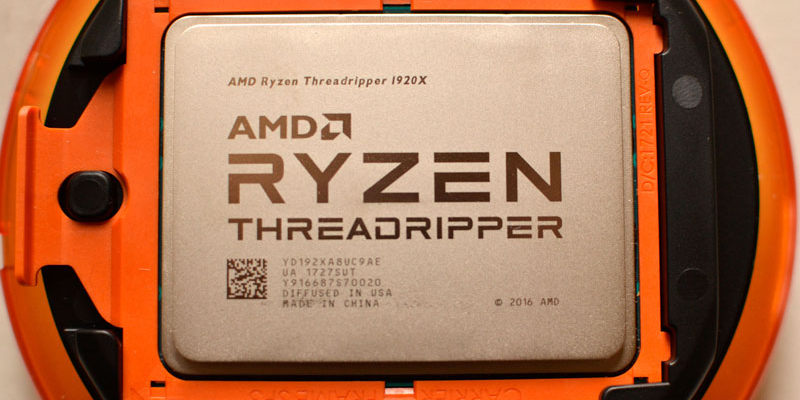
The truth is that hackers will take any chance they can get to infiltrate your system, and CPUs can play a role in that. At the beginning of 2018, Intel’s CPUs were revealed to have a set of vulnerabilities known as Meltdown and Spectre. Just a few months later on March 14 of the same year, another set of vulnerabilities in AMD’s latest line of processors was discovered by a company called CTS-Labs. This time, however, the way the reports were handled was a bit more unorthodox.
The Vulnerabilities

The list of thirteen vulnerabilities discovered by CTS-Labs can be seen summarized in this report.
They are grouped into four categories:
- Ryzenfall
- Fallout
- Masterkey
- Chimera
Each of these categories represents a method that the exploit would use to gain access to the secure area of the CPU’s processor that stores sensitive data like passwords and other credentials. Chimera appears to be the most powerful since it allows hackers to inject malicious code directly into the processor, rendering the entire system completely vulnerable to attack.
Even Microsoft’s new Credential Guard technology cannot protect against these types of attacks, meaning that the majority of software fixes are worthless unless AMD addresses them directly. In the case of Chimera, CTS-Labs assumes it “cannot be fixed and [requires] a workaround.“
“Producing a workaround may be difficult and cause undesired side-effects,” the company added.
It’s not absolutely clear what CTS-Labs means by a workaround, but I am guessing they mean either writing a new kernel-level driver that ignores a portion of the processor or making new CPUs that fix these vulnerabilities.
The other vulnerability categories, in combination with one another, can be used for industrial espionage by a hacker injecting persistent malware into the Secure Processor, according to their whitepaper.
A Few Oddities About this Release
CTS-Labs, up until they made this report, was pretty much a no-name security firm, so it’s important to take everything with a grain of salt. There are three other factors that raise my eyebrows about this particular company:
- They did not send AMD their report but instead chose to release it to the press. Original copies of the whitepaper are very difficult to find and are not disclosed entirely by the press. (Here is the whitepaper, by the way.) AMD also released a statement pointing out this particular behavior. “The company was previously unknown to AMD, and we find it unusual for a security firm to publish its research to the press without providing a reasonable amount of time for the company to investigate and address its findings,” the statement read.
- The website appears to have been a parked domain since 2012 until it became a more official-looking site on January 17, 2018. Their “About Us” page did not exist until the day before they released the whitepaper on a domain named “amdflaws.com.”
- An image has appeared on the Internet showing that the About Us is similar to that of Catenoid Security, a company that says it was once known as “Flexagrid Systems, Inc.” which is behind the CrowdCores adware. This may be nothing, though.
This isn’t to say that the information brought forward by CTS-Labs is invalid, but for the sake of transparency, these are some things that needed to be pointed out.
Should We Worry?
For those of you who are still planning to get a Ryzen chip, don’t let this report stop you. Yes, the processors may well be vulnerable to attack, but the hackers still depend on you to expose those vulnerabilities. Software intending to exploit the CPU still requires your administrative support. Now that we know how vulnerable both processor families are, it’s probably best to start being prudent about what applications you give root access to.
No, you won’t wake up one morning to the news that every system (including yours) was attacked by a CPU monster. Programs like these still require your approval to execute. CPU security measures are just meant to be failsafes, as ineffective as they are.
If you give an application root access to your computer, you’re going to have a bad time no matter what your CPU does in protest. There are tons of other ways to decimate your system with root access that do not involve getting into the machinations of the processor at all.
Does this make you more wary of getting a new CPU? Tell us all about it in a comment!