Passwords and device home buttons are on their way to becoming passé. Biometric scanning is taking over with the thought that while passwords can be stolen and hacked, fingerprints and your face can’t.
However, artificial intelligence researchers have just figured out a way to do it. They have used AI to develop fake fingerprints that they believe is a way to trick biometric ID readers.
Fake Fingerprint Research
Philip Bontrager of the New York University engineering school led a team of researchers to develop “DeepMasterPrints.” This research was presented in October at a Los Angeles, California, biometrics conference, and a report was published as well explaining the process.
The fake fingerprints could replicate more than one in five real fingerprints being used in a fingerprint recognition or face recognition system.
The report details that this process of creating fake prints would be similar to a “dictionary attack.” This is what happens in a hacking process when a dictionary list of words is used to put together possible password combinations. Instead of running through a dictionary of words, a system could run through several fake fingerprints to see if any matched.
One important point the researchers were able to utilize in their research is that many fingerprint scanners only read one portion of a fingerprint, and some portions of fingerprints have more in common than others.
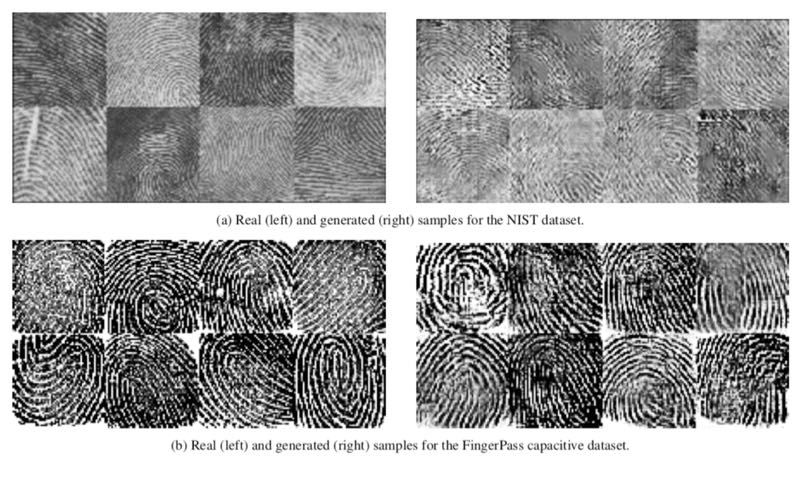
The researchers created the new prints by feeding a real set into a generative adversarial network. Because of what they learned about different portions of prints and what is read, they knew they only needed to create prints that matched the portions that are more likely to have something in common with others.
Bontrager doesn’t believe this could be used to break into your phone. “A similar setup to ours could be used for nefarious purposes, but it would likely not have the success rate we reported unless they optimized it for a smartphone system,” he said. “This would take a lot of work to try and reverse engineer a system like that.”
However, if a hacker tried to force their way into a system that had multiple fingerprint-accessible accounts, then they would have a good chance of being successful at breaking into a few of them.
Furthermore
You may be asking at this point why the researchers came forward with this, with something that hackers could use to exploit the system. The reason is that it’s meant as a type of warning.
“Without verifying that a biometric comes from a real person, a lot of these adversarial attacks become possible,” said Bontrager. “The real hope of work like this is to push toward liveness detection in biometric sensor.”

The researchers just want to push towards a greater awareness of it to be sure that device manufacturers make systems stringent enough to put something in place so that this isn’t possible.
However, it could end up being like the fight between government, hackers, and Apple regarding breaking into iPhones. After it was realized that even the government couldn’t break into the iPhone system, a system was developed that could break into it. Then Apple strengthened their system, only to have that be quickly broken as well.
So now that the researchers have called attention to it, maybe it will increase the desire of hackers to implement this new fake fingerprint process.
What do you think of the researchers announcing their findings that fake fingerprints can be used to trick biometric ID scanners? Let know know your thoughts and concerns in our comments section below.
Image Credit: Real and generated samples by Philip Bontrager, reprinted by The Guardian All others Public domain