You probably have heard of computer virus, malware, trojan horse and many other names that you know can cause great damage to your computer. However, you may not really know the differences between each and every one of them. With so many different types of security threats out there, it can be confusing for the layman that the easiest way is to classified everything as “virus”. In this article, we will discuss and explain the different type of security threats out in the Web, how to avoid these kinds of threats and how to remove them if they make their way into your computer.
Malware
Malware is short for malicious software. That means, any type of software that can harm your computer, including those we discuss below, is considered a malware.
Virus
Virus is a software program which replicates itself and infects all the computers it connects to. Viruses usually need to be executed through Autorun, system startup or manually by the user. The most common sources of virus infections are USB drives, the Internet and attachments in your emails. You should use a good antivirus all the time on your system to save yourself from viruses.
To prevent the virus spreading from your USB drive, you should make it secure before you use it on your own computer.
Spyware
As the name implies, spyware steals your information from the computer and sends it back to its creator. Some of the information captured by spyware includes credit cards detail, visited websites and their login credentials, email accounts etc.
Spyware will not harm your system. Most of the times, you won’t even notice its existence. The good thing is that most modern antivirus software also include an anti-spyware, so you don’t have to install additional anti-spyware software to safeguard your computer. Alternatively, you can also use dedicated anti-spyware software like Spybot search and destroy, Ad-aware, Super Antispyware etc.
Trojans/Backdoors
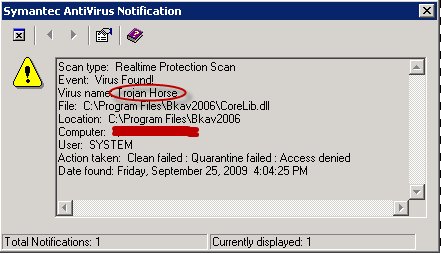
Trojans are one of the most damaging threats to a computer. Trojan is a malicious code hidden inside another seemingly useful software but will secretly connect to the malicious server in the background without your knowledge. Trojans are usually used to take complete control of the computer.
If your computer gets infected with a trojan, you should disconnect it from the Internet and don’t connect again until the trojan is removed completely.
Most outbound firewalls will be able to detect the suspicious activities of a trojan. Windows Firewall is a very basic firewall, you should go with an advanced firewall like ZoneAlarm and TinyWall.
Just remember that Trojans can’t install automatically like viruses. They need to be installed by the user. You should be very careful while installing or executing any programs. Only run the ones that you trust.
If you get infected with a Trojan, you can use Malwarebytes anti-malware tool to scan for and remove the threat.
Adware
Adware will serve advertisements on the computer which may or may not be closed/disabled by the user. Adware are not harmful, but they will keep showing advertisements on the computer, which can be rather annoying.
Adware are usually bundled with legitimate apps. The best way to prevent them from getting into your computer is to keep a close eye on the checked items for every app installation. Nowadays, mostly adware are installed as toolbars in your browsers. Uninstalling the toolbars will get rid of the adwares. You can also use multi-toolbar remover to remove multiple toolbars at once.
Scareware/Ransomware/Rogue apps
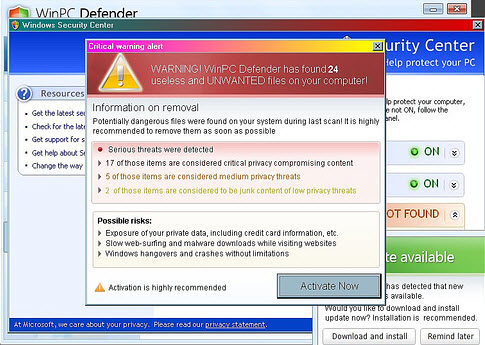
Scareware app will falsely pose itself as a legitimate app and scare the user into buying something useless. The most common disguise is antivirus software, where it “detects” that your computer is infected with many viruses. When you try to remove the viruses through the scareware, it will ask you to buy the full version before it can “clean” the system.
Most free and legitimate antivirus software will not ask you to buy the complete version in order to remove the viruses. If a software is asking for such paid upgrades, most probably it is a scareware app. Some examples of scareware are Microsoft Security Essentials Pro 2013, Windows Virtual Firewall, Internet Security 2012 etc.
Worms
Worms are the most damaging types of computer threat especially for computers connected in a network. They usually make use of security loopholes in a network to sneak inside every computer in the network without user intervention. They can (potentially) destroy all the computers in the network within a few minutes.
The main difference between a virus and a worm is that worm replicates itself from the network and they are a standalone program on its own, while viruses can spread through other means like removable media and they can attach themselves with other programs and executables in order to hide and run automatically upon the program’s execution. Some well known examples of worms are the famous “Iloveyou” and “conficker” worms.
If your network is plagued with a worm, you should disconnect all the computers from the network, scan each and every one of them with a good antivirus software. Only reattach them back to the network when you are sure that all traces of worms are eliminated, otherwise the worm will replicate itself again and the whole cycle restarts.
Exploit/Vulnerability/Flaw/Security hole/Bug
A vulnerability is a weakness that has been left by the developer of the software unknowingly and an exploit is a hack that attacks the vulnerability. No matter how well a software is coded, it bounds to have bugs and security holes. The only way to prevent exploits is to keep the system and the software up-to-dated, or switch to another software that doesn’t come with the vulnerability.
Staying safe from all threats
The same old rules apply:
- Always keep your system up-to-date and make sure you have the latest versions of all installed software.
- Always have a good real-time antivirus guard your system
- Always have a good firewall which can work with both outbound and inbound traffic. Keep an eye on the flow of traffic from and to your computer through the firewall.
- Be cautious when opening suspicious websites, links and attachments in email.
- Avoid using pirated software.
And last of all, always back up your computer regularly.
Did I miss out anything? Comments below.
Image credit: virus, BKAV is detected as malware, Malware, Virus Computer Security Focus as a Background







