Are you worried that your Linux computer may be infected with malware? Have you ever checked? While Linux systems tend to be less susceptible to malware than Windows, they can still be infected. Many times they’re less obviously compromised, too.
There are a handful of excellent open-source tools to help you check if your Linux system has been the victim of malware. While no software is perfect, these three have a solid reputation and can be trusted to find most known threats.
1. ClamAV
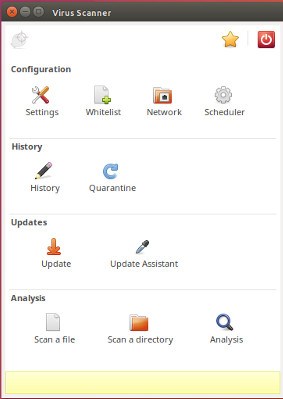
ClamAV is a standard anti-virus and will probably be the most familiar to you. There is actually a Windows version of ClamAV too.
Install ClamAV and ClamTK
ClamAV and its graphical front end are packaged separately. That’s because ClamAV can be run from the command line without the GUI, if you choose. Even still, the graphical interface ClamTK is easier for most people. The following is how to install it.
For Debian and Ubuntu-based distro:
sudo apt install clamav clamtk
You can also find clamav and clamtk in your distro’s package manager if you are not using Ubuntu based distro.
After both programs are installed, you have to update its virus database. Unlike everything else with ClamAV, that has to be done as root or with sudo.
sudo freshclam
There’s a chance that freshclam is being run as a daemon. To run it manually, stop the daemon with Systemd. Then, you can run it normally.
sudo systemctl stop clamav-freshclam
It’ll take some time, so just let ClamAV take care of things.
Run Your Scan
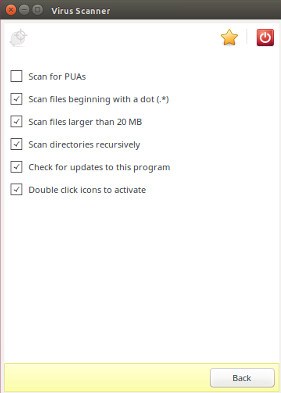
Before you run your scan, click the “Settings” button and check off “Scan files beginning with a dot,” “Scan files larger than 20 MB,” and “Scan directories recursively.”
Go back to the main menu and click “Scan A Directory.” Select the directory that you want to check. If you want to scan the whole computer, select “Filesystem.” You may need to rerun ClamTK from the command line with sudo in order for that to work.
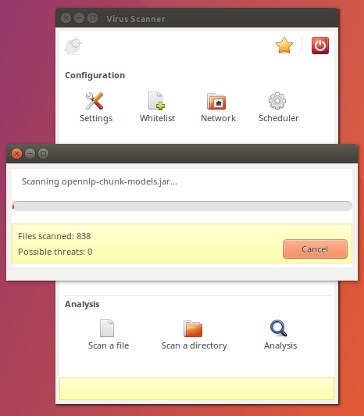
After the scan completes, ClamTK will present you with any discovered threats and allow you to choose what to do with them. Deleting them is obviously best, but may destabilize the system. This comes down to a judgement call for you.
2. Chkrootkit
The next scan to install is Chkrootkit. It scans for a type of malware specific to Unix-like systems like Linux and Mac – the rootkit. As the name suggests, the aim of rootkits is to gain root access on the target system.
Chkrootkit scans system files for signs of malicious alterations and checks them against a database of known rootkits.
Chkrootkit is available in most distribution repositories. Install it with your package manager.
sudo apt install chkrootkit
Check For Rootkits
This one is very easy to run. Just run the command as root or with sudo.
sudo chkrootkit
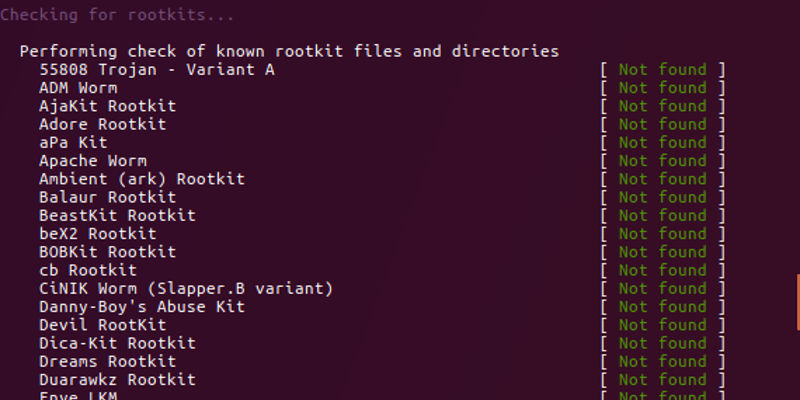
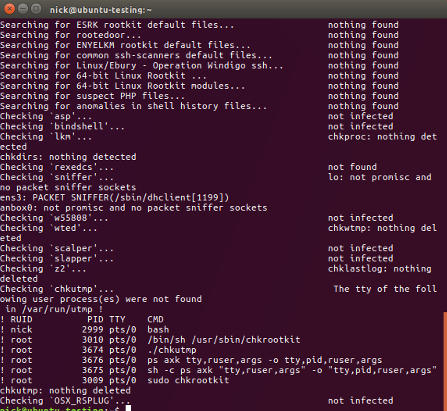
It’ll run down a list of potential rootkits very quickly. It might pause for a while on some while it scans through files. You should see “nothing found” or “not infected” next to each one.
The program doesn’t give a final report when it finishes, so go back through and manually check that no results turned up.
You can also pipe the program into grep and look for INFECTED, but that won’t catch everything.
Known False Positives
There’s a strange bug with Chkrootkit that reports a false positive for Linux/Ebury – Operation Windigo. This is a long-known bug caused by the introduction of a -G flag into SSH. There are a couple of manual tests you can run to verify that it is a false positive.
First, run the following as root.
find /lib* -type f -name libns2.so
It should turn up nothing. Next, check that the malware isn’t using a Unix socket.
netstat -nap | grep "@/proc/udevd"
If neither command turns up any results, the system is clean.
There also appears to be a fairly new false positive for tcpd on Ubuntu. If it does return a positive result on your system, investigate further, but be aware that the result could be incorrect.
You also may encounter entries for wted. Those can be caused by corruption or logging errors on system crashes. Use last to check to see if the times line up with reboots or crashes. In those cases the results were probably caused by those events and not malicious activity.
3. Rkhunter
Rkhunter is yet another tool for searching out rookits. It’s good to run both Chkrootkit on your system to ensure that nothing slipped through the cracks and to verify false positives.
Again, this one should be in your distribution’s repositories.
sudo apt install rkhunter
Run Your Scan
First, update rkhunter’s database.
sudo rkhunter --update
Then, run your scan.
sudo rkhunter --check
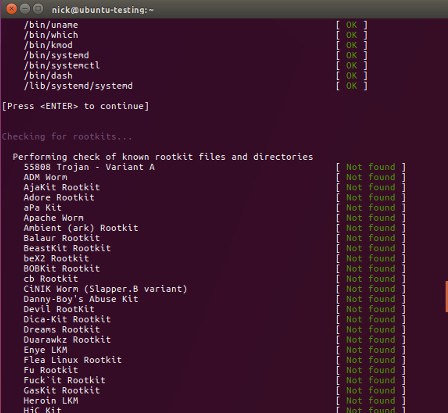
The program will stop after every section. You will probably see some warnings. Many arise because of sub-optimal configurations. When the scan finishes, it’ll tell you to take a look at its full activity log at /var/log/rkhunter.log. You can see the reason for every warning there.
It also gives you a complete summary of its scan results.
Closing Thoughts
Hopefully, your system turned up clean. Be careful and verify any results you receive before doing anything drastic.
If something is legitimately wrong, weigh your options. If you have a rootkit, back up your files and format that drive. There’s really no other way.
Keep these programs updated and scan regularly. Security is always evolving and threats come and go. It’s up to you to stay up to date and vigilant.